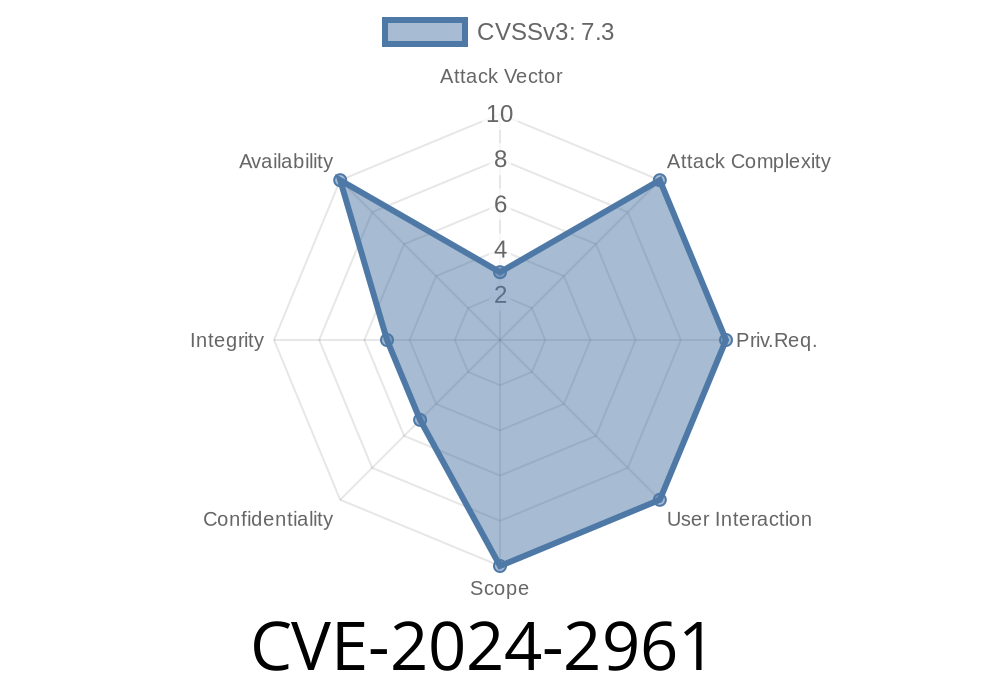
The open-source world was hit by a subtle but critical vulnerability in GNU C Library (glibc) affecting the iconv() function. Registered as CVE-2024-2961, this bug can let attackers overwrite memory buffers by exploiting incorrect output buffer size checks during conversion to the ISO-2022-CN-EXT character set. This post explains what it means, demonstrates a code snippet, references official sources, and dissects how someone could exploit it.
What is iconv()?
The iconv() function is a standard utility in glibc for converting text between different character sets (“encodings”). Programs often use it to make sure text displays correctly, regardless of the user’s system or language.
CVE-2024-2961 Explained Simply
In versions 2.39 and earlier, if you ask iconv() to convert incoming text into the ISO-2022-CN-EXT character set, the function might write up to 4 bytes past the end of the output buffer you gave it.
Could crash your program (Denial of Service)
- Or possibly overwrite a neighboring variable, leading to information leaks or even code execution depending on what the overwritten data is
The Bug in Short
Let's say you allocate a buffer of the "exact" needed size, as recommended. If you then pass a string to iconv() for conversion to ISO-2022-CN-EXT, iconv() might actually write up to 4 additional bytes, corrupting memory.
Look at this simple but vulnerable C program
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <iconv.h>
int main() {
// Sample input
const char *input = "hello";
size_t inlen = strlen(input);
// Set up conversion: any encoding -> ISO-2022-CN-EXT
iconv_t cd = iconv_open("ISO-2022-CN-EXT", "UTF-8");
if (cd == (iconv_t)(-1)) {
perror("iconv_open");
return 1;
}
size_t outlen = inlen * 10; // generous estimate
char *output = malloc(outlen);
char *outptr = output;
size_t res = iconv(cd, (char **)&input, &inlen, &outptr, &outlen);
if (res == (size_t)-1)
perror("iconv");
printf("Converted %ld bytes\n", outptr - output);
iconv_close(cd);
free(output);
return ;
}
Now, suppose you strictly calculate the output buffer (e.g., per byte, or according to the documentation). Due to the bug, iconv() may write up to 4 bytes past output, corrupting memory; this could overwrite variables or crash the program.
Feed text to a program that uses iconv() to convert to ISO-2022-CN-EXT.
2. Cause iconv() to overrun a carefully-placed buffer. If sensitive values (function return addresses, configuration flags, or user data) are next to the output buffer, the attacker’s data could overwrite them.
3. This might lead to information leak, crash, or worse – execution of attacker’s code (if the environment is right).
Note: glibc mitigations like stack canaries, ASLR, and modern mitigations make full remote code execution *hard*, but denial of service is very real.
Official References and Read More
- CVE record: CVE-2024-2961
Upstream bug report:
glibc patch:
Debian Security Advisory:
OSS-Sec Discussion:
oss-security mailing list post
Update glibc to version 2.40 or latest patched backports.
- If you can’t upgrade yet, avoid using ISO-2022-CN-EXT conversions or validate all input/output buffer handling, but note that a clean fix is a library upgrade.
Conclusion
If you rely on GNU glibc and handle any kind of character set conversion, update your systems now. Bugs like CVE-2024-2961 are subtle and can be easily overlooked but pose real risks in software that needs to be secure and reliable. Check your code, keep your libc updated, and stay safe!
Did you find this guide helpful? Check the references above for deep-dive details or share your experience with this CVE below!
Timeline
Published on: 04/17/2024 18:15:15 UTC
Last modified on: 07/03/2024 01:53:40 UTC