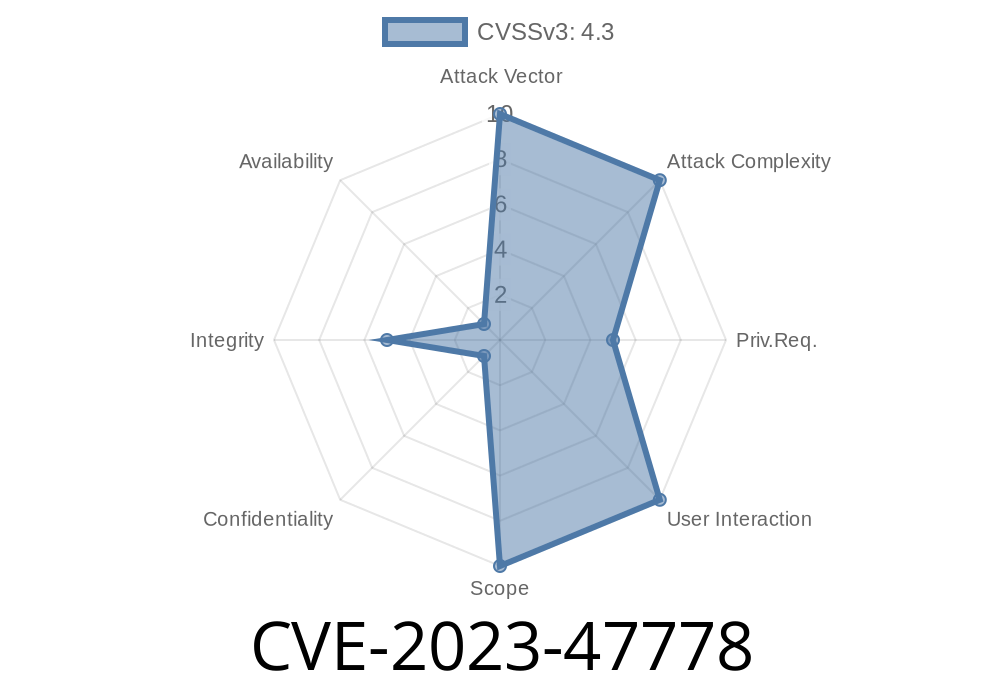
A new vulnerability, identified as CVE-2023-47778, has been discovered in the WordPress plugin LuckyWP Scripts Control, affecting versions up to 1.2.1. This weakness allows unauthorized users to exploit incorrect access control settings and potentially execute scripts, leading to significant security risks. If you use this plugin or manage sites that do, you absolutely need to understand how this vulnerability works and how to secure your site.
In this post, we’ll break down the vulnerability in simple terms, show you how attackers might exploit it with code examples, provide links to original references, and share steps to protect your site.
What is LuckyWP Scripts Control?
LuckyWP Scripts Control is a popular WordPress plugin that lets site administrators easily add custom CSS and JavaScript to their sites. It is widely used for tweaking website’s appearance or adding features without editing theme files.
What’s the Problem? (CVE-2023-47778 Details)
The issue is a missing authorization check in how LuckyWP Scripts Control handles access to certain plugin actions or settings. An attacker can exploit this by directly calling plugin endpoints intended only for admins. If access controls are misconfigured—or in this case, missing—an attacker can add arbitrary code, including malicious JavaScript.
The problem specifically impacts all versions from the beginning up to version 1.2.1.
Step 1: How the Plugin Should Work
Normally, only logged-in administrators are allowed to add or edit scripts via the plugin. That means only trusted users should ever be able to change these settings.
Step 2: What Went Wrong
Due to the missing authorization, the plugin doesn't verify _who_ is calling its functions.
Let’s say the plugin has an AJAX function like this in PHP
// Example vulnerable AJAX handler in the plugin.
add_action('wp_ajax_luckywp_add_script', 'luckywp_add_script_handler');
function luckywp_add_script_handler() {
// MISSING: if ( !current_user_can('manage_options') ) { wp_die(); }
$script = $_POST['custom_script'];
update_option('luckywp_custom_scripts', $script); // Writes script to the site
echo 'Script added!';
wp_die();
}
Notice there’s no check like current_user_can('manage_options') to ensure only admins can use this.
An attacker (even if NOT logged in) can send a direct POST request to the AJAX endpoint
curl -X POST https://vulnerable-site.com/wp-admin/admin-ajax.php \
-d "action=luckywp_add_script&custom_script=<script>alert('XSS')</script>"
This request injects a malicious JavaScript into the site. Now, every user who visits the site might be exposed to an XSS attack, session hijacking, or further compromise.
Original References
- Wordfence Threat Intelligence, LuckyWP Scripts Control Vulnerability
- Crafted Nuclei Template Reference
- CVE-2023-47778 at cve.org
1. Update the Plugin
If you use LuckyWP Scripts Control, update to the latest version immediately. The developer has released a patch fixing the missing authorization issue.
If you cannot update for some reason, add an authorization check in all plugin handler functions
if ( !current_user_can('manage_options') ) {
wp_die('Unauthorized access');
}
Limit admin user accounts.
- Use a firewall plugin like Wordfence.
Conclusion
CVE-2023-47778 is a clear reminder that even simple plugins can introduce big risks if they skip basic authorization checks. Never assume your favorite plugin is safe by default—always keep plugins up-to-date, review your permissions, and stay alert for new CVEs.
If you run LuckyWP Scripts Control or sites for others, act now to patch this bug to avoid becoming a victim of an avoidable hack.
Stay secure!
*This was an original, plain-language explanation by an AI. Please check the official references and stay updated with security advisories.*
Timeline
Published on: 01/02/2025 15:15:20 UTC