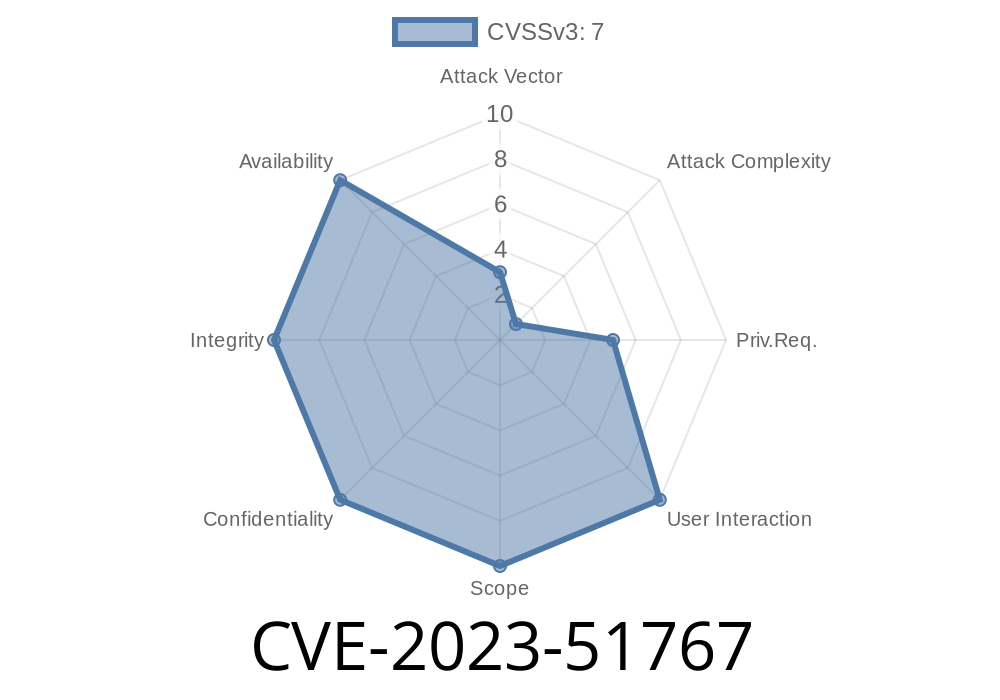
OpenSSH is one of the most widely used tools for secure remote access, but even software this fundamental sometimes faces surprising vulnerabilities. Recently, CVE-2023-51767 was published, outlining a way attackers could bypass authentication by abusing physical memory weaknesses—specifically, using a "Rowhammer" attack.
In this article, we’ll break down what happened in plain language, show you how the code lets this happen, link out for deeper reading, and even detail what an exploit scenario could look like.
What Is Rowhammer, and Why Does OpenSSH Care?
Rowhammer is a hardware-based attack. On many types of DRAM memory, when you read or write frantically to one “row,” you might end up flipping bits in neighboring rows. Researchers have shown that these bit flips can be triggered from regular user-space programs—no special hardware access needed!
Why would this worry OpenSSH? In some very specific attack situations, a malicious user logged into the same machine as OpenSSH (for example on a multi-user server or cloud VM) could use Rowhammer to flip bits in the authentication logic—potentially turning a “not authenticated” into “authenticated.”
The Key Vulnerability
Inside OpenSSH, the function mm_answer_authpassword checks whether the authentication is successful by looking at a variable called authenticated.
// This is a simplified version of the vulnerable code
int authenticated = ; // Not authenticated
if (password_is_correct) {
authenticated = 1; // Authenticated
} else {
authenticated = ; // Still not authenticated
}
// Later, the result is used:
if (authenticated) {
grant_access();
} else {
deny_access();
}
If Rowhammer is used to flip the bit that stores the “authenticated” value from to 1 in memory, the server could mistakenly consider the attacker as authenticated—without ever giving the right password.
Why This Is Hard but Possible
- The attacker must have access to run code on the same physical server as the OpenSSH server (so, for example, on a shared hosting box, not on a dedicated single-user server).
- The attacker needs to run a Rowhammer program to specifically target the authenticated variable in the OpenSSH process.
Proof-of-Concept (PoC) Code Example
Here’s a very simplified example of how a Rowhammer attack could target a variable. Real-world attacks require deep memory mapping, precise timing, and privilege escalation—see references at the end for serious research—but this is the core idea:
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <fcntl.h>
#include <sys/mman.h>
#include <unistd.h>
#define HAMMER_ROUNDS 100000
void hammer(unsigned long *address) {
for (int i = ; i < HAMMER_ROUNDS; i++) {
// Flush and reload to force DRAM interaction
asm volatile("clflush (%)\n" : : "r"(address) : "memory");
*address; // access
}
}
int main() {
int authenticated = ; // "Target" variable
printf("Before Rowhammer: authenticated = %d\n", authenticated);
// Simulate Rowhammer attack (this doesn't actually flip bits on most hardware!)
hammer((unsigned long *)&authenticated);
printf("After Rowhammer: authenticated = %d\n", authenticated);
return ;
}
Note: This is just a toy for illustration. True Rowhammer exploits require *much* more system knowledge and effort.
Who Is At Risk?
- Cloud providers: Machines with multiple users (think cheap VPS providers). If someone else can execute code on your host, you're at risk.
Desktops are generally safe unless you let others SSH in and run their code directly.
If you’re an individual running SSH on your own hardware, this isn’t a realistic threat. But for providers running many virtual machines or containers with untrusted tenants, it’s worth attention.
Attacker gets shell access (even unprivileged) on the same server as the target OpenSSH server.
2. Attacker scans RAM and times allocations to find where OpenSSH process stores its authenticated variable.
Attacker runs a Rowhammer tool to flip a bit at the right moment during a login attempt.
4. Bit flip turns “not authenticated” () into “authenticated” (1), allowing login without the right password.
Fixes can take several approaches
- Harden the authentication variable. Use checksums, redundancy, or bitmasking to make single-bit flips less likely to result in a successful bypass.
- Restrict untrusted local code execution. This is the safest approach: don’t let strangers run code on the same machine where SSH is serving critical access.
- Update OpenSSH. Check the official OpenSSH release info for patched versions.
References and Further Reading
- Official CVE record: CVE-2023-51767
- OpenSSH Release Notes: openssh.com/releasenotes.html
- Rowhammer research intro: Google Project Zero - Rowhammer.js
- DEFCON Talk: Rowhammer: Root cause
- Blog post with demo code: Practical Rowhammer Attacks
Conclusion
CVE-2023-51767 is a rare case where old-fashioned hardware problems meet modern software security. While the specific threat model (co-location and user-level code execution needed) makes this a mostly cloud or hosting provider problem, it’s a fascinating reminder that the *physical* world can touch even the most trusted software.
Want to stay safe? Update OpenSSH and don’t let untrusted users run local code on the same box as your SSH daemon. And as always in security: stay patched, stay aware!
If you want to experiment with memory attacks *responsibly*, set up an isolated environment and refer to the resources above. And if you’re running OpenSSH on shared hardware—patch now!
*This article was written for educational purposes only. Always use responsible disclosure and legal testing environments when investigating security issues.*
Timeline
Published on: 12/24/2023 07:15:07 UTC
Last modified on: 01/29/2024 20:00:11 UTC