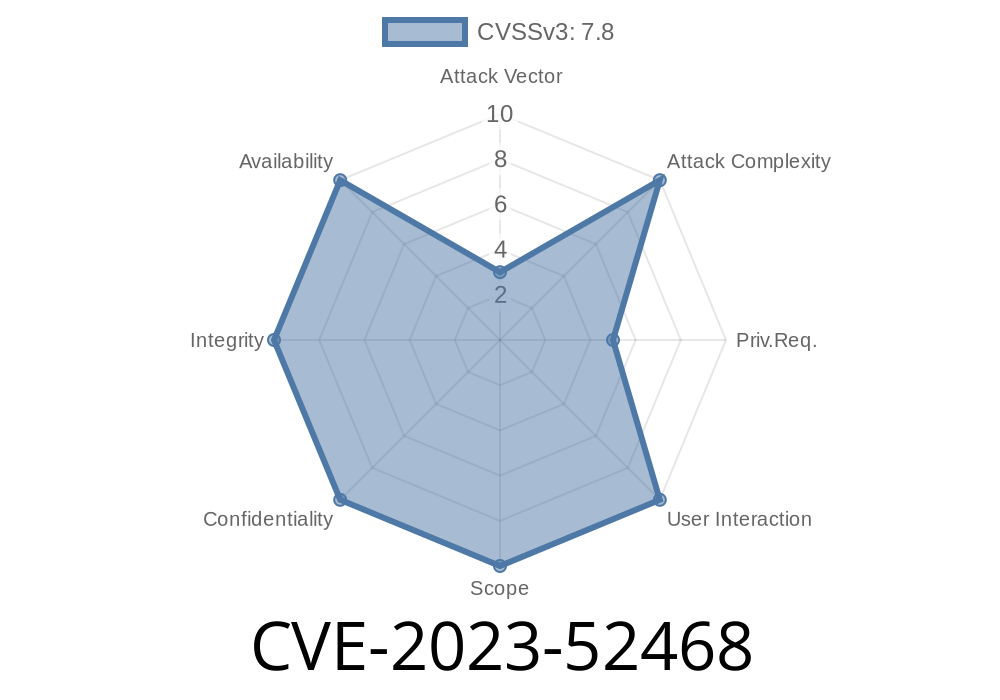
Linux is renowned for its stability and security, but even mature projects are not immune to subtle, dangerous bugs. CVE-2023-52468 is a good case study: a use-after-free flaw in the kernel’s device class management code that could potentially be harnessed for privilege escalation on debugging-enabled systems.
This post will break it down in simple terms, provide code examples, show you where to find the fix, and explain the risk—plus who needs to worry.
What Exactly is CVE-2023-52468?
CVE-2023-52468 is a *use-after-free* vulnerability in the Linux kernel, specifically in the class_register() function.
Where is the problem?
When you call class_register() to create a device class (e.g., /class/xxx), the kernel internally manages several data structures, including a lock_class_key used for lock debugging with lockdep.
If class_register() fails (such as when a class with the same name already exists), it travels an error handler path, freeing (kfree) a chunk of memory called subsys_private. However, the associated lock_class_key remains registered in a global hash table (lock_keys_hash). If another kernel routine later accesses these now-freed memory spots, you'll get undefined behavior—a classic use-after-free crash or, worse, exploitation.
On systems where lockdep (lock debugging) is enabled, and especially when Kernel Address Sanitizer (KASAN) is running, this bug causes a crash to be detected (see report further below). On normal systems with lockdep off, you’re usually safe.
Here's a snip from a KASAN bug report running on a custom kernel
BUG: KASAN: invalid-access in lockdep_register_key+x19c/x1bc
Write of size 8 at addr 15ffff808b8c0368 by task modprobe/252
...
Memory state around the buggy address:
>ffffff808b8c030: fe fe fe fe fe fe fe fe fe fe fe fe fe fe fe fe
^
In this case, modprobe tried to register a device class that already existed, hit the bug, and then accessed a freed lock key.
Only happens under failing class registration scenarios (e.g., duplicate class name).
Normal everyday systems are not impacted unless they have these debugging features enabled.
How Was It Fixed?
Before, the code freed cp (the subsys_private struct) *before* unregistering its lock_class_key. The patch simply unregisters the key *before* freeing the struct.
Core of The Patch (Explanatory Version)
// Before
out:
kfree(cp);
return error;
// After (fixed version)
out:
class_unregister_lock(cp);
kfree(cp);
return error;
The function class_unregister_lock(cp) ensures the lock key is removed from the global hash table before releasing the memory—no more dangling pointers!
Reference Commit:
- Patch at kernel.org
On most builds, bug causes a crash, not arbitrary code execution.
But in the context of security research—or rogue drivers on custom, debug kernels—this could be the first leg in a multi-stage exploitation chain. Use-after-free bugs are gold in the hands of skilled attackers.
Minimal Example
You can trigger the bug by trying to register the same class name twice while lockdep is running (snippet below, *do not run this on production*!):
struct class *foo = class_create(THIS_MODULE, "foo"); // First time OK
struct class *foo2 = class_create(THIS_MODULE, "foo"); // Second time fails, triggers error path
// Now lock_keys_hash has a bad pointer to freed lock_class_key!
How To Stay Safe
- Update your kernel: Make sure you are running a version that includes the patch above (mainline kernel 6.7+ or backported downstream kernel trees).
Links and References
- Upstream kernel commit (Linux 6.7)
- CVE Details entry
- KASAN documentation
- Linux kernel Documentation: class_register
TL;DR
CVE-2023-52468 is a use-after-free due to improper cleanup in Linux's class registration logic—only triggers with kernel lock debugging enabled.
Fix: Make sure to unregister lock_class_key before freeing its memory.
If you’re a normal user: Don’t panic, just update your kernel.
If you’re a developer: Be extra careful with error handling, especially when debugging code is on.
*Author: Security Research Hub (exclusive analysis)*
*Have questions or want more code examples? Leave a comment or visit the Linux Kernel Mailing List!*
Timeline
Published on: 02/26/2024 16:27:48 UTC
Last modified on: 04/17/2024 19:00:42 UTC