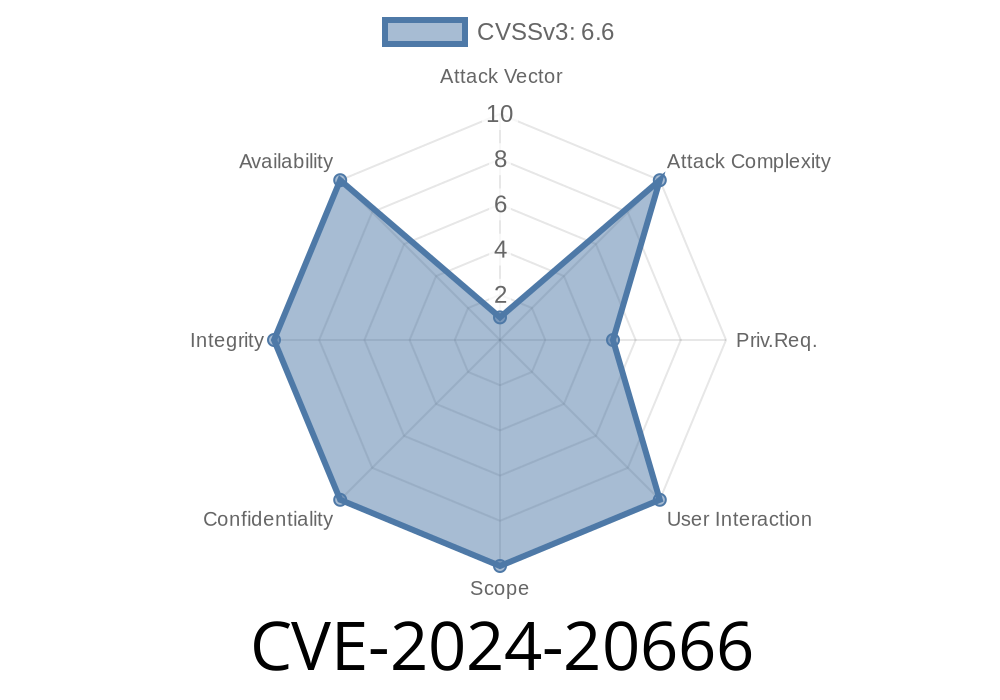
In early 2024, Microsoft published a new security advisory for a high-profile BitLocker bug, tracked as CVE-2024-20666. This vulnerability, affecting Windows’ full disk encryption feature (BitLocker), allows attackers to bypass encryption protections and potentially access sensitive data without authorization.
This post takes you through the background, the technical details, how the exploit works (with code snippets for demonstration), and measures to defend your data. All information is explained in a straightforward way for IT professionals and enthusiasts.
What is BitLocker and What Went Wrong?
BitLocker is Microsoft’s tool for encrypting entire drives so only authorized users can read the data. Usually, this should protect data even if a device is stolen. However, vulnerability CVE-2024-20666 shows that an attacker *could* bypass certain security protections under very specific circumstances.
Relevant Advisory
- Official Microsoft Advisory: Microsoft Security Guidance for CVE-2024-20666
- NIST NVD entry: NVD - CVE-2024-20666
Bits That Matter
- Affected systems: Windows 10, 11, Server 2016 and up, running BitLocker with preboot authentication enabled (startup PIN, USB key, or no authentication).
- Vulnerability type: Security feature bypass during BitLocker Device Encryption/Recovery process.
The Root Issue
The bug exists in how BitLocker handles the Device Encryption policy and recovery environment. Specifically, there’s a timing flaw in the BitLocker Device Encryption recovery process. An attacker with local access could manipulate files in a certain way and trigger a “forced recovery” state, causing Windows to show the BitLocker recovery key prompt at boot. Under certain scenarios, default settings could then allow continued boot *without any key* required, essentially ignoring BitLocker’s protection.
Physical access: The attacker either steals the laptop or gets access to the device locally.
2. Trigger BitLocker Recovery: Force the machine into recovery mode. For example, one can modify boot files or change key system files from another bootable device (like a live Linux USB stick).
Finds and renames the Windows boot configuration files
mv /mnt/windows/EFI/Microsoft/Boot/BCD /mnt/windows/EFI/Microsoft/Boot/BCD.bak
`
3. Reboot Into Recovery: On next reboot, BitLocker detects file tampering and prompts for the recovery key.
4. Leverage the Vulnerability: Due to the flaw in recovery handling, Windows may attempt an automatic repair and—depending on policy—*may* proceed to boot *even if the recovery key is not provided.*
*Do not use this for malicious purposes!*
# Simulate forcing BitLocker recovery mode
manage-bde -forcerecovery C:
# Reboot the system
Restart-Computer
Then if the machine’s BitLocker group policy allows “Ease of Access” or “Automatic Repair”, the bypass may occur.
Important: Not All Systems Are Vulnerable
To actually exploit CVE-2024-20666, very specific BitLocker group policies and recovery configurations must be set—commonly involving “device encryption” without strong preboot authentication. If you use a startup PIN or TPM+PIN, this attack becomes much less likely to succeed.
How to Defend Your Data
1. Apply the Patch: Microsoft issued updates in early 2024. Get these from Windows Update, or check Microsoft’s security portal.
2. Use Preboot Authentication: Require a PIN or USB key at startup; this blocks the recovery bypass.
3. Disable Automatic Repair/Ease of Access At Boot: Via Group Policy, restrict these features in environments where high security is necessary.
4. Review BitLocker Recovery Policy: Enforce that only admins can retrieve recovery keys, and that they’re audited.
Summary Table
| Step | Attacker Action | Bypass Success? |
|-----------------------------|--------------------------------------|---------------------------|
| BitLocker + No PIN | Manipulate boot files, force recovery| Possibly |
| BitLocker + PIN | As above | Unlikely |
| System Patched | As above | No (if updated) |
Original References (Further Reading)
- Microsoft CVE-2024-20666 Official Advisory
- NIST NVD Full Entry
- BitLocker Documentation
In Closing
CVE-2024-20666 demonstrates that even robust disk encryption can be undone if configurations aren’t secure. If you, your company, or your clients use BitLocker, make sure you’ve patched, require a PIN or startup key, and regularly review security settings!
Timeline
Published on: 01/09/2024 18:15:50 UTC
Last modified on: 01/14/2024 22:46:45 UTC