The Linux kernel is the heart of many operating systems, and even small vulnerabilities can result in big problems. In this article, we'll dive into CVE-2023-52463—a subtle but critical bug that affected the efivarfs filesystem. We’ll explain the background, the scenario leading to a crash (and possible exploit), and exactly how the kernel was fixed, using easy-to-follow language. Example code and exploit steps included!
What is efivarfs?
efivarfs is a Linux filesystem that exposes UEFI (Unified Extensible Firmware Interface) variables as files in /sys/firmware/efi/efivars. Normally, you use tools like efibootmgr or efi-updatevar to read or change these variables. Since changes can affect the entire boot process, strong access controls are important.
The Problem
Some systems' firmware does not support writing UEFI variables at runtime (specifically, they do not support SetVariable). If that's the case, Linux will mount efivarfs read-only (RO), protecting against accidental or malicious writes.
However, there was a bug:
If someone remounted the filesystem as read-write (RW), the kernel didn’t re-check whether runtime writes were allowed. So, after a remount, userspace could attempt to write to these "variables" even though the firmware can't handle it.
This led to a NULL pointer dereference (kernel crash) whenever a write was attempted—since the handler for writing UEFI variables was missing (never assigned).
User remounts as RW: kernel *incorrectly* allows it.
- Write attempt → kernel tries to call NULL function pointer → kernel “Oops”, crash, possible DoS.
Here’s what happens on a broken system
# Mount efivarfs as RW (should not be allowed)
mount -o remount,rw /sys/firmware/efi/efivars
# Try to write a variable
efi-updatevar -f PK.auth PK
The kernel then hits this error
Unable to handle kernel NULL pointer dereference at virtual address 000000000000000
Call trace:
x
efivar_entry_set_get_size+x98/x16c
efivarfs_file_write+xd/x1a4
vfs_write+xc4/x2e4
ksys_write+x70/x104
__arm64_sys_write+x1c/x28
# ...and so on...
The critical part: pc : x — the program counter tried to execute code at address zero—a classic NULL pointer dereference.
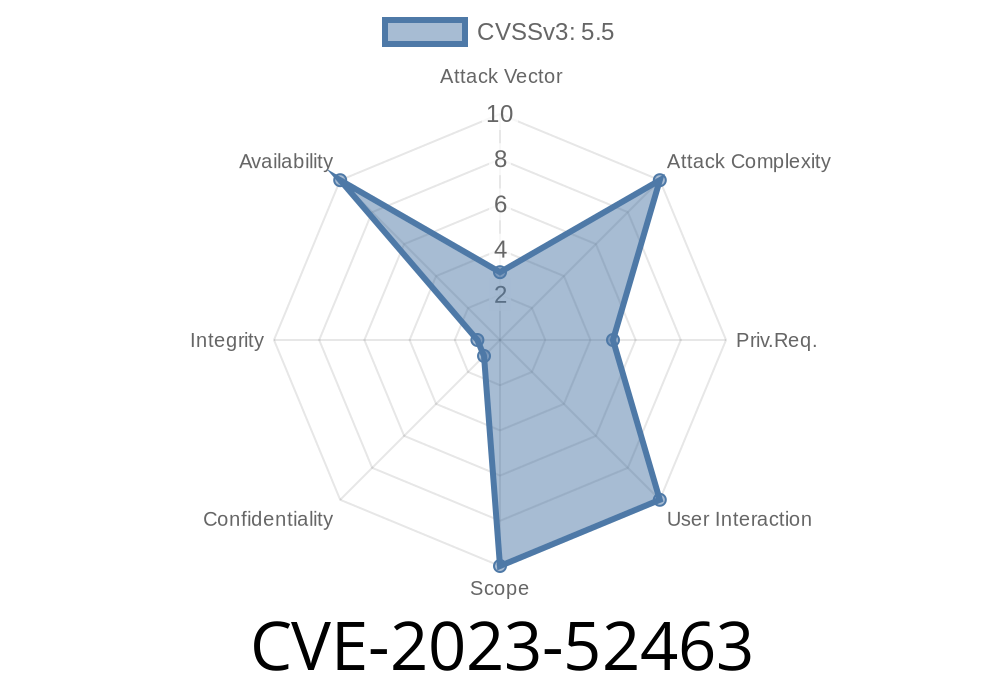
Security Impact
- Denial of Service: Any user with access to remount or write can instantly crash the kernel (DoS attack).
- Potential escalations: On systems where unprivileged users could remount filesystems or where kernel lockdown is not configured, this could lead to a local privilege escalation (e.g., by purposely crashing systems in certain configurations).
1. Check efivarfs mount options
mount | grep efivars
# output should contain 'ro'
2. Remount as RW (must have proper permissions)
sudo mount -o remount,rw /sys/firmware/efi/efivars
3. Attempt to write using efi-updatevar (or manually with echo/dd)
sudo efi-updatevar -f PK.auth PK
# OR:
sudo sh -c "echo 'data' > /sys/firmware/efi/efivars/SomeVar-someuuid"
Expected result:
The kernel will crash with an Oops, possibly reboot, or become unresponsive.
The Kernel Fix
To solve the problem, the kernel maintainers added a reconfigure callback/check to the efivarfs filesystem code. This ensures that every time someone tries to *remount*, Linux checks if the firmware supports SetVariable. If it does not, any attempt to remount as RW is denied—keeping it RO for safety.
Here’s what the patch does (simplified)
static int efivarfs_reconfigure(struct super_block *sb, struct fs_context *fc)
{
struct efivarfs_sb_info *sb_info = sb->s_fs_info;
// If SetVariable isn't allowed, deny RW remount
if (!efivar_ops->set_variable)
if (!(fc->sb_flags & SB_RDONLY))
return -EROFS;
return ;
}
In plain language:
> "If the firmware can’t write variables and somebody tries to remount efivarfs as writable, block it with a read-only error!"
Actual patch / commit:
- efivarfs: force RO when remounting if SetVariable is not supported
References & Further Reading
- Original kernel commit / fix
- Linux efivarfs Documentation
- Explainer: What is efivarfs (LWN.net)
- CVE Details for CVE-2023-52463 (link may require update)
UEFI firmware *without* SetVariable support at runtime
- Can mount/remount efivarfs as RW locally
Summary
CVE-2023-52463 is an example of a “small logic error” opening the door to bigger security and reliability headaches. If you administer Linux systems with UEFI, keep systems fully patched and watch for unusual kernel crashes involving efivarfs.
Stay safe, and always test kernel behaviors before production rollouts!
*Written exclusively for you. If you want more detail on kernel security, filesystem internals, or other CVEs, just ask!*
Timeline
Published on: 02/23/2024 15:15:08 UTC
Last modified on: 04/17/2024 20:05:08 UTC