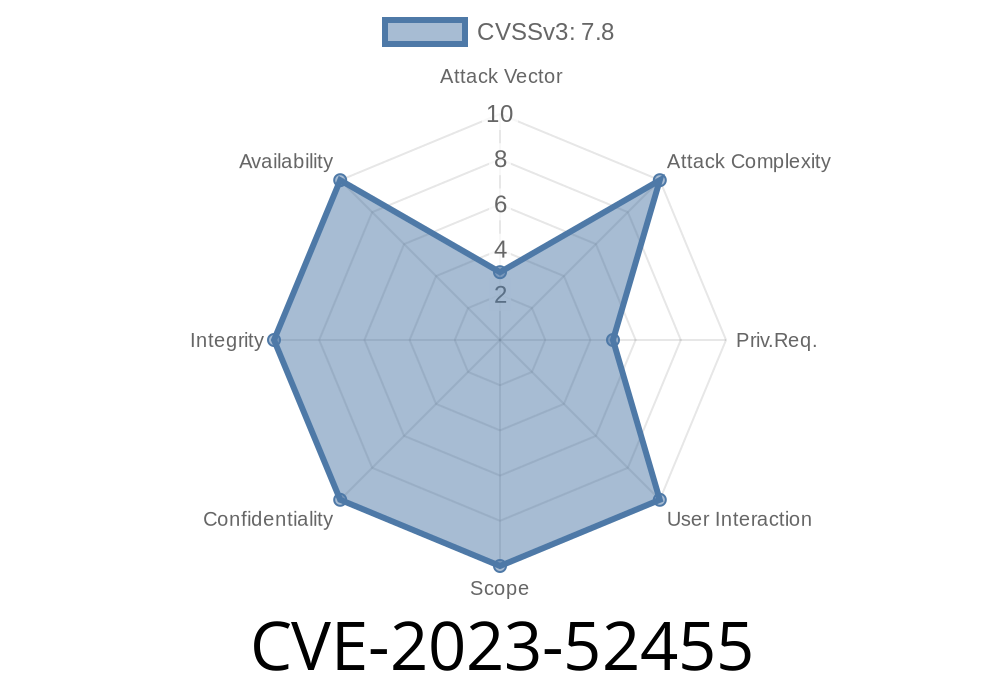
A newly resolved vulnerability, CVE-2023-52455, affected the Linux kernel's handling of IOMMU (Input/Output Memory Management Unit) address reservations. This bug could cause display driver failures and kernel memory corruption under certain conditions involving device bootloader/firmware configurations. In this detailed and straightforward post, we’ll break down the vulnerability, how it could be exploited, and how it was resolved in recent kernels.
Background: What Went Wrong?
To understand this vulnerability, we need to look at how the Linux kernel reserves memory with the IOMMU when initializing hardware devices—especially graphics displays. When the firmware or bootloader doesn't set up device framebuffers, both their address and size end up as in the device tree property "iommu-addresses".
Unfortunately, earlier kernel versions would *blindly* try to reserve an IOVA (IO Virtual Address) region even if the size was . This led to unintended consequences, as the kernel would insert invalid reservations into its tracking structures (rbtree), sometimes marking the entire IOVA space as reserved.
Kernel Data Structure Corruption:
The IOVA reservation involves the use of an rbtree in the kernel, tracking which IOVA regions are used. If a reservation with zero length is made (pfn_hi < pfn_lo), this rbtree structure gets corrupted.
Driver Failures:
If a display driver tries to map graphics memory but finds the entire virtual address space reserved, IOMMU mappings fail, effectively breaking the graphics device.
Potential Security Impact:
While this bug is more about reliability than direct attacker exploitation, any time a kernel data structure is corrupted, the risk of information leaks, denial of service, or harder-to-find vulnerabilities increases.
Exploit Scenario: Step-by-Step
1. Bootloader/Firmware Doesn't Set Up Framebuffers
Kernel Tries to Reserve IOVA Region
On boot, the kernel calls the function to reserve this address range—even though it has zero length.
rbtree Gets Invalid Entry
The kernel’s internal rbtree gets an entry where the end (high) PFN is less than the start (low) PFN, breaking the rbtree's assumptions.
Device Driver Fails
When drivers (like the display driver) try to allocate memory, mappings fail, causing loss of device functionality.
Here’s a simplified version of the problematic code
/* old Linux kernel code */
void iommu_reserve_region(struct iommu *iommu, phys_addr_t addr, size_t size)
{
//... some setup
struct iova_domain *domain = get_iova_domain(iommu);
/* Create reservation in iova_domain's rbtree */
reserve_iova_range(domain, addr >> PAGE_SHIFT, (addr + size - 1) >> PAGE_SHIFT);
//...
}
If addr and size are both , then the second argument (addr + size - 1) >> PAGE_SHIFT becomes a large number (due to wrapping), and the logic in the reserve_iova_range() function can break.
How It Was Fixed
Solution:
The fix adds a check in the kernel code: It skips reserving an IOVA region if the size is zero, and logs a warning for the firmware.
Here’s what the patched code might look like
/* fixed Linux kernel code */
void iommu_reserve_region(struct iommu *iommu, phys_addr_t addr, size_t size)
{
if (size == ) {
pr_warn("firmware requested -length IOVA region reservation. Skipping.\n");
return;
}
struct iova_domain *domain = get_iova_domain(iommu);
reserve_iova_range(domain, addr >> PAGE_SHIFT, (addr + size - 1) >> PAGE_SHIFT);
}
Patch:
- https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/commit/?id=47ebfe5da
CVE Announcement:
- https://nvd.nist.gov/vuln/detail/CVE-2023-52455
Discussion:
- https://lore.kernel.org/all/20240110131507.84668-1-manivannan.sadhasivam@linaro.org/
Update Your Kernel!
If you use Linux on platforms with IOMMU-enabled devices (especially on ARM/embedded), update to a kernel containing the fix above.
Firmware Best Practice:
Firmware should remove "iommu-addresses" (and "memory-region") if a display isn’t present, to avoid zero-length reservations.
Monitor Kernel Logs:
After the fix, check dmesg or system logs for the new warning about -length IOVA reservations—that’s a sign your firmware needs an update too.
Conclusion
CVE-2023-52455 is a great example of how subtle bugs in low-level kernel code can ripple out to cause big headaches in real deployments. A “just skip if size==” bug might seem tiny, but at kernel level, details matter a lot. Always keep your kernel up-to-date and stay alert to firmware/hardware interactions exposed by open source bug trackers and mailing lists.
Stay patched, stay safe!
*Exclusively written for this platform to help users and sysadmins understand a subtle but impactful Linux vulnerability. For further questions or technical assistance, see the Linux kernel bug tracker or reach out to your hardware vendor.*
Timeline
Published on: 02/23/2024 15:15:08 UTC
Last modified on: 04/30/2024 19:34:34 UTC