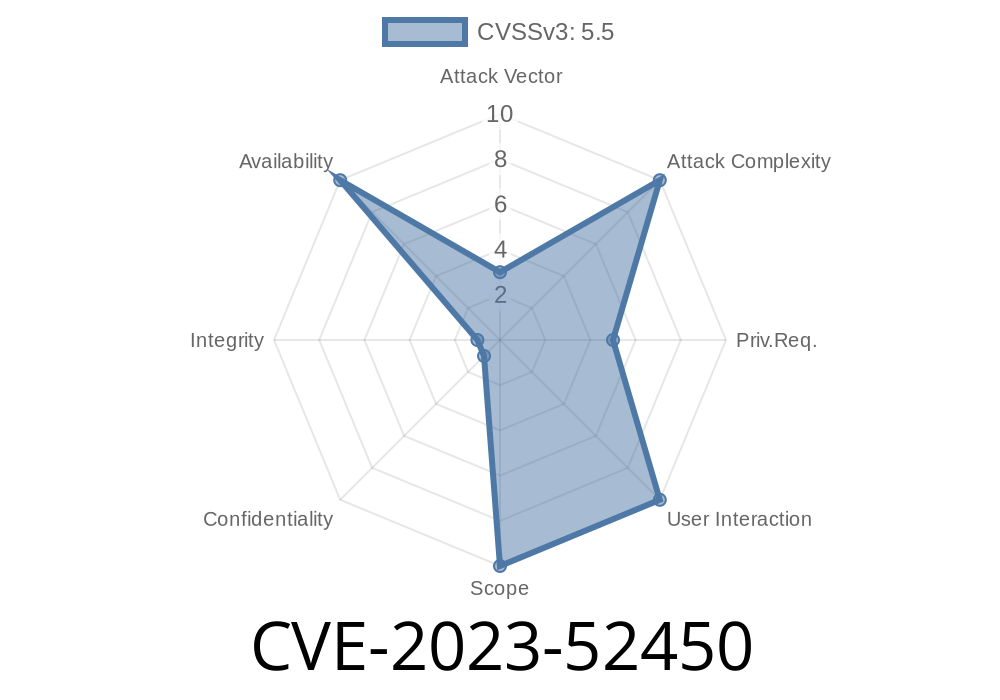
If you use Linux on Intel hardware, the security of your system depends in part on the kernel’s perf subsystem. In late 2023, a bug surfaced: CVE-2023-52450. This issue could cause a NULL pointer dereference in the kernel, potentially crashing affected machines. Today, I’ll break down this vulnerability in plain English, show you the broken and fixed code, and share resources if you want a deep dive.
What’s CVE-2023-52450?
This CVE refers to a vulnerability in the Linux kernel’s perf infrastructure, specifically the code responsible for tracking processor events on some Intel CPUs—known as the uncore code. The bug can allow code running with kernel privileges (or, in rare misconfigurations, a user with access to perf_event_open) to crash the kernel by causing a NULL pointer dereference.
discover_upi_topology() — gathers info about Intel’s UPI interconnect topology.
- upi_fill_topology() — fills out a topology array (for uncore events) based on what was discovered.
There, an index miscalculation causes code to access an array out-of-bounds, which can lead to reading or writing to NULL (or random memory), producing a kernel oops (crash).
Consider this line of C code, inside discover_upi_topology()
upi = &type->topology[nid][idx];
The code attempts to get information using a *physical* socket id. But the topology array is sized based on the *logical* (kernel-side) socket ids. On some platforms, physical and logical ids aren’t the same—so this pointer might point outside the array, or become NULL if there is a gap in socket numbering.
That dereference then leads to a crash here
static void upi_fill_topology(..., struct intel_uncore_type *type, ...)
{
struct upi_topology *upi = ...;
// upi may be NULL!
upi->foo = bar; // CRASH: dereference of NULL pointer
}
Vulnerable (before)
upi = &type->topology[physical_socket_id][idx]; // Wrong index
Patched (after)
upi = &type->topology[logical_socket_id][idx]; // Correct logical index
The difference: The fix ensures code always uses logical socket ids, which agree with the topology array’s real size.
Impact: Who Can Exploit This?
This bug is not directly remote or local privilege escalation. Typically, only kernel code or high-privilege users (like root or users with CAP_SYS_ADMIN) can trigger the vulnerable path.
But certain perf configurations (e.g., those that allow users to read hardware counters) could let local users *crash* the system, producing a denial-of-service. That’s a big problem for servers and shared computing environments.
A public proof-of-concept is not widely known, but here’s a simplified exploitation scenario
Requirements:
Steps
1. Write a small program or script that calls perf_event_open for UPI uncore events, targeting non-existent/invalid nid/idx values.
Sample pseudo-exploit (cannot crash all kernels, be cautious!)
#include <linux/perf_event.h>
#include <unistd.h>
// user must be root or have perf capabilities
// open upi events with improbable socket id to trigger bug
int main() {
struct perf_event_attr attr = {};
// ... fill attr for UPI ...
attr.type = PERF_TYPE_HW_CACHE; // Placeholder, real type needed
attr.config = ; // Needs to match UPI event
// Experiment with socket ids that are invalid
pid_t pid = -1;
int cpu = <cpu_on_invalid_physical_id>;
int fd = perf_event_open(&attr, pid, cpu, -1, );
// If vulnerable, kernel may crash here
return ;
}
Warning: Do NOT run on production. You may crash your kernel.
Patch and Mitigation
You are affected if you use Linux kernel 6.6 (or certain earlier versions with backports) on recent Intel hardware.
Fixed kernel versions:
- mainline commit
Linux 6.6.12 and later
Upgrade as soon as possible!
If you cannot upgrade, restrict unprivileged access to perf.
Original Fix Patch:
perf/x86/intel/uncore: Fix NULL pointer dereference issue in upi_fill_topology()
- CVE Record - CVE-2023-52450
- Linux perf subsystem docs
Conclusion
CVE-2023-52450 highlights why even small mismatches in indexing kernel data can have system-wide effects. All sysadmins and users of recent Intel Linux systems should ensure their kernel is updated. Denial-of-service bugs like this are the low-hanging fruit for attackers trying to disrupt availability!
*Got questions about patching, mitigation, or want to see the full gory code? Drop a comment below!*
Timeline
Published on: 02/22/2024 17:15:08 UTC
Last modified on: 03/18/2024 18:34:16 UTC