CVE-2023-52473 is a vulnerability discovered in the Linux kernel’s thermal framework, where a NULL pointer dereference could occur during thermal zone registration error handling. This can lead to a kernel crash or system instability in certain error paths. Below, we break down the vulnerability, show the affected code, discuss how it was fixed, and explain the exploit potential—all in simple, clear English.
What is the Linux Kernel Thermal Core?
The thermal core in the Linux kernel monitors and manages device temperature, helping prevent devices from overheating by throttling or shutting down components. It uses "thermal zones" to manage various thermal sensors and their associated trips (thresholds triggering cooling actions).
What was the Problem?
When the kernel tries to register a new thermal zone device, it calls thermal_zone_device_register_with_trips(). If an error happens while registering (for example, due to hardware issues), the code did something dangerous:
Here's a simplified version of the problematic sequence
tz = thermal_zone_device_alloc(...);
ret = device_register(&tz->device);
if (ret) {
// After failed register, tz is set to NULL
put_device(&tz->device);
tz = NULL;
}
kfree(tz->tzp); // <-- PROBLEM: tz is NULL here!
If this codepath runs, the kernel tries to free memory at tz->tzp when tz is already NULL, causing a crash.
This bug traces back to two changes
- Commit adc8749b150c introduced the tz = NULL assignment to avoid double-free after unregistering.
- Commit 464962d9404 changed the unregistration function so the tz memory is no longer freed in this place, making the tz = NULL assignment redundant.
So, the original safety mechanism backfired as the code evolved.
Fix: Remove the NULL Assignment
The fix was simple: remove the redundant tz = NULL assignment after device_register() fails. This ensures that if clean-up is required, the cleanup code references the still-allocated object rather than NULL.
Here is the fixed code snippet
tz = thermal_zone_device_alloc(...);
ret = device_register(&tz->device);
if (ret) {
put_device(&tz->device);
// tz is NOT set to NULL anymore
}
kfree(tz->tzp); // Safe, as tz is not NULL
Patch reference:
https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/commit/?id=53e9e23719319217d2537b48ea659083e6309262
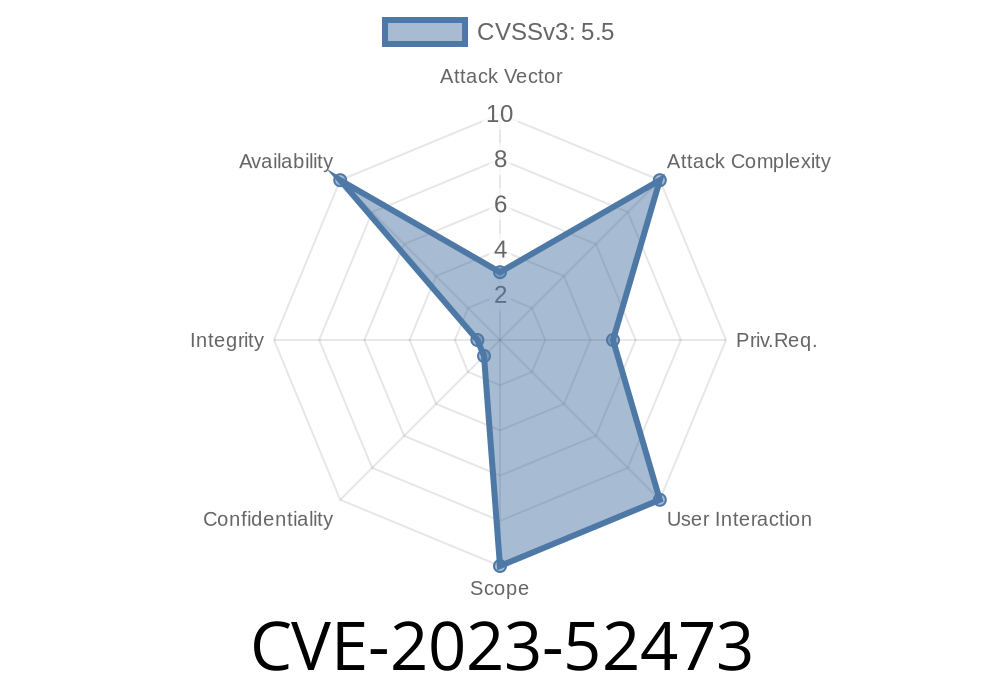
Practical Exploitability
The bug is triggered in error paths when registering a new thermal zone device fails. Exploiting it would generally require:
Malicious or buggy device interfacing with the thermal subsystem.
- Or, the attacker being able to influence device_register() to fail in a way that leads to this code path.
Because it requires such specific conditions and generally only leads to a kernel crash, the real-world exploitability is limited—but still a local denial of service risk (system crash) for privileged (root) users.
Protecting Your System
- Upgrade: Apply the latest kernel updates from your distribution, especially if you build custom kernels.
Monitor: Watch logs for kernel crashes related to thermal zones or devices.
- Limit modules: Do not load untrusted kernel modules or allow insecure device drivers, especially on shared systems.
Additional References
- Kernel Patch Fixing CVE-2023-52473
- CVE Details for CVE-2023-52473
- Linux Kernel Thermal Documentation
Summary
CVE-2023-52473 was a subtle NULL pointer dereference in the Linux kernel’s thermal core, fixed by removing an outdated line of code. This prevents accidental kernel crashes during thermal device error handling. The issue mostly affected kernel developers, device manufacturers, and those maintaining custom kernels. While not easily weaponized, keeping your system up to date remains the best protection.
Need help checking your kernel version or applying updates? Leave a comment!
Timeline
Published on: 02/26/2024 16:27:48 UTC
Last modified on: 04/17/2024 18:30:15 UTC