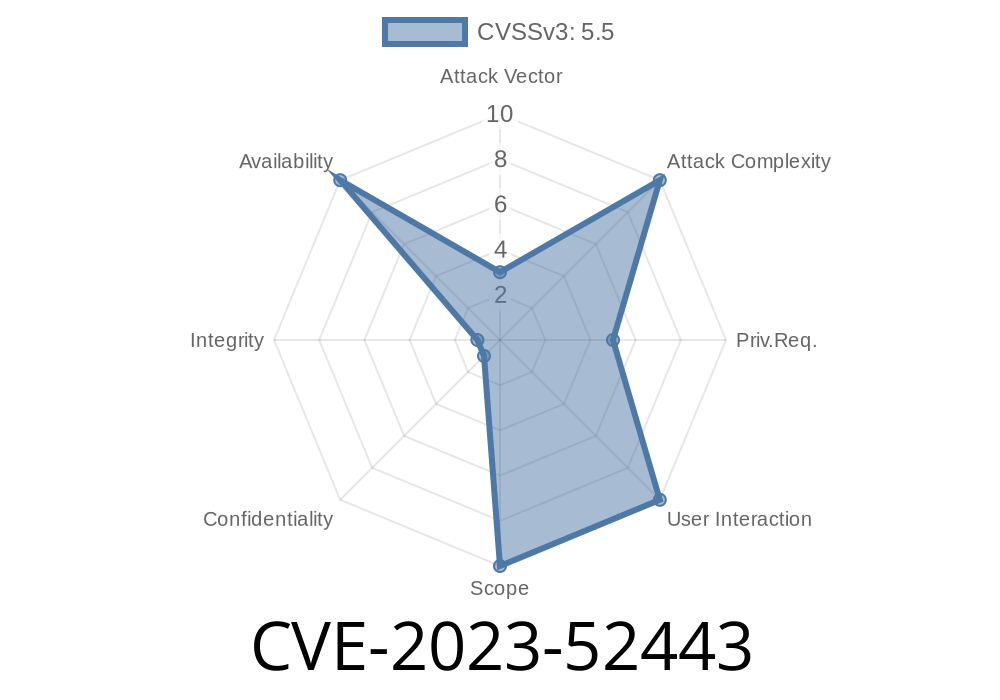
On December 2023, a critical bug was identified in the Linux kernel's AppArmor security module. Tracked as CVE-2023-52443, this vulnerability highlighted a subtle but dangerous issue when parsing profile names—specifically, when profile names were empty or malformed. This post provides a clear, exclusive walkthrough tailored for beginners and sysadmins: what the vulnerability is, how it can be triggered, potential impact, how it was patched, and practical code snippets that show the problem.
What is AppArmor?
AppArmor is a Linux kernel security module that confines programs to a limited set of resources. Profiles are written for programs, describing what files or capabilities they can access.
Certain profile strings, such as
"profile :ns::samba-dcerpcd /usr/lib*/samba/{,samba/}samba-dcerpcd {...}"
would unpack as a name like
":samba-dcerpcd"
This is an *empty profile* name with only a namespace, which wasn't supposed to happen.
It returns NULL for the profile, something for the namespace.
- Later, aa_alloc_profile() expects a real profile name. It gets NULL, tries to use it, and triggers a kernel crash (General Protection Fault / NULL pointer dereference).
Here's what happens in the kernel log
general protection fault, probably for non-canonical address xdffffc000000000: 000 [#1] PREEMPT SMP KASAN NOPTI
KASAN: null-ptr-deref in range [x000000000000000-x0000000000000007]
CPU: 6 PID: 1657 Comm: apparmor_parser Not tainted 6.7.-rc2-dirty #16
...
RIP: 001:strlen+x1e/xa
...
Call Trace:
? strlen+x1e/xa
aa_policy_init+x1bb/x230
aa_alloc_profile+xb1/x480
unpack_profile+x3bc/x496
...
When the code tries to strlen(NULL), boom—it crashes the kernel!
Here's a simplified reproduction in pseudo-C (not wartime code, but close enough for our example)
char* fqname = ":samba-dcerpcd";
char* namespace = NULL;
char* profilename = NULL;
void aa_splitn_fqname(const char *name, char ns, char profile) {
char *colon = strchr(name, ':');
if (colon) {
*ns = strdup(colon + 1);
*profile = NULL; // Since nothing after colon
} else {
*ns = NULL;
*profile = strdup(name);
}
}
void aa_alloc_profile(const char *profile_name) {
if (!profile_name) {
// This would normally crash when strlen is called on a NULL pointer
printf("Crash! profile name is null!\n");
exit(1);
}
// ... normal allocation
}
int main() {
aa_splitn_fqname(fqname, &namespace, &profilename);
aa_alloc_profile(profilename); // This causes crash
}
In the real kernel code, the call to strlen(profile_name) in aa_policy_init() leads to the panic.
Attack Scenario
1. Malicious AppArmor Profile: An attacker (or perhaps a careless admin) feeds a whitespace or malformed AppArmor profile with only a namespace to the system:
`plaintext
echo 'profile :attack-ns::bad-profile /bin/bash {...}' > /sys/kernel/security/apparmor/policy
`
2. Kernel Panic: The AppArmor parser (run as root) tries to parse this entry. The kernel crashes due to the vulnerability ("null pointer dereference").
Impact
- Denial of Service: Any unprivileged user able to supply AppArmor profiles (usually root, but also privileged containers) can crash the host kernel.
- System Unstable: Triggers a direct kernel panic, possibly bringing down critical infrastructure or cloud hosts.
What changed in the patch?
The kernel maintainers added a check: if a profile name is NULL after parsing, immediately error and bail out with a clear message (EPROTO error).
Relevant Patch Snippet (commit link):
if (!name) {
audit_log(NULL, GFP_KERNEL, AUDIT_APPARMOR_USER, "empty profile name not allowed");
return -EPROTO;
}
Now, if you try to load an empty or malformed profile name, the kernel says NO and continues safely.
How Can I Stay Safe?
- Patch your kernels! Make sure you are running with at least the kernel containing this fix.
Only trusted users should have access to load AppArmor profiles.
- For more info, see the LVC report.
References
- CVE-2023-52443 at Linux Kernel Archive
- Patch commit
- AppArmor upstream wiki
- Original bug report by Linux Verification Center (linuxtesting.org)
Conclusion
CVE-2023-52443 is a strong reminder that even small parsing mistakes in security-critical software can lead to complete system crashes. As Linux hardens, these edge cases become important. Update your systems and, when writing or loading AppArmor profiles, always check for bad or empty names!
Timeline
Published on: 02/22/2024 17:15:08 UTC
Last modified on: 03/14/2024 20:16:02 UTC