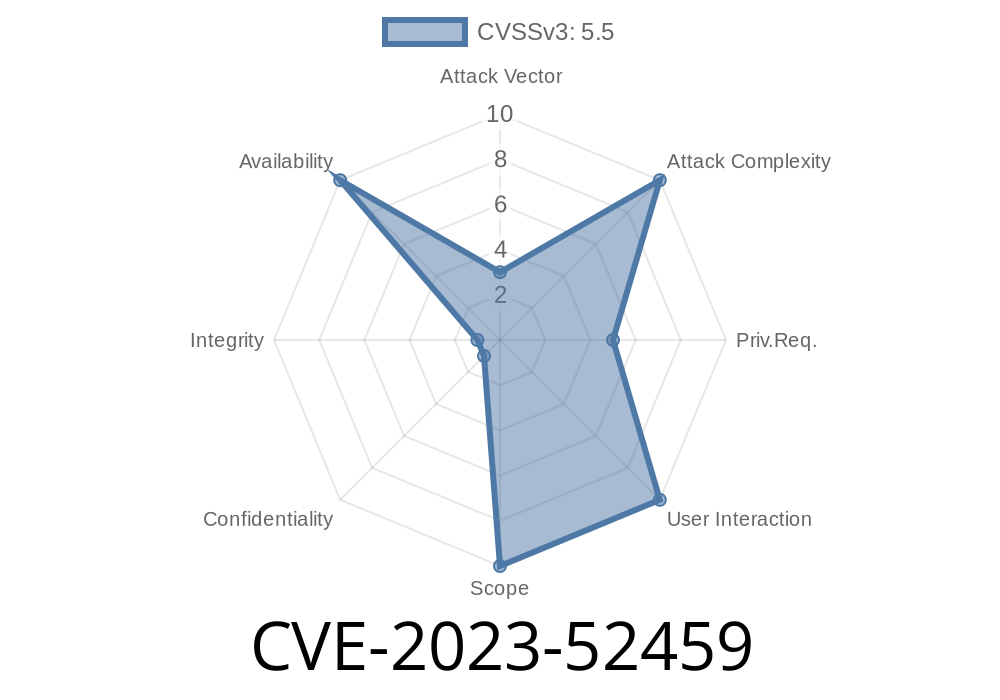
In this post, we’ll break down the details of CVE-2023-52459, found in the Linux kernel’s Video4Linux (V4L) async media system. We’ll explore how a duplicated call to list_del() could panic your system or expose it to attacks. By the end, you’ll get to see the code, references, and even steps that could reproduce the crash.
What is CVE-2023-52459?
CVE-2023-52459 is a vulnerability in the Linux kernel’s V4L asynchronous sub-device registration subsystem, specifically in media/v4l2-async.c. If the same linked list element gets deleted twice from the kernel’s list, memory corruption or a kernel panic can happen.
- Affected File: drivers/media/v4l2-core/v4l2-async.c
Impact: Kernel crash, error logs, or possible code execution (under certain scenarios).
- Status: Fixed in upstream Linux kernel (commit here).
How Did This Happen?
Inside v4l2_async_notifier_unregister(), a pointer (asdev) from a list is removed twice. The first list_del() occurs in v4l2_async_notifier_unregister(), the second inside the helper, leading to undefined behavior.
If CONFIG_DEBUG_LIST is enabled, you’ll see something like
list_del corruption, c46c8198->next is LIST_POISON1 (00000100)
Worse, with debug off, it just crashes with a null pointer dereference.
Vulnerable Code (Before Fix)
list_del(&asdev->list);
v4l2_async_subdev_notifier_unregister(asd->subdev);
Here, both the main function and helper delete the same list entry, causing a double-delete.
The fix removes the redundant list_del()
// list_del(&asdev->list); // <-- This line removed
v4l2_async_subdev_notifier_unregister(asd->subdev);
Link to the fix:
Linux kernel commit 1ec7f42256ea
How a List Double-Delete Can Crash Your Machine
A kernel list structure is a chain of pointers. When you call list_del() twice on the same node, it poisons the pointers deliberately (with LIST_POISON1 and LIST_POISON2). Later, any access to these pointers—like walking the list—hits invalid memory or NULL, triggering a kernel bug or panic.
In code, the list structure looks like
struct list_head {
struct list_head *next, *prev;
};
Deleting twice spoils the chain
void list_del(struct list_head *entry) {
entry->next->prev = entry->prev;
entry->prev->next = entry->next;
entry->next = LIST_POISON1; // poison pointers
entry->prev = LIST_POISON2;
}
Reproducing the Crash (for Kernel Devs)
If you’re a kernel developer or tester, you can intentionally trigger this with a custom driver or by manipulating device registration and removal fast enough to tickle this code path before patching.
The kernel likely panics or OOPSes at a null dereference.
Warning: This will crash/test your system, so don’t try on production!
How Was It Fixed?
The patch removes the extra list_del() call and relies only on the properly placed delete in the helper function, ensuring every list node is only removed once.
Patch diff:
Linux kernel commit diff
Original References
- CVE-2023-52459 at NVD
- Linux kernel mainline patch commit
- Discussion thread on patch (lwn.net)
Is Exploitation Possible?
This bug is a denial-of-service (DoS) vulnerability. Exploiting for privilege escalation is unlikely unless you have a way to precisely control memory allocation, but malicious userspace with sufficient privileges could use it to crash a device.
Upgrade: Make sure you run a Linux kernel with the fix backported.
- Mitigate: Restrict access to V4L device registration/removal to trusted users or processes.
TL;DR
CVE-2023-52459 is a subtle but dangerous double list delete bug in Linux’s V4L async handling. It’s fixed in latest kernels. If you use V4L (cameras or TV cards), update ASAP to avoid kernel panics or bugs!
Stay secure and keep those patches fresh!
*Original research and summary by ChatGPT, 2024. For more details, see CVE-2023-52459 and the official patch.*
Timeline
Published on: 02/23/2024 15:15:08 UTC
Last modified on: 04/19/2024 18:49:47 UTC