In early 2024, Microsoft disclosed a crucial security vulnerability tracked as CVE-2024-26175. This vulnerability affects Secure Boot—a cornerstone of modern Windows security. Secure Boot is designed to prevent rogue software from loading during the system start-up process. If bypassed, attackers can gain deep, persistent control over a system—sometimes called “bootkits.”
In this post, we’ll break down exactly what CVE-2024-26175 is, how the exploit works, offer code snippets for better understanding, and provide steps to protect yourself. Everything is kept to simple language and is based on authoritative references.
What is Secure Boot?
Secure Boot is a firmware security standard. It makes sure a computer boots only with software trusted by the PC maker or the user. It’s part of the Unified Extensible Firmware Interface (UEFI) standard.
If malware or altered bootloaders try to sneak in, Secure Boot checks signatures and blocks them.
Description of CVE-2024-26175
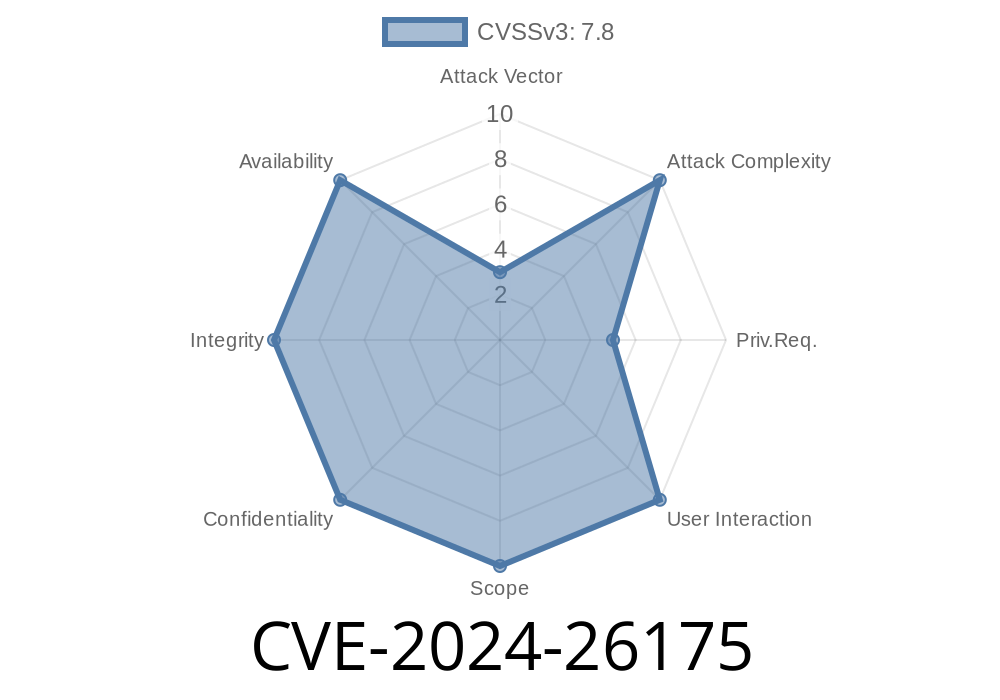
CVE-2024-26175 is a security feature bypass within the Secure Boot process, assigned a high severity rating. An attacker with sufficient privileges could exploit this bug to bypass Secure Boot policy enforcement, letting unauthorized or malicious code run during early boot—before the operating system starts.
This lets malware such as rootkits or bootkits load invisibly, making detection and removal *extremely* tough.
1. Malicious Boot Image Injection
If an attacker gains *administrator* privilege or physical access (think: someone with access to your machine or an already compromised system), they can install a malicious bootloader or modify existing boot files.
2. Policy Bypass
Due to improper verification logic, the Secure Boot process doesn’t correctly validate certain components, including old or specially crafted bootloaders.
3. Chain of Trust Breaks
Once Secure Boot is tricked, the system trusts the rogue bootloader and loads it on reboot, handing over system control.
Exploit Example (Hypothetical)
WARNING: For educational purposes only. Do not attempt unauthorized actions on systems you do not own.
Below is a simplified PowerShell-like pseudocode showing how an attacker might exploit this vulnerability after gaining admin rights:
# Example: Replacing Secure Bootloader with a malicious one
# 1. Take ownership and grant permission
takeown /f C:\EFI\Microsoft\Boot\bootmgfw.efi
icacls C:\EFI\Microsoft\Boot\bootmgfw.efi /grant Administrators:F
# 2. Replace the legitimate bootloader with a malicious version
copy C:\malware\evil_bootmgfw.efi C:\EFI\Microsoft\Boot\bootmgfw.efi /Y
# 3. Reboot to load malicious bootloader
shutdown /r /t
*Note: In real-life attacks, the process is more complex and the bootloader would be specially crafted to take advantage of CVE-2024-26175’s bypass flaw.*
How Was This Found?
Security researchers at Microsoft and independent experts identified the vulnerability. Details are published in the official Microsoft advisory:
- Microsoft Security Update Guide - CVE-2024-26175
Some additional references
- Microsoft Tech Community post
- NIST NVD Entry
Run Windows Update to install the security fix for CVE-2024-26175.
2. Update UEFI/BIOS:
Conclusion
CVE-2024-26175 is a powerful reminder of the importance of patching not just software, but also firmware and security settings. Secure Boot is an essential line of defense—if it’s broken, system security can be severely compromised.
Further Reading & Official References
- Microsoft Security Advisory CVE-2024-26175
- NIST National Vulnerability Database
- Secure Boot Documentation (Microsoft)
Timeline
Published on: 04/09/2024 17:15:36 UTC
Last modified on: 04/10/2024 13:24:00 UTC