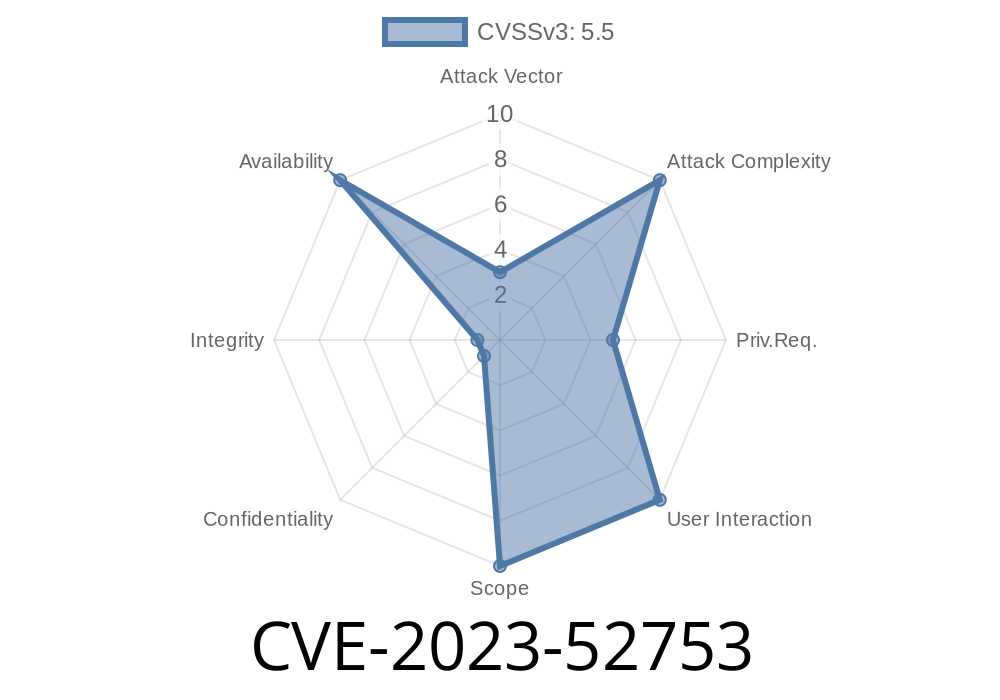
CVE-2023-52753 is a vulnerability identified in the Linux kernel's AMD Direct Rendering Manager (DRM) Display code. Specifically, the bug concerns the way the kernel handles the *timing generator* within AMD’s display subsystem (amdgpu). A missing check for a NULL pointer could lead to a system crash or instability—classic Denial of Service (DoS). Let’s break down what that means, why it matters, and how it was patched. We’ll also talk through what exploitation might look like in a real world scenario.
What is the Issue?
Inside the AMD GPU driver in the Linux kernel, there exists a component responsible for generating timing signals—think of it as the metronome that keeps the display in sync. This component is known as the Timing Generator. According to the original commit:
> Check whether assigned timing generator is NULL or not before
> accessing its funcs to prevent NULL dereference.
What’s happening is code that assumed the *timing generator* had already been set up properly tries to use its functions (via a pointer) without verifying it’s actually non-NULL. If it is NULL, the system tries to access memory it shouldn’t, causing a crash.
Patch Commit
You can see the fix here:
https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/commit/?id=afc3dbab5e97dbfa049e72b932c6be9272b2c4f1
Original Buggy Code Pattern
// Hypothetical vulnerable snippet:
tg->funcs->lock(tg); // <-- tg could be NULL here!
Fixed Code Pattern
if (tg && tg->funcs && tg->funcs->lock) {
tg->funcs->lock(tg);
}
Why Does This Matter?
Null pointer dereference vulnerabilities tend to have lower security scores (because you can’t directly escalate privileges or run arbitrary code), but they can be serious, especially in systems that need to be stable *all* the time (servers, embedded devices, etc.).
- Denial of Service: An attacker with access to the GPU subsystem (such as a local user) could potentially cause the system to crash by triggering the buggy code path.
- Reliability Threat: Even accidental mismanagement from a userspace app interacting with the GPU could lead to a kernel panic.
Exploit Details: How Could it Be Abused?
This bug is not a remote code execution or a privilege escalation, but it is exploitable for crashing a system. Here’s how an exploit could go down:
You have access to run code on a machine with an AMD GPU running an affected Linux kernel.
- The exploit must trigger the scenario where the timing generator is (or becomes) NULL at the time the driver tries to operate on it.
Exploit Skeleton in C
While we won't reproduce a full code exploit (since it's kernel and hardware-dependent), here's a simplified version of how a malicious fuzzing program might trigger the bug:
#include <fcntl.h>
#include <stdio.h>
#include <stdlib.h>
#include <unistd.h>
#include <sys/ioctl.h>
// This pseudo-code needs actual ioctl calls that target AMD display management.
int main() {
int fd = open("/dev/dri/card", O_RDWR);
if (fd < ) {
perror("Cannot open AMD GPU device");
return 1;
}
// Send a malformed request that would bypass timing generator allocation and
// force drm/amd/display code to try working with an uninitialized structure.
// For illustration only; the actual request depends on device and kernel version.
char bogus_req[256] = {};
ioctl(fd, /* DRM_IOCTL_BOGLUS_CMD */, bogus_req);
close(fd);
return ;
}
What could happen?
- If the kernel doesn’t check if tg is NULL, it tries to call tg->funcs->lock(), dereferencing NULL, and triggers a kernel panic.
References and Further Reading
- Commit Log: Linux Kernel Fix Commit
- CVE Entry: NVD - CVE-2023-52753
- AMD GPU Driver Documentation
- Linux DRM Subsystem
Mitigation & Recommendations
- Update your kernel! If you use AMD GPUs on Linux, especially in production or on a server, patch to a kernel version containing this fix.
- Limit user access to DRM/GPU device nodes (e.g., /dev/dri/card) if possible.
- Monitor kernel patch notes. DRM drivers develop quickly; regular updates and monitoring CVEs is critical for system security.
Conclusion
While CVE-2023-52753 may look subtle and low impact, it's a textbook example of why defensive programming—or "paranoia checks"—matter so much in the kernel. Even simple checks for NULL can block a whole class of reliability and security bugs. If you maintain machines with AMD GPUs on Linux, make sure you’ve applied this patch!
*Written exclusively for this post, simplifying technicalities for clarity and practical impact.*
Timeline
Published on: 05/21/2024 16:15:14 UTC
Last modified on: 05/29/2024 05:16:42 UTC