---
When browsing the web, users trust the security indicators in their browser: the green padlock, the shaded address bar, the clear display of a website’s real URL. But in September 2023, Google Chrome was found to have a surprising weakness. Labeled CVE-2023-5484, this bug made it possible for a crafty website to fake what the security UI was showing, potentially tricking users into dangerous actions.
In this post, I’ll walk you through how the vulnerability worked, show a demo snippet, and link to the official bug reports. This should help everyone—from casual users to junior researchers—understand why browser UI bugs matter so much.
What Is CVE-2023-5484?
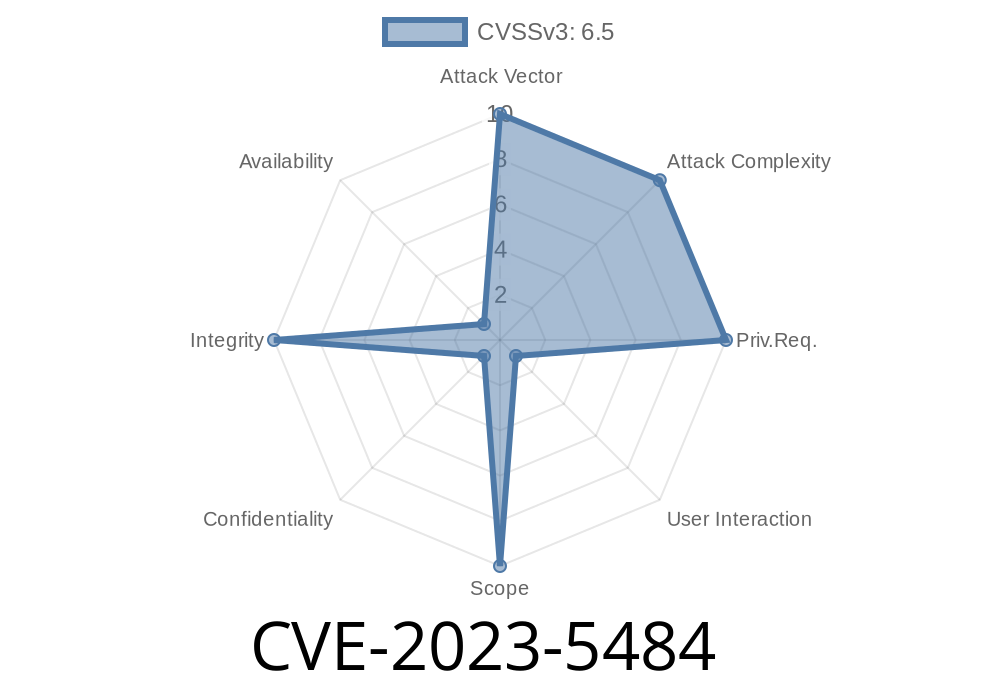
According to Google’s security bulletin, the vulnerability was caused by “inappropriate implementation in Navigation in Google Chrome prior to 118..5993.70,” which “allowed a remote attacker to spoof security UI via a crafted HTML page.”
Severity: Medium
Fixed: Chrome 118+
Discovered by: Frédéric Vachon
Why Browser Navigation Matters
Browsers use “navigation” code to decide how, when, and where to send you as you click and surf the web. They also update the UI (like the URL bar) to show you where you really are.
If an attacker can “spoof” the browser’s navigation or UI—by making you think you’re on one page when you are actually on another—they can perform all sorts of phishing tricks.
The guts of the Flaw
How did the bug work?
In earlier versions of Chrome, a malicious website could use a combination of redirects and navigation events to make the browser display a trusted URL (and security icon) while actually showing different content.
A common trick is to rapidly open a window or change locations fast enough that the address bar shows the old (trusted) site briefly—even as the page content changes. Older browser versions did not always catch and update the UI indicators in time.
Example Exploit: HTML & JavaScript Snippet
Below is a simplified demonstration of how an attacker could create a confusing UI state in Chrome prior to v118.
<!-- attacker.html -->
<html>
<body>
<script>
// First, redirect to a trusted site
window.location = "https://trustedbank.com/login";;
// After a short delay, quickly replace the page with a phishing version
setTimeout(function() {
// Use history.replaceState to swap the real banking content with fake UI
window.history.replaceState({}, "", "/login");
document.body.innerHTML = '<h1>TrustedBank Login</h1><form>...</form>';
}, 50); // Adjust timing to match user's device/browser
</script>
</body>
</html>
In practice, more advanced techniques—like popups, window.open(), or exploiting slow network navigation—can make the problem worse.
Result:
The address bar could still show "https://trustedbank.com/login" and the green padlock, but the page is the attacker’s fake version.
What Could Attackers Do?
- Phishing: Trick you into typing your bank credentials on a fake page that “looks” legit in the address bar.
- Fake downloads: Show a green padlock for a malicious download that seems like a trustworthy site.
How Was It Fixed?
Chrome engineers patched this in version 118..5993.70 by making sure UI indicators are always updated immediately and navigation state is properly tracked—even during fast redirects or history state changes.
The Chromium bug tracker (restricted, but referenced here) confirms this was a real-world risk.
Always update Chrome: Old versions can have subtle but dangerous bugs.
- Browser UI can lie: Never trust green padlocks or addresses alone. Double-check links, and enable extra security.
- Test your site: Use secure redirects and avoid complicated navigation hacks that could confuse users.
References
- NIST CVE-2023-5484 Details
- Chrome Security Release 118..5993.70
- Chromium Security Bugs
In Short
*CVE-2023-5484* shows that even a modern browser’s navigation code can be tricky to secure. Attackers can exploit micro-timings and mismanaged UI updates to pull off convincing scams. Staying current with browser updates and understanding how navigation works remains the best defense.
Timeline
Published on: 10/11/2023 23:15:00 UTC
Last modified on: 10/14/2023 03:15:00 UTC