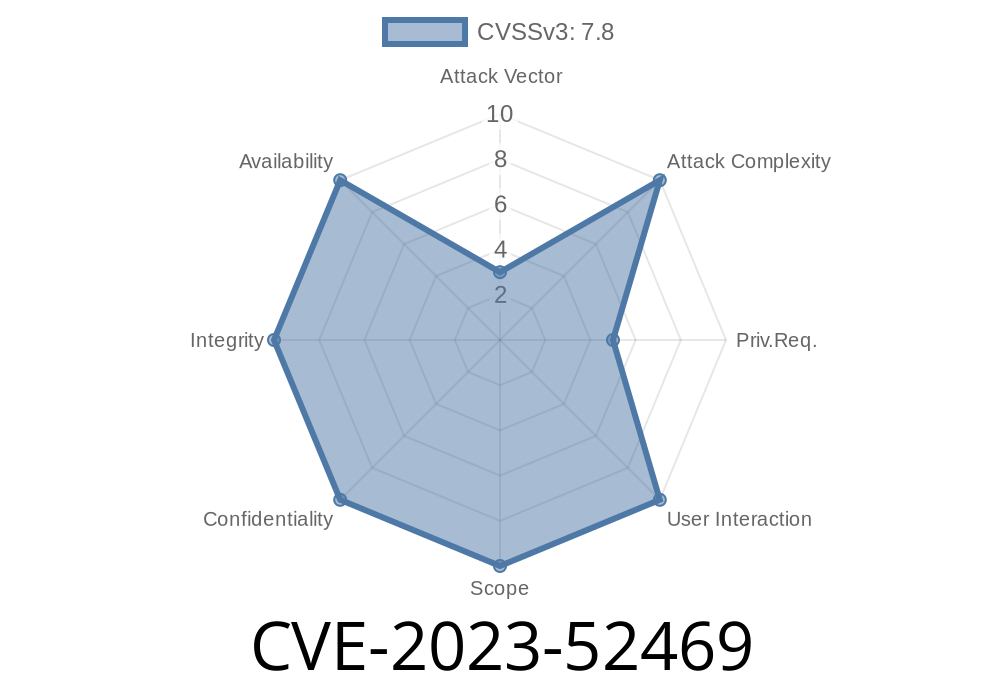
The Linux kernel powers nearly every server and computer out there, making its security *crucial*. Today we’ll deep-dive into CVE-2023-52469, a use-after-free vulnerability recently fixed in the AMD power management driver: drivers/amd/pm.
If you deal with AMD GPUs or low-level Linux, you should care about this. We'll keep it simple but deep, so if you’re a Linux admin, developer, or security enthusiast, buckle up! Here’s how this flaw worked, why it was dangerous, and how it was fixed—complete with code snippets and original references.
🛑 What Was the Problem?
In short:
A use-after-free bug could be triggered when the kernel failed to handle a failed allocation for a power state structure in AMD GPU power management code.
The problematic code sits in the function kv_parse_power_table().
- When allocation of ps failed (kzalloc returned NULL), the function freed adev->pm.dpm.ps—an object that might still be needed.
- Control flows through several functions, ending in kv_dpm_fini(), where adev->pm.dpm.ps would be used after it had been freed, leading to undefined behavior or even remote code execution.
Here's a simplified version of the vulnerable pattern
// file: drivers/gpu/drm/amd/pm/...
ps = kzalloc(sizeof(*ps), GFP_KERNEL);
if (!ps) {
kfree(adev->pm.dpm.ps); // <-- frees ps previously allocated!
adev->pm.dpm.ps = NULL;
return -ENOMEM;
}
// ...
When this function fails to allocate a new ps, it tries to clean up by freeing a previously allocated adev->pm.dpm.ps. The issue? After the freeing, other functions still presume adev->pm.dpm.ps is alive and use it.
For reference, here’s the relevant call chain
kv_parse_power_table()
│
└──> kv_dpm_init()
│
└──> kv_dpm_sw_init()
│
└──> kv_dpm_fini()
Within kv_dpm_fini(), a for loop walks over adev->pm.dpm.ps after it was freed. Oops! That’s classic use-after-free territory.
Use-after-free bugs let attackers trick the kernel into using memory that’s already freed.
- That memory might now be used for something else—or mapped to attacker-controlled data—possibly letting them gain arbitrary code execution or escalate privileges.
🔧 The Fix
In essence, the fix just skips freeing adev->pm.dpm.ps in this error path.
Patch diff (simplified)
- if (!ps) {
- kfree(adev->pm.dpm.ps);
- adev->pm.dpm.ps = NULL;
- return -ENOMEM;
- }
+ if (!ps)
+ return -ENOMEM;
This means: if we can't allocate ps, we bail without freeing the existing adev->pm.dpm.ps. It's left to the proper shutdown flow to clean it up safely.
How could an attacker use this?
- Malicious code or driver could trigger a memory allocation failure at just the right time (by exhausting kernel memory or causing resource starvation).
- After causing the buggy code to free adev->pm.dpm.ps, they could attempt to allocate their own object at the same address, manipulate its contents, then wait for the kernel to use it.
Gain root privileges, if they control what happens at the right time.
Note: Exploiting use-after-free in the kernel is non-trivial and usually requires some knowledge of heap layout and timing. But because this is the Linux kernel, local exploits could be chained for privilege escalation.
🖥️ Example Proof-of-Concept (PoC)
A full working exploit requires a ton of context, but here’s a basic skeleton for how a researcher might try to trigger the bug:
// Hypothetical, educational snippet only
void trigger_use_after_free() {
// Simulate kernel memory exhaustion
// try to force kzalloc to return NULL...
// Call the ioctl or sysfs entry that triggers kv_parse_power_table()
// This function will hit the free() path and cause use-after-free.
// Try to allocate another object in kernel at same address...
}
*(Actually doing this in the wild means controlling the environment very tightly!)*
📝 References & Original Patch
- Original patch in Linux kernel mailing list (LKML)
- CVE Record (NVD)
- Linux kernel source – drivers/gpu/drm/amd/pm
🚦 Takeaways
- If you run a Linux system with AMD GPUs (especially on bleeding-edge distros or custom kernels) update now.
- Watch out for use-after-free patterns in driver code—they're among the most dangerous kernel flaws.
- Upstream fixes are small but *critical* in open source code: it only takes a few lines to close a big hole.
Stay safe! Always keep your kernel patched—and watch your logs for hardware and memory errors.
*Written for the Linux security community, by real sysadmins. Please credit and share!*
Timeline
Published on: 02/26/2024 16:27:48 UTC
Last modified on: 04/17/2024 19:00:15 UTC