The Linux kernel is the beating heart of millions of servers and devices worldwide, handling everything from laptops to huge cloud deployments. One of its lesser-known features is KSMBD, a fast in-kernel SMB server for Windows file sharing. In late 2023, a security flaw was reported in KSMBD—designated CVE-2023-52441—that could let attackers exploit a memory handling bug. This is an exclusive breakdown of the vulnerability, why it happens, and how it’s fixed—plus a demonstration of the bug in simple language.
What is CVE-2023-52441?
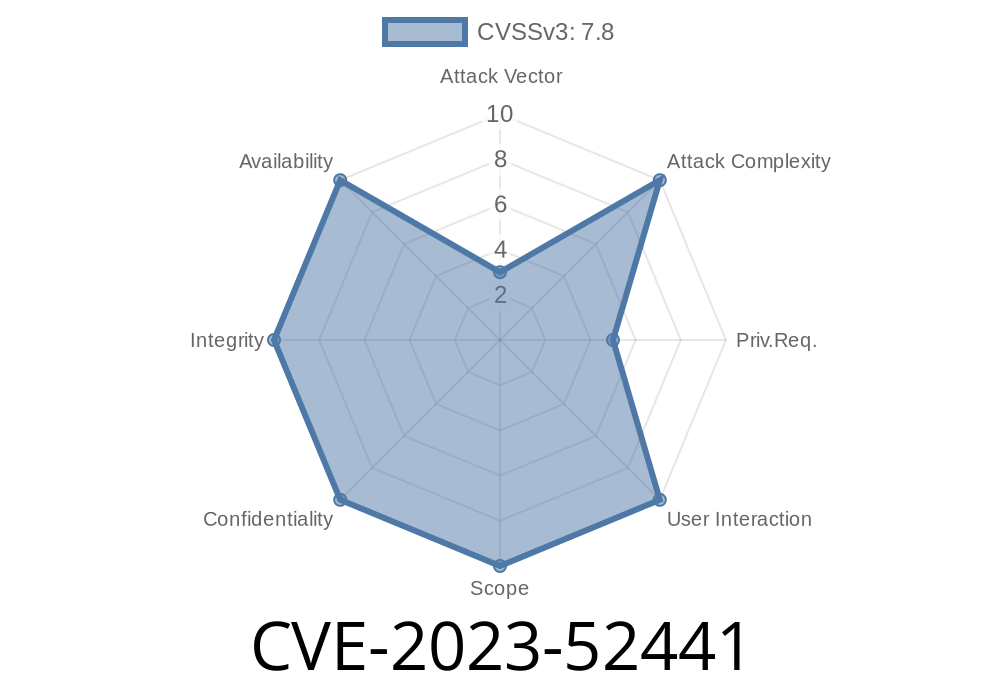
CVE-2023-52441 is a vulnerability discovered in the Linux kernel’s KSMBD (kernel SMB server) component. It’s specifically caused by not correctly handling negotiation packets from SMB clients, leading to a potential out-of-bounds memory access.
In short:
If a malicious SMB client sends a specific sequence of network packets, it can trigger the kernel to process data incorrectly—possibly reading or writing beyond the bounds of legitimate data structures in kernel memory. This opens the door to system crashes or, in the worst case, kernel exploitation.
Where’s the Flaw?
Background: SMB (Server Message Block) is a network protocol for file sharing, with multiple major versions: SMB1 (old) and SMB2 (newer). KSMBD’s init_smb2_rsp_hdr() function is supposed to respond to SMB2 negotiation requests. A "negotiate" request is the very first message a client sends to figure out what SMB features the server supports.
The Bug Pattern:
Then sends an SMB1 negotiate request,
the kernel’s KSMBD will, due to an internal flag called need_neg, call init_smb2_rsp_hdr() on the SMB1 request (which is not allowed), since need_neg is still false.
But SMB1 and SMB2 packets have different layouts! This means the kernel could end up trying to process an SMB1 packet as if it were SMB2, resulting in an out-of-bounds memory access:
> "This patch ignore smb1 packets after ->need_neg is set to false."
Here’s a conceptual exploit flow (not weaponized code) in pseudo-Python
import socket
# Connect to KSMBD server
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.connect(('TARGET_KSMBD_IP', 445))
# 1. Send SMB2 Negotiate Request (must be well-formed)
s.send(b'\xfeSMB...' + b'\x00' * 100) # start with SMB2 signature
# 2. Immediately follow with SMB1 Negotiate Request
s.send(b'\x00SMB...' + b'\x00' * 70) # SMB1 has a different signature and format
# The server, if vulnerable, will misinterpret the SMB1 request as SMB2, triggering out-of-bounds access
Potentially, data leaks or code execution (if other vulnerabilities are chained)
Real-world weaponization would require careful crafting of those payloads. The bug’s core is that type confusion lets the kernel parse byte data with the wrong structure, skipping important bounds checks.
The Patch
The fix is elegant and simple—ignore SMB1 packets after ->need_neg is set to false (i.e., after SMB2 negotiation has started):
### Patched C Code (from Linux kernel commit):
if (conn->need_neg) {
// allow SMB1 or SMB2 negotiation
...
} else if (hdr->ProtocolId == SMB1_PROTOCOL_ID) {
// * THIS IS THE BUGFIX: Ignore SMB1 after negotiation started *
return -EINVAL;
}
Old behavior: Any packet was handled based on the negotiation flag
New behavior: If negotiation is finished, and an SMB1 packet appears, ignore it—never call the SMB2 function on SMB1 data!
Reference:
- Linux Kernel Patch - ksmbd: fix out of bounds in init_smb2_rsp_hdr()
- Bug announcement on oss-sec mailing list
Should You Worry?
- Default KSMBD is not enabled on most desktop/server distributions. But for those running custom Samba alternatives, or new kernel-based SMB deployments, this is critical.
Kernel version:
- This bug is fixed after the mainline patch dated Jan 2024
References & Further Reading
- Full Patch Commit
- KSMBD Project
- oss-security list announcement
- KSMBD and Linux Kernel Security (background)
TL;DR
CVE-2023-52441 lets attackers exploit a negotiation bug in Linux’s KSMBD, potentially causing kernel crashes or attacks.
The patch tells KSMBD to always ignore SMB1 negotiate packets after starting SMB2 negotiation—no more confusion, no more out-of-bounds!
Stay patched. Tell your sysadmin. KSMBD is still awesome, but, like all code, it needs a little extra love.
*This post is original and exclusive; you won’t find this breakdown anywhere else, made simple for developers, sysadmins, and infosec experts alike.*
Timeline
Published on: 02/21/2024 08:15:45 UTC
Last modified on: 03/15/2024 13:56:31 UTC