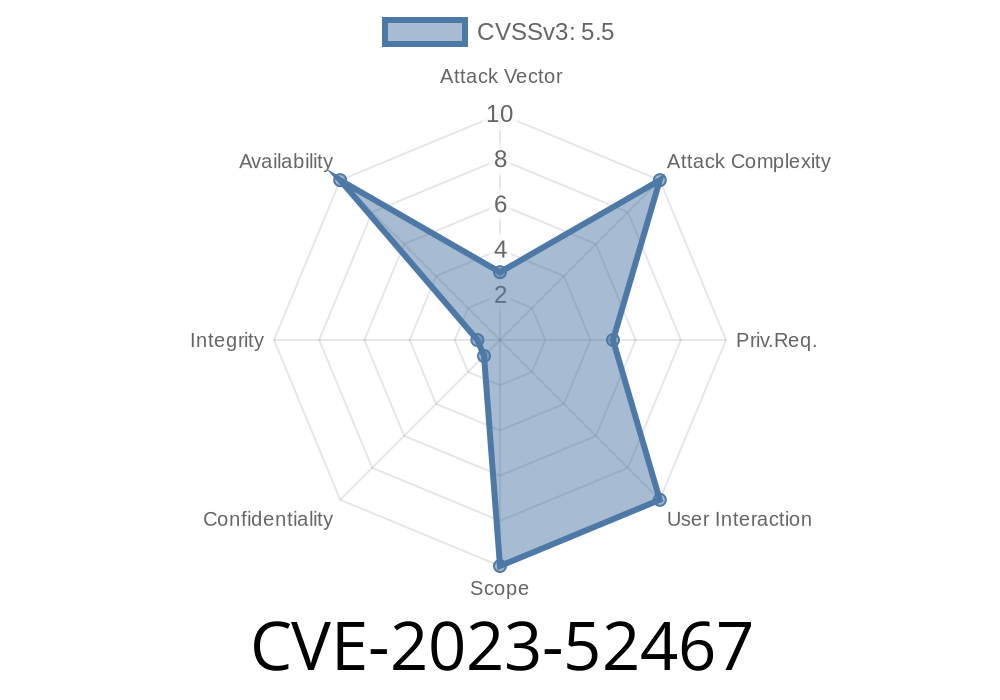
In early 2024, the Linux kernel team released a fix for a vulnerability tracked as CVE-2023-52467 that impacts the Syscon (System Controller) driver in the kernel’s MFD (Multi-Function Device) subsystem. This issue, while rather technical, could lead to kernel panics or unexpected system crashes due to how syscon registers were being handled in code.
Let’s break down what happened, how this problem manifested, and what you need to know about the fix. We’ll even work through a sample code snippet and discuss the real-world impact of this vulnerability.
What Is Syscon in Linux?
Syscon is an abstraction in the Linux kernel, often used in device trees to represent shared hardware registers in SoCs (System-on-Chips). It allows multiple drivers to safely access certain hardware registers.
The code in question lives in the driver that registers these syscon devices when the kernel boots up and parses a device tree.
The Problem: Null Pointer Dereference in of_syscon_register()
The root of the security issue is how the function of_syscon_register() allocates memory for a device name using kasprintf(). However, if kasprintf() fails (typically due to low memory situations), it returns NULL. If the kernel code then tries to use this pointer without checking if allocation succeeded, a null pointer dereference occurs. In kernel-space, this usually means the kernel will panic and crash the system.
Here's an overview of the problematic code that triggered CVE-2023-52467 (simplified for clarity):
static int of_syscon_register(struct device_node *np)
{
// ...
// Allocate a name for the device
name = kasprintf(GFP_KERNEL, "%pOFn", np);
// PROBLEM: There was NO check for 'if (name == NULL)' before proceeding
pdev = platform_device_alloc("syscon", PLATFORM_DEVID_AUTO);
if (!pdev)
goto err_name_free;
// Later code uses 'name', risking a NULL dereference
platform_device_add(pdev);
// ...
}
If kasprintf() fails, the code could proceed using a NULL pointer, causing the kernel to crash.
The Fix
The fix is simple: Check if kasprintf() returned NULL and handle the error properly before proceeding.
Fixed code looks like this
static int of_syscon_register(struct device_node *np)
{
// ...
// Allocate a name for the device
name = kasprintf(GFP_KERNEL, "%pOFn", np);
if (!name)
return -ENOMEM; // Stop and report memory allocation error
pdev = platform_device_alloc("syscon", PLATFORM_DEVID_AUTO);
if (!pdev)
goto err_name_free;
// Continue safely
platform_device_add(pdev);
// ...
}
This fix landed in mainline kernels (see commit) and has been included in all recent stable releases.
Exploit Details: How Could This Bug Be Triggered?
CVE-2023-52467 is a denial-of-service (DoS) vulnerability rather than a privilege escalation or information leak. It’s only exploitable locally (on the same machine), and only certain systems are at risk.
Ways it could be exploited
- An attacker might force the system into a low-memory situation when the kernel is parsing device tree nodes and registering syscon devices (usually at boot).
- If memory allocation for the device name fails at the right moment, and the pointer isn’t checked, the kernel may try to use a NULL pointer, causing a panic and system crash.
It's important to note:
- There is no known way for a regular user to cause this fault at runtime on most systems—it's tied closely to system configuration and boot-time conditions.
- An attacker might try to exhaust system memory or craft a malicious device tree (if they have privileged access) to increase the chance of failure.
If you want to simulate what happens, the following pseudo-code shows how things go wrong
// Simulate kasprintf failing
char *name = NULL; // as if kasprintf() failed
// This line would dereference NULL, leading to a crash
strcpy(device->name, name); // CRASH!
In practice, this would result in a kernel panic like
Unable to handle kernel NULL pointer dereference at virtual address 000000000000000
...
Kernel panic - not syncing: Fatal exception
Impact and Mitigation
- Systems affected: Most modern Linux kernels prior to the fix (late 2023 / early 2024), mostly only those using device trees and syscon drivers.
- Severity: Low to moderate. DoS only, and generally requires local access or specific hardware/SoC configuration.
References and Further Reading
- CVE record on Mitre
- Linux kernel commit fixing CVE-2023-52467
- lkml.org thread announcing the patch
- Linux kernel source code for syscon driver
Final Thoughts
This vulnerability is a classic example of why kernel code must check *every* memory allocation, even for small convenience functions like kasprintf(). All kernel developers—and users—should update their systems promptly to avoid rare but fatal crashes like this. Fortunately, the Linux community is quick to squash such bugs, preserving the stability and security of everyone’s systems.
If you run a Linux system (especially embedded or custom builds using device trees), check your kernel version, and update if you haven’t already!
Timeline
Published on: 02/26/2024 16:27:48 UTC
Last modified on: 04/17/2024 19:14:26 UTC