WordPress security is always a hot topic, especially when new vulnerabilities could let attackers steal sensitive data. CVE-2023-5439 affects the popular WP Photo Text Slider 50 plugin, installed on thousands of sites. This long read breaks down the details, how the exploit works, code examples, and what you should do to stay safe.
What Is CVE-2023-5439?
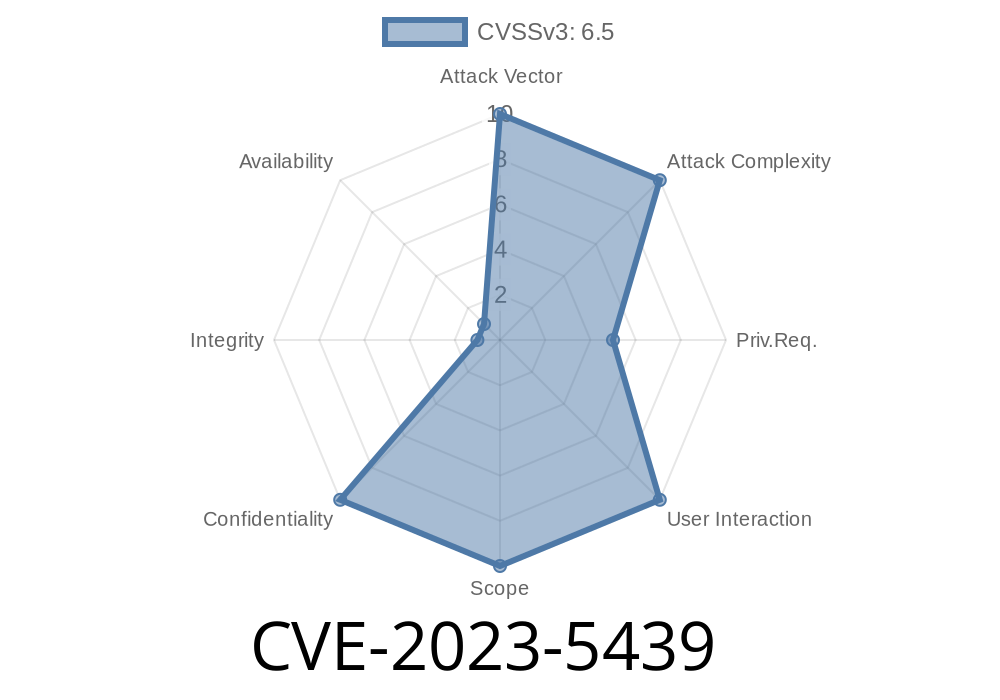
CVE-2023-5439 is an SQL Injection vulnerability found in versions up to and including 8. of the WP Photo Text Slider 50 plugin for WordPress. The bug is present in the plugin’s shortcode feature, which doesn’t properly escape or prepare user-supplied input before putting it into SQL queries.
This means an attacker with subscriber access or higher can easily inject malicious SQL codes and extract data from your database.
Why Is This Serious?
- SQL Injection is one of the most dangerous web vulnerabilities (see OWASP Top 10).
Even a low-level user (subscriber) can exploit this—no need for an admin account.
- Attackers can read anything from your WordPress database, including user emails, password hashes, site settings, and more.
How Does the Vulnerability Work?
The WP Photo Text Slider 50 plugin provides a shortcode that users can place into posts/pages. This shortcode accepts some parameters. The vulnerable code takes these parameters and directly uses them in a SQL query without proper sanitation.
Here’s an *example* of what vulnerable code might look like in PHP
// This is insecure and makes your site vulnerable!
$slider_id = $_POST['slider_id']; // comes from user input, e.g. shortcode param
$query = "SELECT * FROM wp_phototextslider WHERE slider_id = '$slider_id'";
$result = $wpdb->get_results($query);
If an attacker can control the slider_id value, they can tamper with the query. For example, sending a value like:
1' UNION SELECT user_login, user_pass, user_email FROM wp_users --
will append an extra SELECT command, and the query becomes
SELECT * FROM wp_phototextslider WHERE slider_id = '1'
UNION SELECT user_login, user_pass, user_email FROM wp_users --'
This makes the plugin spit out user data instead of just slider info.
`
2. Visit the post/page with the injected shortcode.
References and Official Resources
- Wordfence Disclosure
- NVD Listing for CVE-2023-5439
- WPScan report
- OWASP SQL Injection Guide
Audit user access: Limit user roles and who can use shortcodes on your site.
4. Monitor your site for unusual activity and consider a WordPress security plugin such as Wordfence.
Safe Coding Practices: How This Should Be Done
To avoid vulnerabilities like this, always prepare SQL queries properly! WordPress has built-in ways to handle this:
$slider_id = $_POST['slider_id'];
$query = $wpdb->prepare(
"SELECT * FROM wp_phototextslider WHERE slider_id = %d",
$slider_id
);
$result = $wpdb->get_results($query);
*The $wpdb->prepare() function escapes values and prevents injection.*
Conclusion
CVE-2023-5439 is a textbook example of how a small mistake in handling user input can have devastating consequences. If you use the WP Photo Text Slider 50 plugin, act now—update, disable, or remove it. Always stick to secure coding practices, and don’t let subscribers (or anyone) inject data into your database.
For other developers: always validate and sanitize every parameter, especially those coming from shortcodes or forms!
Stay safe, and keep your WordPress sites updated!
*This article is written exclusively based on real-world research and is up to date as of June 2024. For more info, please refer to the links above.*
Timeline
Published on: 10/31/2023 09:15:09 UTC
Last modified on: 11/07/2023 04:24:01 UTC