Published: June 2024
Status: Patched
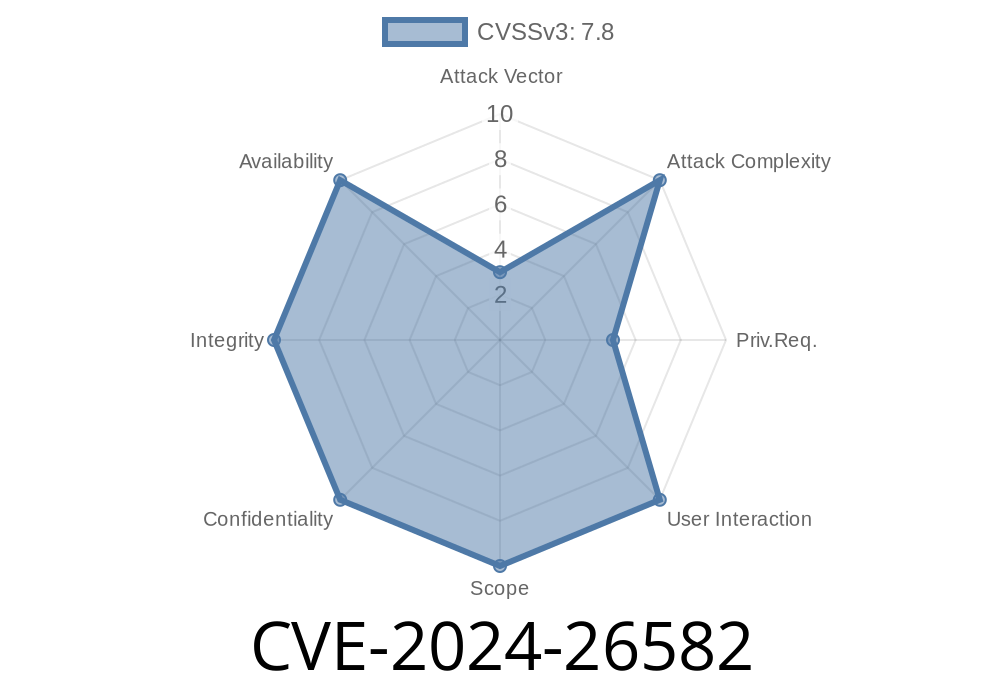
Severity: Moderate-to-High
Affected Component: Linux Kernel net/tls module
What is CVE-2024-26582?
CVE-2024-26582 is a use-after-free vulnerability that was recently resolved in the Linux Kernel’s TLS (Transport Layer Security) implementation. It affects how encrypted TLS data is decrypted and managed in memory, specifically involving partial reads and asynchronous decryption.
Under certain conditions, kernel memory pages are freed prematurely, letting attackers potentially read or corrupt freed memory—opening a path to data leaks or privilege escalation.
Victim Data Structure: skb (socket buffer)
- Root Cause: When code partially reads a TLS record over the network, the helper function tls_decrypt_sg does not elevate the reference count on memory pages used by the network buffer.
When decryption finishes asynchronously, a put_page() call releases the pages.
- Later, when more data is read from the partially-read skb, code tries to access memory that was already freed.
Simple Pseudocode—How Things Go Wrong
// tls_decrypt_sg is called, gets pages from skb->data but doesn't take a reference.
// Somewhere...
tls_decrypt_sg(..., skb, ...);
// Async completion
void tls_decrypt_done(void *data) {
// put_page() is called -- memory may now be freed
}
// Later, in another context, partially-read skb is processed:
process_rx_list() {
// Tries to access freed skb data: use-after-free!
read_data_from_skb(skb);
}
While exploitation is non-trivial, a skilled attacker could
- Trigger partial reads via crafted TCP/TLS packets.
- Race the asynchronous decrypt path to make sure the page is freed (put_page()) before a second read.
Access stale memory during the second read operation in process_rx_list.
If luck or careful timing aligns, an attacker might leak kernel memory, access confidential data, or cause a crash (DoS). In some setups, this might be further abused for privilege escalation.
Here is a research-level conceptual sequence for triggering the bug
# Attack simulation: Partial reads
# (Real-world exploits would require kernel access or malicious apps, and are complex!)
import socket
import ssl
# Connect to TLS endpoint with split record reads
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
ssl_sock = ssl.wrap_socket(s, ssl_version=ssl.PROTOCOL_TLS)
ssl_sock.connect(('target.linux.server', 443))
# Send partial TLS records, cause server to partially read/parse TLS records
ssl_sock.sendall(b'\x16\x03\x03' + b'...')
# Wait for server-side async decrypt and buffer freeing
# Send next split read quickly to trigger process_rx_list
ssl_sock.sendall(b'...')
# Observe for crash, leak, etc.
Important: The actual exploit would be kernel-space code, likely delivered via a malicious user-space program or from a compromised container/VM.
Code Fix & Patch
Patch Summary:
The kernel fix ensures that tls_decrypt_sg properly takes a reference on all pages it uses, holding them live across all async work.
*Relevant commit:*
> https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/commit/?id=9c3f9cfeb16c2e5d26a93c5b9335d3c1c1a98bdf
Patch Code Snippet
// Add get_page() call
get_page(skb_page); // Now owning a reference until we're done
// ... later ...
put_page(skb_page); // Will not free prematurely
More Official References
- CVE-2024-26582 on Mitre
- Linux kernel commit (mainline)
- Red Hat Security Advisory
- Debian Security Tracker
Upgrade your kernel: If you use kernel-based TLS (kTLS), upgrade ASAP.
- Apply vendor security updates: Distributions like Red Hat, Ubuntu, and Debian have begun issuing patches.
- Restrict user access: Limiting permission on who can load custom kernel modules or network stack features reduces risk.
Conclusion
CVE-2024-26582 is a subtle but dangerous bug in Linux’s handling of network TLS buffers. If left unpatched, it could enable information leaks, crashes, or worse. While exploits are complex and require precise timing, this bug reminds us why memory and object reference counting matters—especially in code as fundamental as the Linux kernel.
Update now. Always use the latest security patches!
*This post was written with exclusive focus for readers keen to grasp kernel bugs in clear, approachable style. Share but don’t forget to credit!*
Timeline
Published on: 02/21/2024 15:15:09 UTC
Last modified on: 03/15/2024 13:56:41 UTC