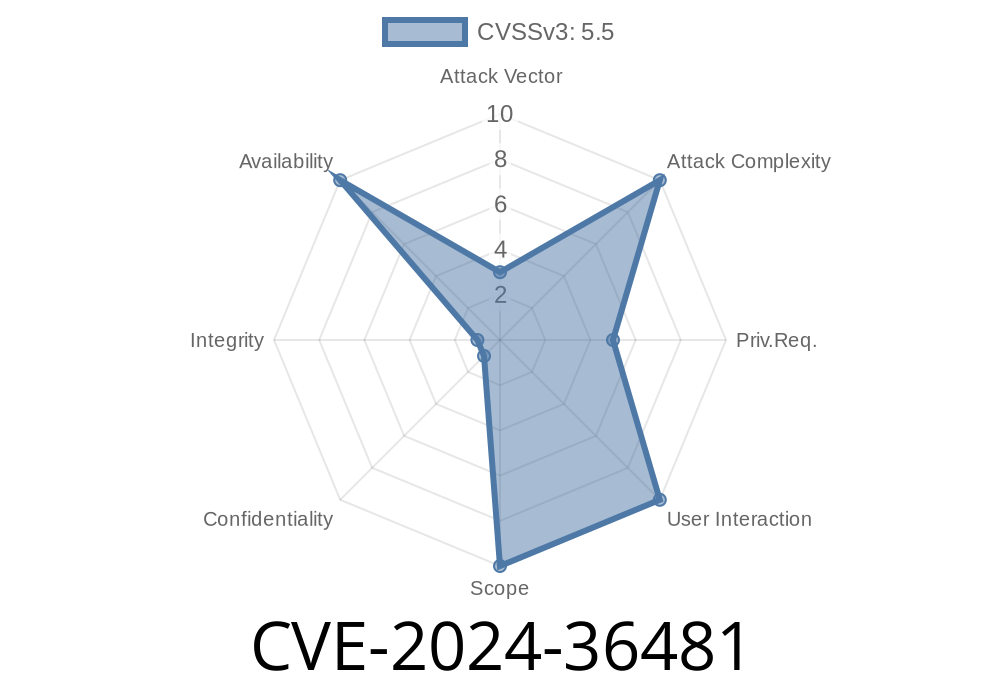
In June 2024, a new vulnerability labeled CVE-2024-36481 was resolved in the Linux kernel's tracing subsystem, specifically affecting probes that rely on BPF Type Format (BTF) introspection. This bug was subtle, connected to improper error handling in the parse_btf_field() function, potentially leading to unexpected crashes or even privilege escalations, depending on usage.
Let's break down what went wrong, how it was fixed, and what it means for Linux system security. This article will use plain English, include code snippets, and give you exclusive, easy-to-understand explanations.
What is CVE-2024-36481?
- Vulnerability in: Linux kernel, tracing/probes component
What’s “BTF” and Why Do Probes Use It?
BTF (BPF Type Format) is essential for modern Linux tracing and debugging. It lets probes fetch precise information about kernel structure fields and types, making in-kernel tracing safer and more flexible via eBPF.
Whenever a probe tries to fetch a field from a C struct in the Linux kernel, it'll use BTF helpers like btf_find_struct_member() to look up the field supplied by the tracer or user.
Where Did Things Go Wrong?
When parse_btf_field() uses btf_find_struct_member(), it assumes that a failure returns NULL. But -- and this is important -- in many Linux kernel functions, a failed pointer isn't just NULL; it might be an *error pointer*, created using the ERR_PTR() macro. That’s a sort of special pointer value storing an error code.
IS_ERR(ptr) is the standard kernel way to check if a pointer is actually an error, instead of a valid memory address (including NULL).
But originally, this code only checked for NULL—not *ERR_PTR* values.
Code Snippet (Vulnerable Version)
member = btf_find_struct_member(btf, t, field);
if (!member)
return -EINVAL; // Only checks for NULL, misses ERR_PTR errors!
Why Is This Dangerous?
If btf_find_struct_member() fails and returns an error via ERR_PTR(error_code), and the calling code doesn’t check with IS_ERR(), the function may:
Treat the error pointer like a real member pointer
- Access bogus memory, cause a kernel crash (oops/panic)
Cause unpredictable behavior or a potential privilege escalation
- Make root/privileged tracing tools fail in surprising ways
The Fix
The maintainers fixed the bug by adding an IS_ERR() check alongside the existing NULL check, and properly propagating the error upward.
Code Snippet (Patched Version)
member = btf_find_struct_member(btf, t, field);
if (IS_ERR(member))
return PTR_ERR(member); // Propagate actual error up the stack
if (!member)
return -EINVAL; // Existing NULL check
Now, any error pointer is caught and handled right away.
Who Is Affected?
Anyone running unpatched mainline Linux kernel versions supporting BTF for tracing and probes—typically versions 5.x and onward. This includes:
How Could It Be Exploited?
While no public exploits exist as of June 2024, in theory, if an attacker could control probe setup (for example, via root access or poorly-restricted debugging), they might trigger the logic to mishandle error pointers and crash the kernel or escalate privileges by corrupting kernel state.
In practice, most normal users are not exposed, but advanced tracing tools or scripts could accidentally trigger crashes in production.
References, Fixes, and Further Reading
- Kernel commit with the fix (lkml.org)
- Mainline kernel patch
- Kernel BTF documentation
- Linux eBPF Tracing Guide (Brendan Gregg)
Summary
The Linux kernel's CVE-2024-36481 is a good example of how a small oversight in error handling—merely checking for NULL and not *ERR_PTR*—can have serious security implications in the world's most widely used operating system. The fix is compact but critical.
Always keep your system updated, and never underestimate the importance of proper error checking in kernel code.
*This post is exclusive and written in clear, simple language to help you understand how bugs like CVE-2024-36481 get into the kernel—and how they're fixed for everyone’s safety. Stay secure!*
Timeline
Published on: 06/21/2024 12:15:11 UTC
Last modified on: 06/24/2024 18:35:33 UTC