Cisco has long been a trusted name in network security, but even the leaders are not immune from vulnerabilities. In early 2024, a new weakness was discovered and assigned CVE-2024-20353, affecting the management and VPN web servers of Cisco Adaptive Security Appliance (ASA) Software and Cisco Firepower Threat Defense (FTD) Software.
This post will help you understand the details, see how an attack works in practice, and learn what you can do to protect your network.
What Is CVE-2024-20353? A Quick Breakdown
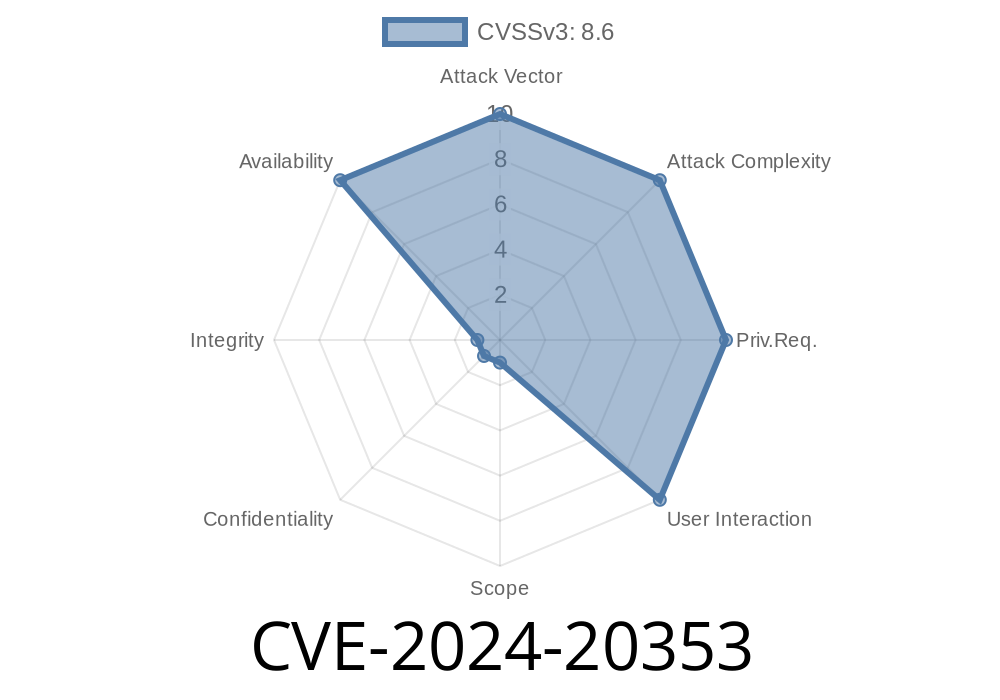
CVE-2024-20353 is a security vulnerability that allows a remote, unauthenticated attacker to crash Cisco ASA or FTD devices by sending a specially crafted HTTP request. The problem lies in how these devices process incoming HTTP headers during web-based connections—such as when someone uses the web portal to manage VPNs or firewall rules.
If exploited, this can trigger an unexpected device reload (restart), causing a temporary Denial of Service (DoS). During this time, administrators and end-customers could lose VPN or firewall connectivity.
A Closer Look: What Causes This Vulnerability?
At its core, the issue is incomplete error checking when the ASA or FTD software parses HTTP headers. If an attacker sends a malformed or purposely crafted HTTP header, the device doesn’t handle the error properly, resulting in a system crash.
Any remote attacker who can reach the affected ports (like web management or VPN portal) can trigger this attack without needing to log in.
Cisco Firepower Threat Defense (FTD) Software with its web interfaces enabled.
*Note: Not all features or configurations may be vulnerable. But if you expose management or VPN web ports to the internet, you’re at risk.*
See the Cisco Security Advisory for the full device list and details.
Attack Scenario (In Plain English)
1. Attacker identifies a vulnerable ASA or FTD device—usually by port scanning and checking responses from common web ports like 443 (HTTPS).
2. Attacker crafts a special HTTP request with one or more headers intentionally malformed, designed to trigger the device’s flawed parsing logic.
Attacker sends the malicious HTTP request to the device’s web server.
4. Device receives the request, tries to process the invalid header, and crashes due to the incomplete error validation.
Device reloads, causing a DoS event for all connected users and services.
*No authentication or internal access is required; attacks can be launched over the internet if the vulnerable web interfaces are exposed.*
Proof-of-Concept Code (Simplified)
Here’s a basic example demonstrating the concept using Python’s requests module. Warning: Never use this on systems you do not own!
import requests
# Target HTTPS management or VPN web portal
target = "https://<asa-ftd-vulnerable-host>";
# This header is intentionally malformed to simulate a potential crash
malformed_header = {
"Accept": "A" * 100000 # An abnormally long value; actual exploit headers may vary
}
try:
response = requests.get(target, headers=malformed_header, verify=False, timeout=5)
print("Request sent, status code:", response.status_code)
except Exception as e:
print("Error:", e)
*A real-world exploit may use different header manipulations (e.g., invalid characters, broken formatting), as discovered in security research.*
Signs of Attack
- Unexpected device reloads/crashes
Cisco has released fixes. See direct advisories and apply updates
- Cisco Security Advisory for CVE-2024-20353
Restrict Web Access
Don’t expose management interfaces (Web VPN, ASDM, etc.) directly to untrusted networks/the internet. Use access control lists (ACLs) or VPN.
Full References
- Cisco Security Advisory for CVE-2024-20353
- NIST National Vulnerability Database (NVD) Entry
- Cisco ASA and FTD Official Documentation
Exclusive Takeaways
CVE-2024-20353 shows that even basic interfaces like web management can present sizable risks. Rushed parsing routines or overlooked error-handling code can leave even world-class products open to simple but impactful denial-of-service attacks.
If you run Cisco ASA or FTD with web management or VPN services exposed, patch now and never allow direct internet access to sensitive interfaces! Always keep devices current and minimize attack surfaces.
Timeline
Published on: 04/24/2024 19:15:46 UTC
Last modified on: 04/26/2024 15:22:27 UTC