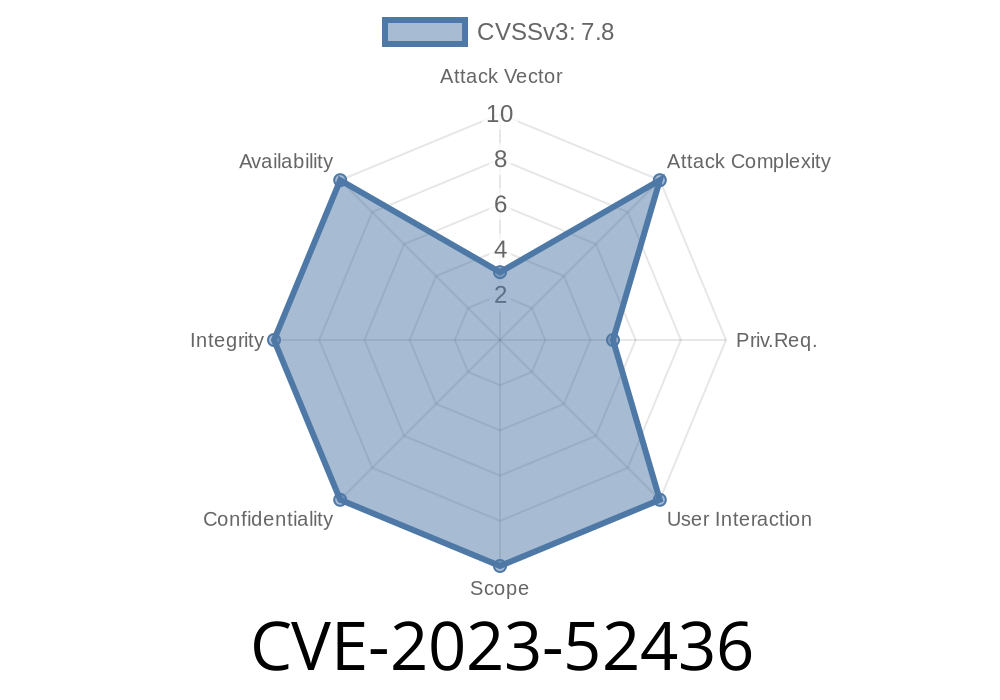
In early 2024, the Linux community addressed a subtle but significant vulnerability identified as CVE-2023-52436. This issue affected the f2fs (Flash-Friendly File System) in the Linux kernel, specifically relating to how extended attribute (xattr) lists were handled. The flaw lay in the assumption that unused space in xattr areas was always safely zeroed out, which, as it turned out, wasn’t always true. Without proper null-termination, attackers could abuse this to read or write unintended memory, possibly leading to leaks, data corruption, or privilege escalation.
In this long read, we’ll break down the exploit, the fix, and why this matters for Linux administrators and kernel developers.
What is f2fs and xattr?
f2fs stands for “Flash-Friendly File System.” It's designed for NAND-flash memory storage devices. One important feature is xattr (extended attributes), which let you attach arbitrary name/value pairs to files and directories—think labels, security policies, or access controls.
The kernel keeps xattrs in a list, and this list is supposed to be null-terminated (ending with a special ‘\’ or zero byte) to mark its conclusion.
The Bug Explained
Before the patch for CVE-2023-52436, f2fs would sometimes not explicitly null-terminate the xattr list when you set an xattr. Instead, it trusted that any extra space in the xattr area was already all zeros—a dangerous assumption.
If an attacker managed to fill the area with non-zero data, say through file system corruption or crafted operations, the xattr list’s “end marker” wouldn’t exist. Functions parsing the xattr list could run off the end, reading or writing data they’re not supposed to.
Here's a simplified snippet from before the fix
// Copy new xattrs into a buffer, but no explicit '\' at the end
memcpy(buffer, xattr_data, xattr_len);
// Assumed: unused space is already zeroed
If buffer had leftover junk, no null would mean “keep reading!”
The Patch
The fix is both simple and crucial: explicitly write a null byte at the end of the new xattr list.
memcpy(buffer, xattr_data, xattr_len);
buffer[xattr_len] = '\'; // Explicitly null-terminate
Now, even if the area wasn’t zeroed, the xattr list will properly end, making it safe for the kernel to parse.
Patch Reference
- Linux kernel mailing list commit
- CVE-2023-52436 in NVD
How Could This Be Exploited?
Note: Exploiting kernel bugs is advanced and dangerous—don’t run untrusted code on your machines!
Mount the image on a vulnerable kernel.
3. Set a new xattr that relies on parsing that area, causing the kernel’s xattr parser to read past the bounds.
Leak information back (e.g., via file reads) or even attempt to overwrite adjacent metadata.
In more complex exploits, parsing past the buffer could allow tricking the kernel into misinterpreting file permissions or attributes—sometimes leading to privilege escalation.
Proof-of-Concept Outline (for educational purpose only)
# Pseudo-code
# 1. Create f2fs image with non-zeroed xattr area.
# 2. Mount and set xattr to trigger bug.
# 3. Observe kernel logs or crash.
# Dangerous! Don't run on production.
Conclusion and Recommendations
CVE-2023-52436 is a good lesson in security hardening: Don’t assume uninitialized memory is zero! In system programming, always be explicit, even with something as small as null-terminating a list.
Review areas where you rely on “zeroed” memory.
- Consider allocating/initializing buffers explicitly.
Further Reading
- f2fs Documentation (kernel.org)
- Extended attributes (xattr) explained (Wikipedia)
- The commit fixing CVE-2023-52436
- CVE-2023-52436 NVD entry
If you want to stay safe, patch early, patch often—and remember, even small code changes can have big consequences.
Timeline
Published on: 02/20/2024 21:15:08 UTC
Last modified on: 04/19/2024 17:36:10 UTC