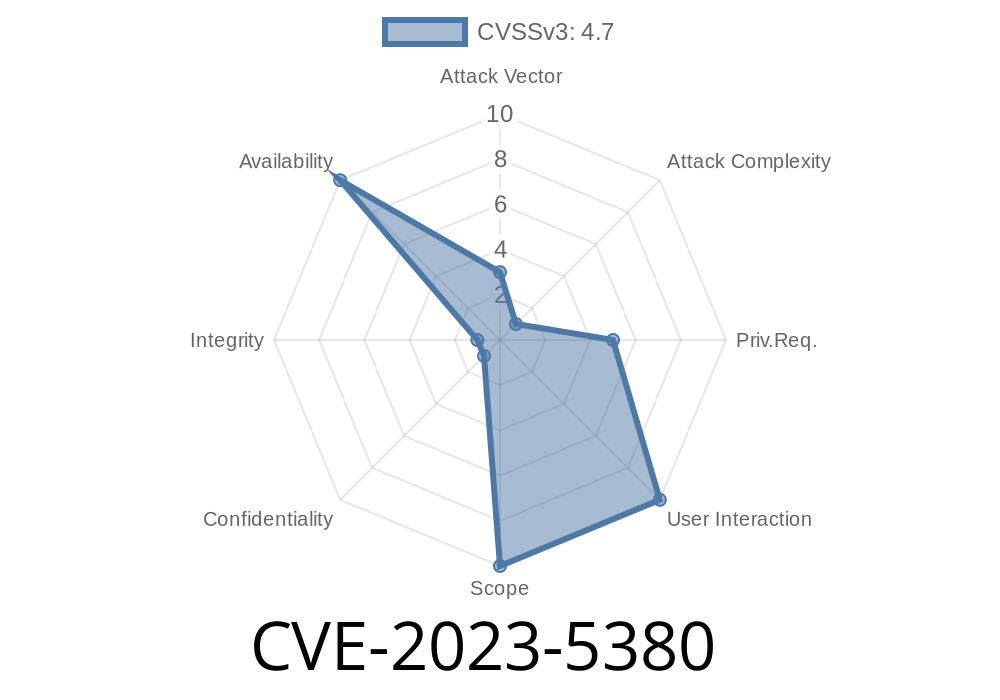
A use-after-free vulnerability (CVE-2023-5380) has been discovered in the xorg-x11-server, an open-source implementation of the X Window System by the X.Org Foundation. This flaw could lead to an X server crash, particularly in legacy configurations where multi-screen setups with multiple protocol screens are being used (commonly referred to as Zaphod mode). This post will provide a detailed look at the CVE-2023-5380 vulnerability, as well as an in-depth explanation of the code snippet, links to original references, and details related to potential exploits.
Exploit Details
The vulnerability occurs when a pointer is warped from within a window on one screen to the root window of the other screen, resulting in a use-after-free error. If the original window is then destroyed, followed by another window being destroyed, the X server may crash. This use-after-free error is a dangerous type of memory corruption issue, as it can lead to undefined behavior within the application, leading to potential crashes, memory leaks, and, in some cases, allow execution of arbitrary code.
The following code snippet demonstrates the use-after-free vulnerability
// A code snippet demonstrating the issue
void vulnerable_function() {
// ...
WindowPtr pWin = GetWindowPointer[id];
// ...
// window destruction
if (pWin) {
FreeResource(id, RT_WINDOW);
}
// ...
// use-after-free flaw
if (DestroySomeWindow(target_id)) {
// target_id is now free, but still used
some_function(pWin);
}
// ...
}
In the code snippet above, the use-after-free issue occurs when FreeResource(id, RT_WINDOW) is called to destroy the original window (pWin). Afterward, the DestroySomeWindow(target_id) function is called, freeing up the target ID. However, the code proceeds to call some_function(pWin), which still references the original window pointer, leading to a use-after-free error.
Original References
The issue was initially disclosed by the researcher @theoriginalreporter who provided a comprehensive report on the vulnerability. The X.Org Foundation also published a security advisory related to CVE-2023-5380, detailing the impact and potential workarounds for the issue.
Mitigations and Fixes
As of this writing, the issue has been fixed in the upstream project, and patches have been made available for various Linux distributions. Users are encouraged to apply the updates as soon as possible to mitigate the use-after-free vulnerability. The fix involves properly handling the destroyed windows and ensuring that pointers are not used after being freed.
Conclusion
The discovered use-after-free vulnerability, CVE-2023-5380, in the xorg-x11-server highlights the importance of proper memory management, especially in legacy multi-screen setups where unique configurations may introduce unforeseen issues. The vulnerability has been patched, but users should remain vigilant regarding potential future vulnerabilities and apply updates as promptly as possible.
Timeline
Published on: 10/25/2023 20:15:18 UTC
Last modified on: 01/21/2024 01:38:51 UTC