---
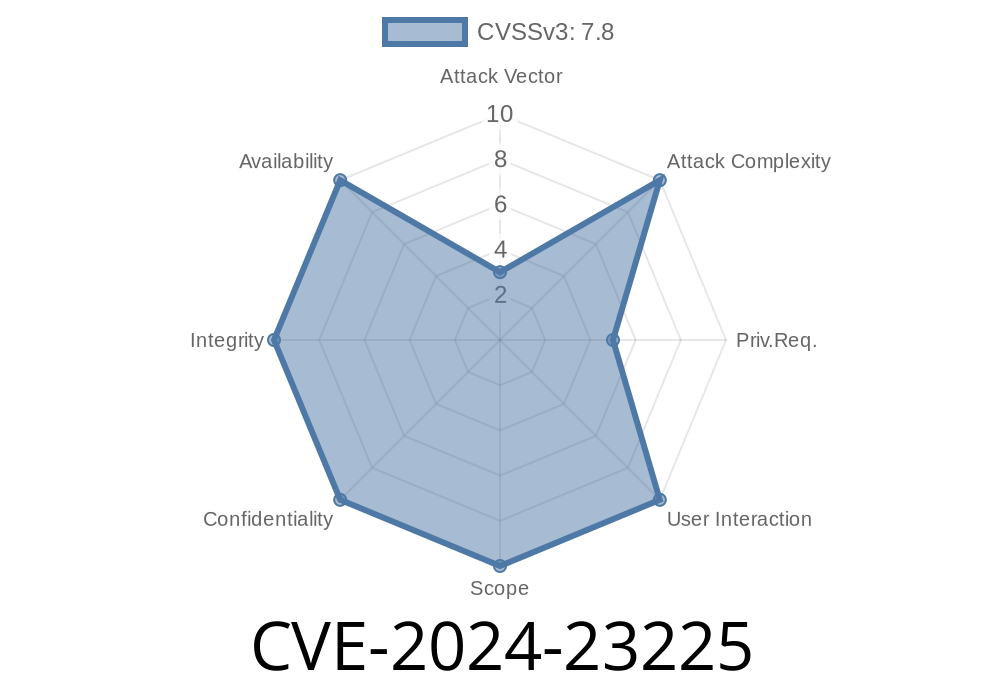
Apple devices are known for their strong security, but sometimes even big companies can face serious threats. A recent example is CVE-2024-23225, a vulnerability that shook the iPhone and iPad world in early 2024. In this exclusive long read, we’ll break down what happened, explain with simple terms and code, share how hackers could use it, and offer links for those who want to dig even deeper.
What Is CVE-2024-23225?
CVE-2024-23225 is a security flaw caused by a memory corruption bug inside Apple’s operating systems—including iOS and iPadOS. This bug was severe enough that Apple said attackers could use it to bypass kernel memory protections, which help keep the core of the system safe from malicious actions.
Public exploitation: Apple confirmed it may have been attacked in the wild.
- Impact: Hackers with *arbitrary kernel read & write* abilities could gain even more dangerous access.
How Did the Vulnerability Work?
This bug occurred because the system did not properly validate inputs or memory addresses when interacting with kernel memory. If an attacker had the ability to read and write anywhere in the kernel’s memory space, they could escape kernel-level security protections.
1. Memory Corruption
In computer systems, memory corruption can happen if a program reads or writes data outside the boundaries of what it’s supposed to use. This can change important variables or code, leading to crashes or allowing attackers to make the system do unintended things.
2. Improper Validation
The affected function or area of code did not check if memory operations were safe. For example, it didn’t check the given memory addresses properly before letting code access them.
Simplified Example Code
> Note: This is a representative example for educational purposes.
// Example of unsafe kernel memory write
void vulnerable_kernel_function(void* user_ptr, size_t len) {
char kernel_buffer[256];
// No proper validation of len or user_ptr!
memcpy(kernel_buffer, user_ptr, len);
}
An attacker with control over user_ptr and len could overwrite parts of memory they shouldn’t touch.
How Attackers Exploited It
This vulnerability is valuable to attackers who already have some level of access, especially those who have already gained code execution in the kernel (for example, as part of a "jailbreak" chain).
Step-by-step Exploitation
1. Obtain kernel read/write primitive:
Use another exploit or bug to get code running with the ability to read and write memory at will in the kernel address space.
Trigger CVE-2024-23225:
Direct the buggy code to specific, sensitive kernel memory regions. Change kernel structures that enforce memory protections (such as code signing or security flags).
Bypass protections:
With modified security settings, they could execute arbitrary code, hide their presence, or install persistent malware.
A Realistic Exploit Scenario
While the public technical details are limited, here’s how a malicious exploit could look in simplified pseudocode:
# Attacker already has kernel R/W primitives (e.g., via another bug/exploit)
def exploit_cve_2024_23225(kmem_write, kmem_read):
# Address of security flag as discovered by reverse engineering
security_flag_address = xfffffff007123456
# Read current security flag value
original_flag = kmem_read(security_flag_address)
# Disable protection by writing malicious value
kmem_write(security_flag_address, x)
# Now attacker can run unsigned code or access protected resources
# ...
# Restore original value to hide tracks
kmem_write(security_flag_address, original_flag)
*Note: Actual addresses and details would vary by iOS version and device, requiring reverse engineering.*
Apple’s Fix – What Changed?
Apple fixed this problem by improving validation in the code—meaning more checks are made before kernel memory is accessed or changed.
From their official release notes
> "A memory corruption issue was addressed with improved validation. This issue is fixed in iOS 16.7.6 and iPadOS 16.7.6, iOS 17.4 and iPadOS 17.4."
>
> (Source: Apple Security Updates)
What does ‘improved validation’ mean?
It means double-checking that any request to read or write kernel memory is safe. For example, verifying that pointers are pointing to allowed places, or that only privileged code can alter certain memory regions.
iPadOS 17.3.1 or earlier
If you had not updated to iOS 16.7.6/17.4 or iPadOS 16.7.6/17.4, your device could be vulnerable.
What Should You Do?
1. Update your iPhone/iPad immediately to the latest iOS/iPadOS version.
2. Don’t jailbreak your device—jailbroken systems make it much easier for attackers to use this kind of bug.
References and More Reading
- Apple Security Update – CVE-2024-23225 Details
- National Vulnerability Database: CVE-2024-23225 Entry
- Apple Security Updates List
Conclusion
CVE-2024-23225 is an example of how dangerous memory corruption bugs can be, especially in the kernel—the heart of your device’s operating system. Apple acted quickly, but this shows why keeping your device updated is so important.
If you want your iPhone or iPad to remain safe, always stay on top of the latest updates, and be cautious about what software you install. Attackers are always hunting for vulnerabilities—but simple habits can keep you a step ahead.
Timeline
Published on: 03/05/2024 20:16:01 UTC
Last modified on: 03/19/2024 01:00:01 UTC