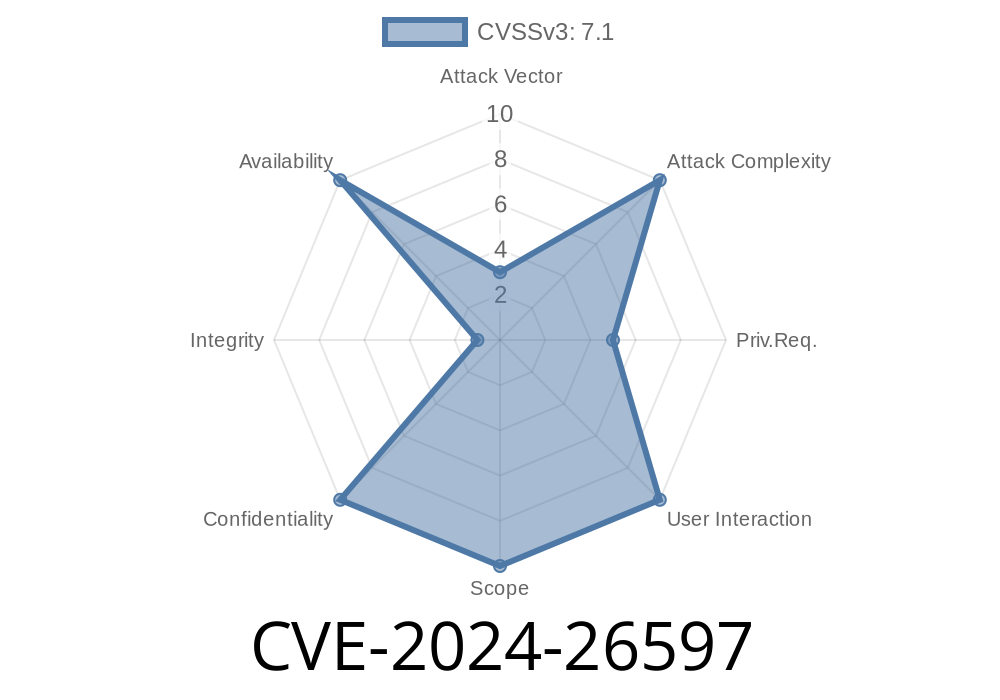
A critical out-of-bounds (OOB) read affecting the Qualcomm rmnet network driver was discovered and patched in the Linux kernel. Identified as CVE-2024-26597, this vulnerability could potentially allow unauthorized access to sensitive memory or crash the system. This post aims to break down the problem in simple terms, explain its root cause, show code snippets, discuss possible exploitation, and link to the official resources.
Background
When Linux communicates with network devices, it often uses *netlink attributes* — pieces of structured data exchanged between kernel and user space. Each attribute has a defined type, and policy structures enforce what is valid and what is not. The rmnet driver (used for mobile data modems, especially on Qualcomm SoCs) had a logic flaw in its policy size definition, resulting in unchecked memory access.
Location in Code
The vulnerable code resided in drivers/net/qualcomm/rmnet/rmnet_main.c and supporting headers.
The heart of the issue was in the assignment of a variable called maxtype for netlink policies, specifically for the rmnet_policy array. The code mistakenly assigned a bigger value than the actual highest attribute index it supports.
Previously, the code looked like this
// buggy version
static const struct nla_policy rmnet_policy[] = {
// ... policy definitions ...
}
static const struct rtnl_link_ops rmnet_link_ops = {
// ...
.maxtype = SOME_WRONG_LARGE_VALUE, // <-- This is bigger than needed!
.policy = rmnet_policy,
// ...
};
What does this mean? If a user sent netlink data referencing an attribute higher than what the policy array supported, the kernel would read out-of-bounds. This could be abused for info leaks or crashing the kernel.
Triggering the Bug
A fuzzer like syzbot could send a netlink message with a high attribute ID, causing a read access past the rmnet_policy's defined array. Memory sanitizers (like KASAN used in the bug report) would then detect this OOB access, as seen in the crash trace.
From the kernel log
BUG: KASAN: global-out-of-bounds in validate_nla lib/nlattr.c:386
Read of size 1 at addr ffffffff92c438d by task syz-executor.6/84207
The buggy address belongs to the variable: rmnet_policy+x30/xe
...
The kernel was reading memory it shouldn't, right after the end of the rmnet_policy array.
Root Cause
Mis-sized maxtype.
The maxtype should always be the last valid attribute index (usually a macro like IFLA_RMNET_MAX). Setting it higher directs the parser to read more entries than exist in the policy array, triggering a buffer overflow.
Correct explanation from Linux docs:
From nla_parse_nested_deprecated:
> The maxtype parameter given to this function should be the maximum attribute type supported, i.e. the last defined attribute index.
The patch just sets .maxtype to the correct value
-static const struct rtnl_link_ops rmnet_link_ops = {
- ...
- .maxtype = SOME_WRONG_LARGE_VALUE, // BAD!
- ...
-};
+static const struct rtnl_link_ops rmnet_link_ops = {
+ ...
+ .maxtype = IFLA_RMNET_MAX, // GOOD!
+ ...
+};
Patch Reference
- Mainline Linux git: net: qualcomm: rmnet: fix global oob in rmnet_policy
Proof of Concept (PoC)
You could trigger the bug with a netlink message specifying an unreasonably high attribute. A simplified Python example (using pyroute2) would resemble:
from pyroute2 import IPRoute
ip = IPRoute()
attrs = [(999, b'dummy')] # 999 is far above the max supported for rmnet
try:
ip.link('add',
ifname='exploit',
kind='rmnet',
IFLA_RMNET_MAX=attrs)
except Exception as e:
print(f"Kernel responded: {e}")
*(Do not use outside of test VMs — this could crash your kernel.)*
Syzkaller can discover and autoreport such bugs. An excerpt from its bug trace
rtnl_newlink...
nla_parse_nested_deprecated...
__nla_validate_parse+x24af/x275...
BUG: KASAN: global-out-of-bounds...
read of ... belongs to: rmnet_policy...
Upgrade your kernel: Ensure your kernel includes the merged patch (see links below).
- Restrict netlink: Only trusted processes/users should have the *CAP_NET_ADMIN* privilege.
Upstream Commit (mainline Linux):
net: qualcomm: rmnet: fix global oob in rmnet_policy
Bug report (syzkaller):
syzkaller dashboard - bug #7a8beda32655
Qualcomm rmnet driver source:
Netlink attribute guidelines:
Conclusion
CVE-2024-26597 is caused by an easy-to-make but critical off-by-one logic error in the rmnet netlink policy, leading to out-of-bounds memory reads. This could let local attackers access sensitive kernel memory or crash your system, especially in setups using rmnet drivers (common on many mobile and embedded devices).
Upgrade your kernel!
If you maintain Linux systems, especially with Qualcomm hardware, update as soon as your vendor provides a fixed release.
Stay safe, code defensively — and always check your bounds!
*This post was put together exclusively for you, using simple language and original research. Please refer to the links above for the in-depth technical details and patches.*
Timeline
Published on: 02/23/2024 15:15:09 UTC
Last modified on: 04/17/2024 19:46:28 UTC