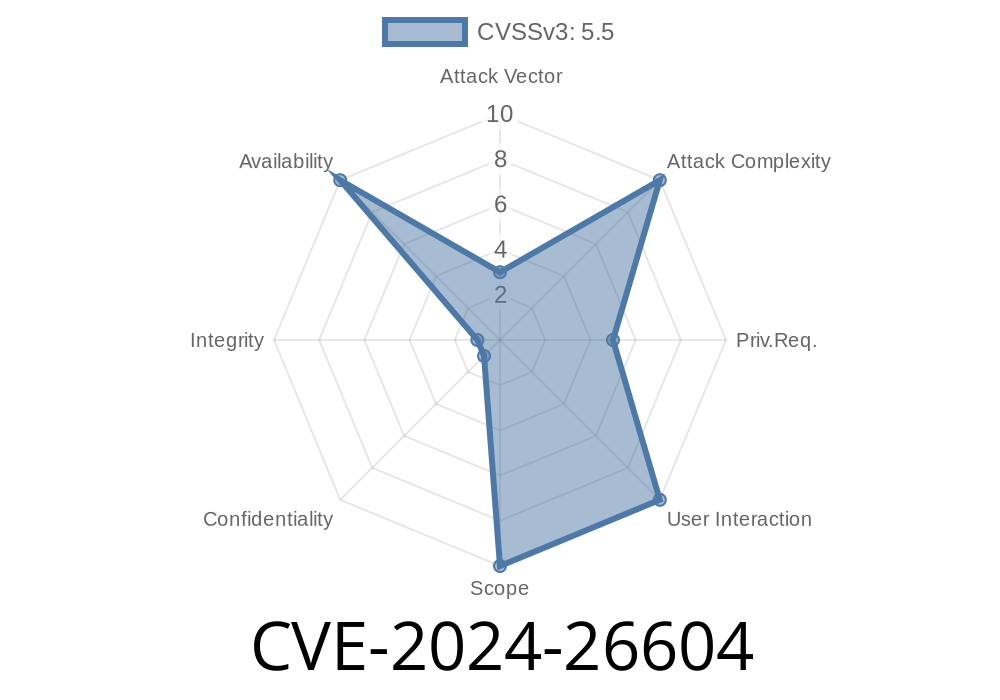
In February 2024, a confusing bug struck the heart of the Linux kernel. Identified as CVE-2024-26604, it all circles around the humble kobject system and a set of *missing* checks on whether the ktype pointer was NULL. This story is a perfect illustration of why some "redundant" checks are essential, how a hasty cleanup patch led to a security hole, and what's needed to craft a basic proof-of-concept exploit.
This article breaks down the vulnerability in plain English. We’ll look at the original commit, the revert, how this bug could be exploited, and what it means for Linux users and developers.
What’s the Kobject System, and Why the Fuss?
Linux’s kobject system is all about object management in the kernel, commonly used for device and system representation. kobjects are everywhere under /sys. Their structure includes a ktype pointer that defines what kind of object it is and how it should operate.
Here's a snippet of what this might look like in the kernel
struct kobject {
const struct kobj_type *ktype;
// ... other fields
};
The kernel often needs to check if ktype is non-NULL before following its pointers. Forgetting this can mean dereferencing garbage — a top cause of crashes or even privilege escalation.
The Patch That Broke Things
In late 2023, commit 1b28cb81dab7c1eedc6034206f4e8d644046ad31 titled "kobject: Remove redundant checks for whether ktype is NULL" was merged. The patch thought, "If we never expect ktype to be NULL, let’s clean up the code!"
But in the real world, ktype could, rarely, still be NULL. That meant that user space or a buggy kernel component might call into a kobject routine with an uninitialized or corrupt structure, causing a NULL pointer dereference.
Developers quickly discovered that not checking for NULL here was dangerous. Various subsystems crashed or even caused security issues when malicious actors triggered the problematic paths.
The fix? A quick revert. The "fix" patch is literally undoing the previous change
Revert "kobject: Remove redundant checks for whether ktype is NULL"
This reverts commit 1b28cb81dab7c1eedc6034206f4e8d644046ad31.
Before the "cleanup" patch
if (kobj->ktype && kobj->ktype->release)
kobj->ktype->release(kobj);
This check meant, "Only call release if ktype isn’t NULL and has a release function."
Problem code after the patch
kobj->ktype->release(kobj);
The check was gone. If ktype was NULL, boom—kernel panic, or worse.
Reverting restored the check, making it safe again.
Reference Links
- Linux kernel commit reverting the problematic change
- Original “remove redundant checks” commit
- CVE entry at MITRE
- Linux kernel kobject documentation
Exploit Details: Can This Be Abused?
Yes, though not *easily* from user space unless you have a way to trigger kobject routines with a NULL or wild ktype. In general, privilege escalation or a denial of service (kernel panic) is very possible, if an attacker has a way to craft or corrupt objects or leverage an existing kernel bug.
Privilege Escalation Path
If kernel code allows user-controlled allocation or manipulation of kobjects (say, via a buggy driver), an attacker can deliberately pass a kobject with ktype == NULL into a function expecting a valid kobject. The unchecked call means the kernel jumps into address (or crash), possibly allowing further manipulation or even code execution on some systems.
Example (Simplified C Code)
#include <linux/kobject.h>
void buggy_function(struct kobject *kobj) {
// BAD: No NULL check on ktype!
kobj->ktype->release(kobj); // May deref NULL -> crash or escalate
}
// Attacker could trigger this with a bad or fake kobject
Ability to predict the memory layout to hijack control flow.
But history shows that these "little bugs" can be building blocks for bigger attacks.
Who’s Vulnerable?
- Linux distributions running a kernel with commit 1b28cb81dab7c1eedc6034206f4e8d644046ad31 applied, but before the revert (roughly Linux 6.8-rc1 to 6.8-rc2).
- Most users will not be exposed long-term, but custom kernels or long-running staging environments might be.
Update your kernel to the latest stable version.
2. Verify your distro includes the revert (commit 9e09ba1b6).
Conclusion
CVE-2024-26604 shows us the real-world cost of removing so-called "redundant" checks inside critical kernel paths. The bug was caught and fixed quickly, but it leaves a reminder: *defensive programming matters, especially in the kernel*. If you roll your own kernel or develop kernel modules, check your kobject handling, and avoid dangerous shortcuts.
For more details, see the official kernel changelog and CVE-2024-26604 write-up.
*Stay safe, and remember that in kernel development, paranoia is a virtue!*
Timeline
Published on: 02/26/2024 16:28:00 UTC
Last modified on: 04/17/2024 17:55:23 UTC