In January 2024, a security issue dubbed CVE-2023-52471 was patched in the Linux kernel. This flaw affected specific network adapters managed by the Intel Ethernet Controller (ICE) driver. In simple terms, a bug in this driver could cause the kernel to crash if it encountered a rare "out of memory" error. While this is not the most dangerous vulnerability (it doesn't directly allow privilege escalation or code execution), unexpected kernel crashes are never good news in server and critical networking setups.
This article gives you an easy-to-understand look at CVE-2023-52471—how it happens, the code it impacts, the patch, and what you should do if you manage Linux systems.
What Is the ICE Driver?
The ICE driver is part of the Linux kernel, responsible for managing Intel E800 Series Ethernet controllers. These are high-performance network cards found in servers and data centers, often where uptime and reliability matter most.
The PTP Feature
PTP stands for Precision Time Protocol. It's a network clock synchronization standard that helps computers agree on the exact time, which is crucial for certain applications—including financial systems, telecommunications, and industrial networks.
The file ice_ptp.c implements PTP support for the ICE driver. It's where the bug was found.
What is devm_kasprintf()?
This function helps format strings in the Linux kernel (like sprintf, but allocates memory for you). If memory runs out (a rare but possible case), it returns NULL.
The Bug
The original code did not check if devm_kasprintf() returned NULL before using its result. If the system ran out of memory just when this function was called, the system would try to use a NULL pointer. This leads to a NULL pointer dereference, which almost always causes a kernel panic (crash).
Let's look at a simplified problematic code fragment
// OLD VULNERABLE CODE
struct device *dev = ...;
const char *clk_name = devm_kasprintf(&pdev->dev, GFP_KERNEL, "ptp_%s", dev_name(dev));
...
clk_hw_init(&my_clk.hw, clk_name, &my_clk_ops, ...);
// If clk_name is NULL, this will panic.
Here, devm_kasprintf() could return NULL, but the code doesn't check for that.
The Fix
The maintainers fixed the bug by adding a NULL check after calling devm_kasprintf(). If the allocation fails, the function bails out gracefully.
// NEW SAFE CODE
struct device *dev = ...;
const char *clk_name = devm_kasprintf(&pdev->dev, GFP_KERNEL, "ptp_%s", dev_name(dev));
if (!clk_name)
return -ENOMEM; // Or handle error properly
...
clk_hw_init(&my_clk.hw, clk_name, &my_clk_ops, ...);
Now, if memory allocation fails, the kernel does not try to use a NULL pointer and avoids a crash.
Reference for the fix:
- kernel.org patch link
Severity
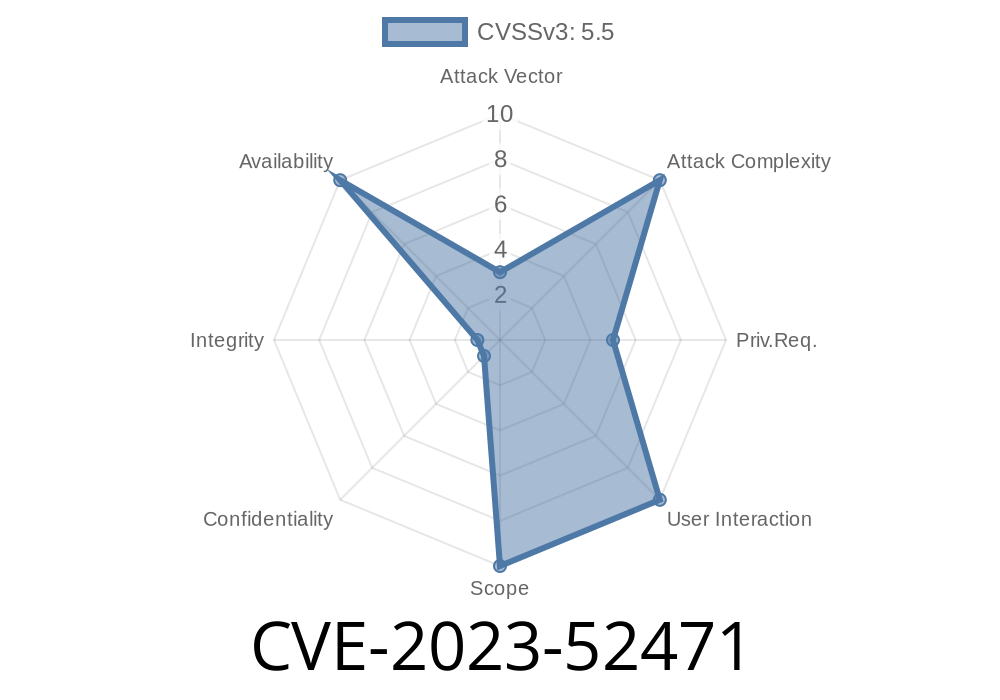
This bug is a denial-of-service (DoS) issue. An attacker (or a rare insane coincidence during heavy memory pressure) could crash the kernel by exploiting this NULL pointer dereference.
Notably: The attacker would need access to trigger the code path in the ICE PTP logic, which isn't accessible to regular unprivileged users. It's much more likely to be an accidental crash rather than a targeted exploit.
What an Exploit Could Look Like
Let's be clear: you can't just send packets and crash the system—memory allocation must fail at the right moment. That is, the attack would require exhausting system memory and then triggering the PTP feature to allocate a new clock name (maybe by loading/unloading drivers or reconfiguring network hardware).
This is barely practical, except maybe in a targeted denial-of-service against a critical or production server where the attacker already has some level of privilege.
Environments where stability is critical (data centers, financial institutions, telecoms)
- Setups with untrusted users who can mess with hardware/network config
Practical Steps to Stay Safe
- Update your kernel: Make sure you're running Linux kernel 6.7 or newer, or the latest 6.6 LTS with security patches applied.
- If you must stick with an older kernel, investigate backported security fixes from your Linux vendor (especially if using RHEL, Ubuntu, or Debian).
References and Further Reading
- CVE-2023-52471 at NVD
- Official patch at kernel.org
- Linux kernel’s ICE driver source
- Linux kernel documentation - Memory allocation
Conclusion
CVE-2023-52471 is an example of how small oversights in memory management can lead to system crashes, even in trusted code like the Linux kernel. While exploitation is tricky and unlikely for regular users, stability is important—especially in the data center world.
Timeline
Published on: 02/26/2024 16:27:48 UTC
Last modified on: 04/17/2024 18:59:17 UTC