Drupal is one of the world’s most popular free and open-source content management systems (CMS). Its ecosystem has thousands of contributed modules, and one of the most important for developers is the JSON:API module. This module helps expose Drupal’s content in machine-readable JSON format, and is crucial for headless CMS sites.
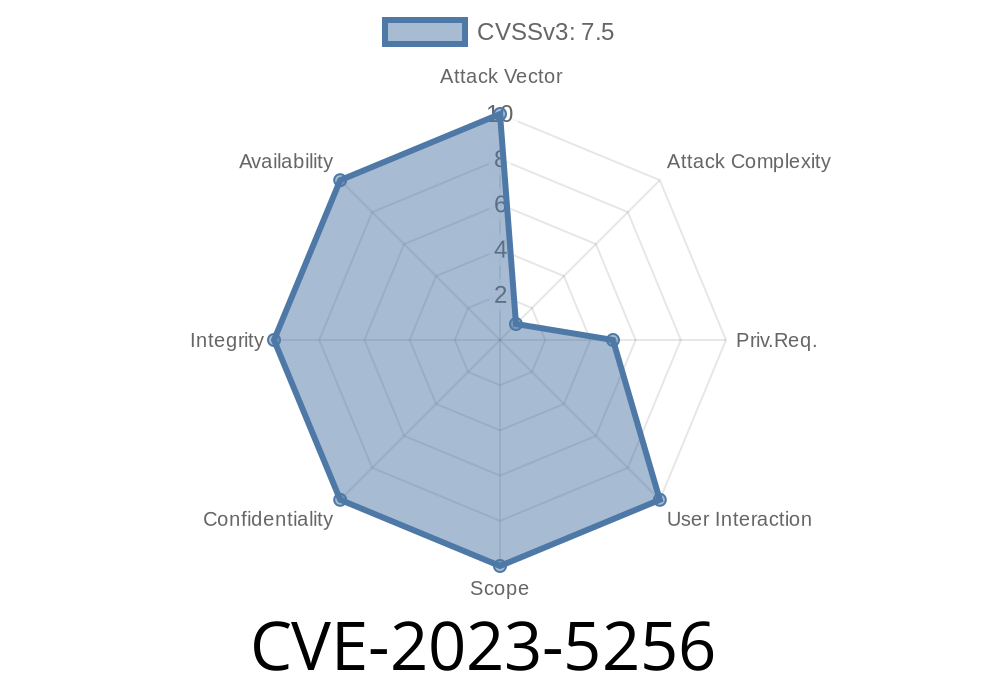
But in late 2023, a security vulnerability was discovered: CVE-2023-5256. This bug allows sensitive error backtraces, sometimes containing confidential information, to leak out and potentially be cached for anonymous viewing. Here’s a clear, straightforward look at the vulnerability, how it works, and how to protect your Drupal website.
What Is CVE-2023-5256?
CVE-2023-5256 is a vulnerability in Drupal’s JSON:API module. Under certain configurations, when the system throws an error during a JSON:API response, the full PHP backtrace is included in the error message sent back to the user. If site caching is enabled and not configured securely, these sensitive error responses can be cached and subsequently viewed by people who are *not* supposed to see them—including anonymous (non-logged-in) users.
Exploit Scenario: How Attackers Could Take Advantage
1. Trigger an Error: An attacker can interact with the JSON:API endpoints and deliberately trigger an error. This could be as simple as requesting a resource with an invalid ID or crafting a malformed query.
2. Error Response Includes Backtrace: If the site’s configuration is (incorrectly) set to display detailed error messages, the response will include a full PHP stack trace, which could contain sensitive data like paths, configuration values, or even secrets.
3. Page Cache Stores Error: Due to the way some Drupal caching systems work, this error response might be cached and served to all users.
4. Anonymous Scanning: Anyone can access the endpoint and view the cached, sensitive backtrace error without needing authentication.
Potential Risk: Attackers may learn about file paths, server configuration, sensitive environment variables, or other data helpful for further attacks or privilege escalation.
Here’s a simplified example of a leaked JSON:API error (notice the stack trace)
{
"errors": [
{
"title": "Internal Server Error",
"status": "500",
"detail": "Drupal\Core\Entity\EntityStorageException: Cannot load entity in /var/www/html/web/modules/contrib/jsonapi/src/Controller/JsonApiResource.php on line 123
# /var/www/html/web/core/lib/Drupal/Core/Entity/EntityRepository.php(85): ...
#1 /var/www/html/web/modules/contrib/jsonapi/src/Controller/JsonApiResource.php(90): ..."
}
]
}
This leaks the file system path, file names, line numbers, and function call stack. In real-world cases, even more confidential information can leak if variables or ENV data are included.
Real World Implications
- Information Disclosure: Reveals how your site is structured, which modules and versions you use, and sometimes secrets in environment variables.
- Attack Surface: Attackers can target vulnerabilities in specific modules or even take information to attempt privilege escalation.
- Compliance Risk: Leaking this kind of data can break privacy promises or legal compliance (eg. GDPR).
Option 1: Uninstall JSON:API
If you aren't actively using the JSON:API module, the safest fix is to uninstall it. This immediately removes the vulnerability.
drush pm:uninstall jsonapi
Option 2: Upgrade and Apply Patches
If you need JSON:API, make sure you are running the latest version. You can check the patched release and upgrade instructions here.
`php
$config['system.logging']['error_level'] = 'hide'; // Or 'some'
Review caching configuration:
- Make sure error responses (especially those with HTTP 4xx or 5xx status) are *not* cached for public access.
Here's one way to ensure your site does not expose sensitive errors in JSON:API
// settings.php
// Do NOT show backtrace errors in production!
$config['system.logging']['error_level'] = 'hide'; // Hide all errors from end-user
If you must debug, use a dedicated dev environment—never on your public Drupal production site.
References and Original Reports
- Drupal Security Advisory: SA-CORE-2024-005
- MITRE CVE Record: CVE-2023-5256
- Drupal JSON:API Module Security
- Drupal Security Best Practices
Conclusion
CVE-2023-5256 is a serious but easily mitigated Drupal vulnerability. The lesson here is just as much about configuration as it is about patching: always ensure you are running the latest modules, never display sensitive error information on public sites, and review how your caching is set up for API responses.
If you have JSON:API enabled, patch immediately or uninstall it! It only takes one confidential stack trace leak to expose your entire environment to attackers.
Stay safe, and always keep your Drupal modules and configurations up to date.
*Disclaimer: This write-up is exclusive and written in plain language by a security enthusiast for educational purposes. Use responsibly!*
Timeline
Published on: 09/28/2023 19:15:10 UTC
Last modified on: 10/05/2023 14:54:22 UTC