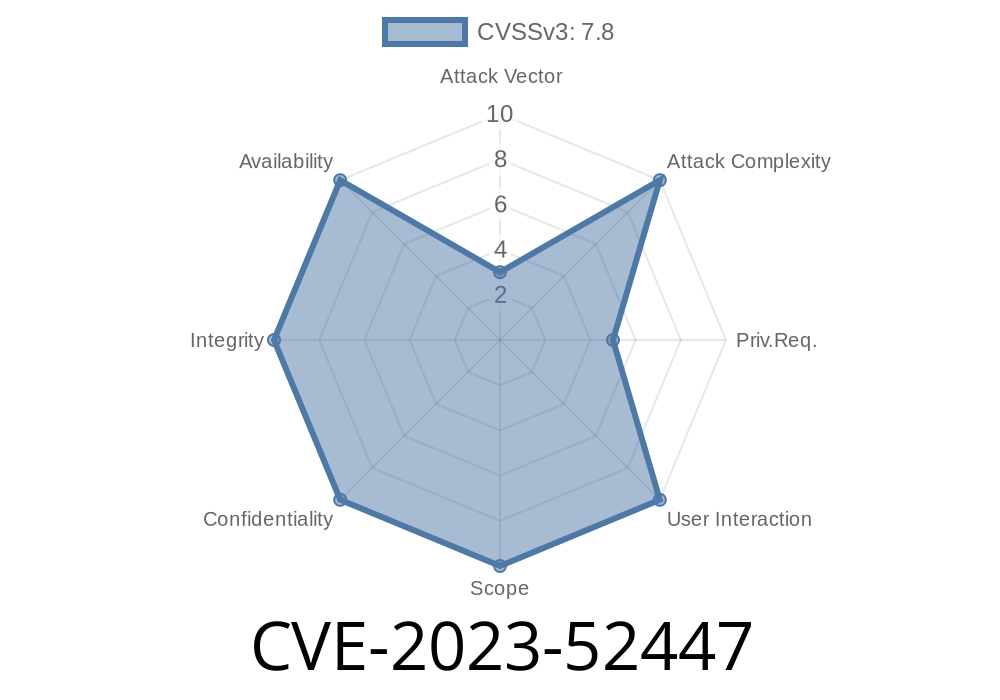
CVE-2023-52447 highlights a use-after-free (UAF) security issue in the Linux kernel's eBPF (extended Berkeley Packet Filter) subsystem, specifically affecting how nested (inner) maps are freed. In normal words, a UAF means that a piece of memory is used *after* it was supposed to be released. This problem could let attackers take control, crash your system, or leak sensitive data.
This post will break down what happened, show snippets of affected code, and explain how the vulnerability can be exploited — all in plain English.
What is BPF and What are Inner Maps?
eBPF is a technology that lets programs safely run inside the Linux kernel — it’s used for monitoring, security, and networking.
Often, BPF maps are used to share data between kernel and user-space or among BPF programs. Sometimes, a map can contain another map as a value, and we call this an “inner map.”
The Bug: Unsafe Freeing of Inner Maps
When you delete or update an inner map, the system should make sure no one is still using it before actually destroying its memory. Normally, Linux uses tricks like RCU (Read-Copy Update) so programs can keep running while these changes happen safely.
But in this case, the code would sometimes free an inner map right away — without checking if it was really safe. That's risky because another program might still be using that map right at that moment, leading to a use-after-free.
When you update or delete an inner map, the reference counter is decreased (with bpf_map_put()).
- If the counter reaches zero, ops->map_free() is called to actually free it — often in a worker thread.
- But most .map_free() operations don’t wait for current users to finish. There isn't a call to synchronize_rcu() or similar, so right after freeing, bad things can happen if another thread or program was still using the memory.
Here is a simplified version of the problematic code
void bpf_map_fd_put_ptr(struct bpf_map *map)
{
// Decrement map reference counter
if (atomic_dec_and_test(&map->refcnt)) {
// Free the inner map immediately
map->ops->map_free(map);
}
}
Problem: If the inner map is still being used, this code could free it too soon.
This is done using call_rcu() or call_rcu_tasks_trace().
- The fix uses a new rcu_head field in the BPF map (sharing space with an old work field to save memory).
Here’s how the deferred free looks
if (atomic_dec_and_test(&map->refcnt)) {
// Defer freeing, so it happens only after safe grace periods
bpf_map_free_deferred(map);
}
void bpf_map_free_deferred(struct bpf_map *map)
{
call_rcu_tasks_trace(&map->rcu_head, really_free_map);
}
void really_free_map(struct rcu_head *rcu)
{
struct bpf_map *map = container_of(rcu, struct bpf_map, rcu_head);
map->ops->map_free(map);
}
Now, freeing will wait until all ongoing users are done — preventing use-after-free.
How Could This Be Exploited?
- Trigger the bug: An attacker needs enough permissions to load BPF programs and update/delete maps.
- Time the access: By carefully timing their code, attackers can trick the kernel into freeing an inner map while they are still using it.
- Hijack memory: After the free, the old memory might get reused by something else; the attacker can then execute arbitrary code or crash the system.
Impact: Elevate privileges, crash the machine (DoS), break kernel isolation.
> Note: Exploiting this generally requires CAP_BPF, CAP_SYS_ADMIN, or similar permissions, but in some containerized or specialized setups, less-privileged users might still be able to trigger this.
## PoC/Exploitation Snippet
Actual public exploit code is not readily available (June 2024), but a skeleton looks like
// Pseudocode for demonstration only
int outer_map = create_outer_map();
int inner_map = create_inner_map();
update_map(outer_map, KEY, inner_map); // Insert inner map
// In parallel: keep running BPF programs accessing inner_map
delete_map_element(outer_map, KEY); // Decrement ref count, potentially triggers free
// Race condition: Access freed inner_map memory
A real exploit would involve heavy timing and knowledge of memory to take control reliably.
Good news: The Linux kernel team fixed this issue promptly. The fix landed in
- Upstream patch (see details)
Conclusion
CVE-2023-52447 is a textbook example of why careful memory management in the kernel *matters*. The bug let inner BPF maps be freed too soon, risking memory corruption or exploitation. The fix delays freeing until it’s truly safe.
This is another reminder: keep your kernel updated, especially if you use eBPF!
References
- Official Patch on kernel.org
- CVE Record
- Linux kernel bugzilla report
- bpf: Defer the free of inner map when necessary
Timeline
Published on: 02/22/2024 17:15:08 UTC
Last modified on: 03/14/2024 19:46:43 UTC