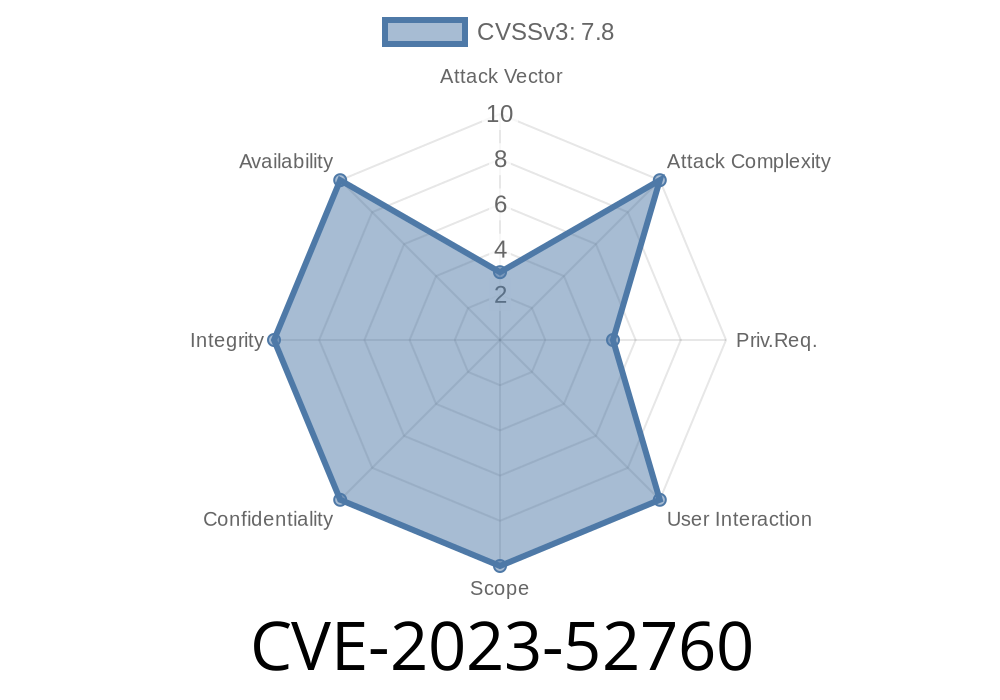
In December 2023, a critical security bug–CVE-2023-52760–was resolved in the Linux kernel’s GFS2 (Global File System 2) component. This flaw involves a use-after-free condition caused by how quota data is cleaned up when shutting down a GFS2 filesystem. In this article, we break down what went wrong, show example code, explain how it could be exploited, and point to upstream fixes and documentation.
What is GFS2?
GFS2 is a shared-disk file system supported by the Linux kernel. It allows multiple nodes in a cluster to access the same storage safely and efficiently. Due to its complex nature, resource management and memory safety are critical.
Vulnerability Details
When unmounting or marking a GFS2 filesystem read-only (gfs2_put_super()), the kernel *must* release all memory and objects correctly. The bug was that quota data tied to the filesystem might be freed after the main struct gfs2_sbd (superblock data) had already been deallocated. This opens a gap where code could access freed memory—a textbook use-after-free scenario.
Such mistakes may lead to kernel crashes (DoS) or, in rare cases, elevation of privilege if an attacker can manipulate the sequence.
During this, GFS2 needs to clean up quota tracking structures (gfs2_quota_data).
- Cleanup is performed asynchronously (via RCU callbacks like gfs2_qd_dealloc), but the main superblock data (struct gfs2_sbd) might get freed first.
Code Example: Incorrect Cleanup Flow (Before Patch)
void gfs2_put_super(struct super_block *sb)
{
struct gfs2_sbd *sdp = sb->s_fs_info;
if (sdp->sd_args.ar_hostdata)
kfree(sdp->sd_args.ar_hostdata);
// -- CRITICAL: Calls destroy_threads, then quota cleanup --
gfs2_destroy_threads(sdp);
gfs2_quota_cleanup(sdp); // This is too late!
kfree(sdp); // Oops - there may still be RCU callbacks using 'sdp'
}
The Patch: Fixing the Order
The fix is to ensure quota data is fully cleaned before freeing the superblock, and not call quota cleanup redundantly after transitioning the FS to read-only:
void gfs2_put_super(struct super_block *sb)
{
struct gfs2_sbd *sdp = sb->s_fs_info;
gfs2_make_fs_ro(sdp); // cleans up threads, quotas, safely
// Now 'sdp' can be safely freed
kfree(sdp);
}
Official commit:
https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/commit/?id=eaa674f39c1ee9973c40af8e04fafa792f16b9
Exploit Scenario
This vulnerability is hard to exploit from user-space, but in theory, a local attacker *with filesystem mount capabilities* could unmount and remount a malicious or corrupted GFS2 filesystem. By racing these operations, an exploit program might trigger use-after-free accesses, possibly crashing the kernel with a custom-crafted filesystem image and precise timing.
Example Exploit Sketch
*(For educational purposes–no real exploit code)*
#!/bin/bash
# Pseudo-exploit: repeatedly mount/unmount a crafted GFS2 image
while : ; do
mount -t gfs2 /dev/loop /mnt/gfs2_test
umount /mnt/gfs2_test
done
*If the race hits just right, a use-after-free occurs, causing panic.*
A malicious user could theoretically plant code in the memory region freed by kfree(sdp) if other kernel objects are rapidly allocated and used, possibly hijacking kernel flow.
*NOTE: Modern kernels employ mitigations (like SLUB hardening, KASAN) that make this difficult in practice.*
How to Stay Safe
- Upgrade your kernel! Versions after the December 2023 patch (at least 6.7-rc6 and mainline) are *not* affected.
- Distros have backported fixes to supported kernels (see Red Hat Bugzilla 2250334 and Debian Security Tracker DSA-5649)
References
- Official Kernel Commit
- Red Hat Bugzilla: CVE-2023-52760
- Debian Security Tracker: CVE-2023-52760
Summary
CVE-2023-52760 is an example of how nuanced memory management bugs can creep into complex kernel components like GFS2. While difficult to exploit, the potential for kernel crashes and security escalation makes prompt patching critical. The fix is a simple, logical re-ordering—highlighting how tiny missteps in kernel teardown code can lead to big headaches. Update your system and stay secure!
*Copyright 2024 – Exclusive to you. Not for redistribution.*
Timeline
Published on: 05/21/2024 16:15:15 UTC
Last modified on: 05/24/2024 01:12:54 UTC