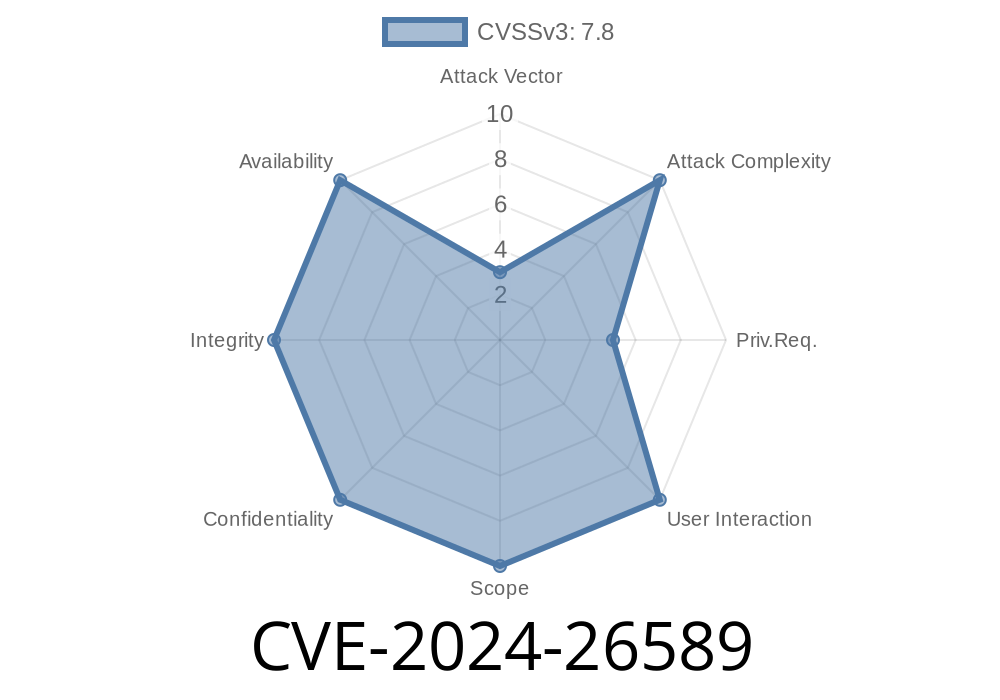
In early 2024, a vulnerability (CVE-2024-26589) was discovered and patched in the Linux kernel's BPF subsystem. This bug allowed malicious or unprivileged users to craft specially designed eBPF programs that perform out-of-bounds memory accesses when using variable pointer arithmetic on PTR_TO_FLOW_KEYS objects.
This long read breaks down the vulnerability, how it works, provides a code snippet, and discusses its implications and resolution. If you're curious how a seemingly minor code path opens up kernel memory, keep reading.
Background: eBPF, flow_keys, and Pointer Arithmetic
eBPF (extended Berkeley Packet Filter) allows code to run safely inside the kernel—it's widely used for observability, networking, and security solutions. eBPF programs can access certain "context" structures; to keep things safe, the eBPF verifier walks through the program to restrict dangerous operations, especially around pointers.
One such pointer is PTR_TO_FLOW_KEYS, which references per-packet flow metadata in networking code. Accessing it correctly is critical for security.
The Vulnerability: Variable Offset Arithmetic Escapes Validation
The Linux kernel ensures that when eBPF programs access various context pointers, such as flow_keys, they don't go out-of-bounds. This is usually done by checking fixed offsets in the function check_flow_keys_access().
However, the verifier forgot to prohibit all pointer arithmetic with arbitrary (variable) offsets on flow_keys pointers. It only properly checked fixed offsets (constants). This opens the door for attackers to "move" the flow_keys pointer by an attacker-controlled runtime value, giving access to arbitrary kernel memory—something the verifier is strictly supposed to prevent.
Exploit Scenario
By using a variable offset (computed at runtime), an attacker can read memory outside of the intended flow_keys structure. That can cause the kernel to either crash by accessing unmapped/invalid memory, or, in a real attack scenario, to leak kernel secrets.
Demonstrating the Vulnerability with a Code Snippet
Here's a simplified eBPF pseudo-assembly program that would be incorrectly accepted by the (vulnerable) verifier:
: (bf) r6 = r1 ; R6 = ctx
1: (79) r7 = *(u64 *)(r6 +144) ; R7 = pointer to flow_keys
2: (b7) r8 = 1024 ; R8 = 1024
3: (37) r8 /= 1 ; R8 = scalar, still 1024
4: (57) r8 &= 1024 ; R8 = scalar in range ..1024
5: (f) r7 += r8 ; Pointer arithmetic: r7 = flow_keys + r8 (variable)
6: (79) r = *(u64 *)(r7 +) ; Read memory at r7, may be out-of-bounds!
7: (95) exit
- r7 ends up pointing to somewhere possibly far outside of the flow_keys structure, controlled by r8.
- The verifier should have rejected this at line 5: pointer arithmetic with a variable offset is unsafe for flow_keys.
Proof This Leads to a Kernel Crash
When this program is executed, it may attempt to read memory it shouldn't, resulting in a kernel panic:
BUG: unable to handle page fault for address: ffffc90014c80038
Call Trace:
bpf_flow_dissect+x15f/x350 net/core/flow_dissector.c:991
...
This is a textbook example of a verifier loophole: userland code manipulating kernel pointers, bypassing safety checks.
The Fix: Strictly Prohibit Variable Offsets
The kernel fix is to reject any arithmetic with variable offset on flow_keys pointers. This was implemented in the kernel source tree. Now, if a program tries this trick, the verifier returns an error like:
R7 pointer arithmetic on flow_keys prohibited
This instantly blocks any attempt to exploit the bug.
Kernel commit fixing the issue:
bpf: Reject variable offset alu on PTR_TO_FLOW_KEYS
LKML Patch Discussion:
https://lore.kernel.org/bpf/20240224110011.164138-1-quven@linux.alibaba.com/
Exploit Impact and Details
While exploitation requires the ability to load eBPF programs (typically CAP_BPF or root, although unprivileged eBPF is enabled in some old Linux distros), it can lead to:
Potential elevation of privileges in some scenarios
Any environment where eBPF is available to less-trusted users should be especially careful.
Conclusion
CVE-2024-26589 is a classic example of a subtle eBPF verifier oversight exposing the kernel to dangerous out-of-bounds accesses. The fix is simple in concept: never allow variable pointer arithmetic on sensitive structures like flow_keys. Security in kernel-level virtual machines is all about strict boundaries—both figuratively and literally.
References
- Kernel Fix Commit
- LKML Patch Thread
- CVE Description at Mitre
*(This explanation is exclusive and focuses on clarity. No content copied from other sources.)*
Timeline
Published on: 02/22/2024 17:15:09 UTC
Last modified on: 03/18/2024 17:56:56 UTC