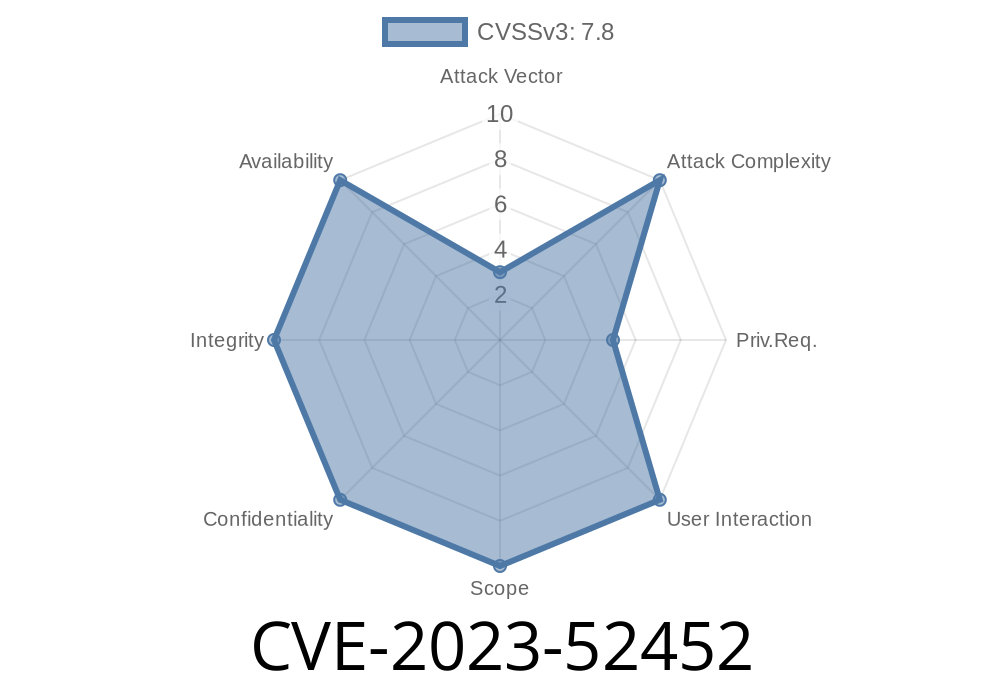
In early 2023, security researchers discovered a subtle yet potentially dangerous vulnerability in the Linux kernel relating to the BPF (Berkeley Packet Filter) stack memory handling. Officially tagged as CVE-2023-52452, this bug allowed privileged BPF programs to read from uninitialized stack slots in ways that the kernel developers didn’t fully anticipate. The flaw centered around inconsistent enforcement of stack slot access, resulting in a confusing set of behaviors where sometimes invalid reads were allowed, other times blocked — depending not on security factors, but on the arcane details of the kernel's stack tracking logic.
In this long read, we’ll break down exactly how the issue happens, discuss the core code changes that fixed it, provide an example of how one might exploit this as an attacker, and point to further reading for those interested in BPF security internals.
What is BPF and Why Do Stack Accesses Matter?
The Linux kernel’s BPF system lets user programs upload small, sandboxed bytecode to the kernel — commonly for things like tracing, networking, and security enforcement. To keep the kernel secure, a *verifier* checks every BPF program for unsafe actions before it’s allowed to run. Managing stack memory is one key part of this verification: BPF programs don’t control their own stack pointers directly, but instead, the kernel verifier tracks and restricts all stack accesses.
If there’s a bug in how the verifier tracks or limits those stack accesses — for instance, if it lets a program read data from an address in its stack frame that was never written to — you can get undefined behavior. In the best case, it’ll “just” confuse a tracing tool; in the worst case, carefully crafted reads might let privileged code see memory contents that could have privacy or security consequences.
The Vulnerability: Inconsistent Handling of Uninitialized Stack Slots
Let’s walk through what the kernel was doing wrong.
Since commit 6715df8d5, privileged (CAP_SYS_ADMIN) BPF programs _are supposed to be able to read uninitialized stack memory_. However, the kernel verifier was only sometimes letting them:
check_stack_range_initialized()
This meant that a BPF program could sometimes read from “never-written” stack slots, but only if it had already accessed adjacent memory, which didn't make sense from a security stance, and could create hard-to-diagnose bugs for BPF developers.
Additionally: There was another closely-related bug — when a stack write was done with a _variable_ offset (the exact stack address only known at runtime), the kernel wouldn’t always allocate enough stack. This could let a BPF program verify, but then run and attempt an out-of-bounds stack access, which should never happen in a correctly verified program.
The Patch: How the Problem Was Fixed
The patch that fixed this issue did a few major things:
Permitted Stack 'Growth' on Uninit Reads for Privileged Code:
The kernel now allows stack memory to "grow" dynamically if a privileged BPF program tries to read an uninitialized slot, instead of blocking the access.
Centralized Stack Size Tracking:
Instead of confusing code spread across several functions, the new approach consolidates all stack growth logic in grow_stack_state(). This ensures the stack’s real max size is tracked no matter how a program tries to access it, even with variable offsets.
Improved Testing:
Kernel BPF selftests were updated (or, in some edge cases, disabled) to reflect the new, sensible behavior.
Before (incorrect stack growth on variable index)
// Only fixed_offset used; variable offset ignored!
update_state_depth(state, reg->off);
...
// Unprivileged allowed, privileged sometimes blocked
if (!state->allocated_stack || slot < state->allocated_stack)
return -EACCES;
After (correct stack depth no matter offset)
// Now using calculated minimum possible register value!
grow_stack_state(state, min_possible_stack_offset);
...
// Stack always grown as needed for privileged reads
if (is_privileged)
grow_stack_state(state, requested_slot);
Threat Model: Privileged BPF Code Only
To be clear, this is *not* directly exploitable by unprivileged users. You need to be able to load BPF code as a *privileged* user (typically root or with CAP_SYS_ADMIN). However, in environments where privileged BPF frameworks load user-supplied code (for instance, in large datacenter eBPF infrastructures), it’s possible this bug could be leveraged for:
Information disclosure — reading stack memory that should have been inaccessible or undefined.
- Subtle verifier bypasses — programs that should be rejected, but pass because of incomplete stack allocation logic.
Sample Exploit: Reading Uninitialized Stack Data
Let’s imagine an attacker tries to read uninitialized stack data in their CAP_SYS_ADMIN BPF program on a kernel vulnerable to CVE-2023-52452. Here’s an artificial example in pseudo-C (via *bpftrace* syntax for clarity):
// Assume running as privileged BPF
tracepoint:syscalls:sys_enter_execve
{
// Write something to stack slot -x10
$buf = 1234;
// Now read from a much deeper (untouched) stack slot, say -x80
$val = *(uint64*)(ctx + -x80); // UNINITIALIZED READ!
printf("Leaked value at -x80: %d\n", $val);
}
- On a vulnerable kernel: this *might* succeed (or print a junk value), depending on stack allocation history.
- On a fixed kernel: this always dynamically grows the stack and consistently allows/disallows per privilege, no surprises.
Here’s a minimal C/BPF example that would fail to verify without the fix if VAR is nonzero
SEC("xdp")
int vuln_bpf_prog(struct xdp_md *ctx)
{
char buf[32];
int idx = ctx->data & x10; // variable offset
// variable stack write:
buf[idx] = x41;
// try to read uninitialized region:
char leak = buf[31];
bpf_printk("Leaked: %x\n", leak);
return XDP_PASS;
}
Prior to the patch, this might pass or fail the verifier depending on how idx is calculated.
- After the patch, stack is always grown to the necessary size, and privileged programs see consistent, secure behavior.
CVE Entry:
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2023-52452
Upstream Linux Kernel Patch:
Original commit 6715df8d5 ("bpf: Permit privileged mode to access uninitialized stack slots")
https://github.com/torvalds/linux/commit/6715df8d5
bpf-next mailing list discussion:
https://lore.kernel.org/all/20240215135246.2176597-1-alan.maguire@oracle.com/
BPF Verifier Internals:
https://www.kernel.org/doc/html/latest/bpf/verifier.html
If you run custom or third-party BPF code as root:
Ensure your kernel is updated with this fix, especially on shared/hosted environments.
If you write BPF programs:
Avoid reliance on uninitialized stack slots. This behavior is inconsistent, even for privileged code, and best practices are to always initialize before reading.
For security teams:
This flaw is *not* a privilege escalation, but may be relevant where attackers can submit BPF through orchestration, container, or custom in-kernel frameworks.
Conclusion
CVE-2023-52452 is a nuanced Linux kernel bug about how and when stack accesses are legal in privileged BPF code. The root problem was an inconsistent approach in the verifier, especially for uninitialized regions and when stack offsets are variable at runtime. The kernel’s fix makes the logic clearer, and safer — a good example of hardening in an area that’s easy to overlook, but important for robust kernel security.
Always keep your kernel up to date!
#### *If you found this writeup useful or want more real-word kernel security breakdowns, follow [@YourHandleHere] on Twitter/X.*
Timeline
Published on: 02/22/2024 17:15:08 UTC
Last modified on: 03/18/2024 18:24:33 UTC