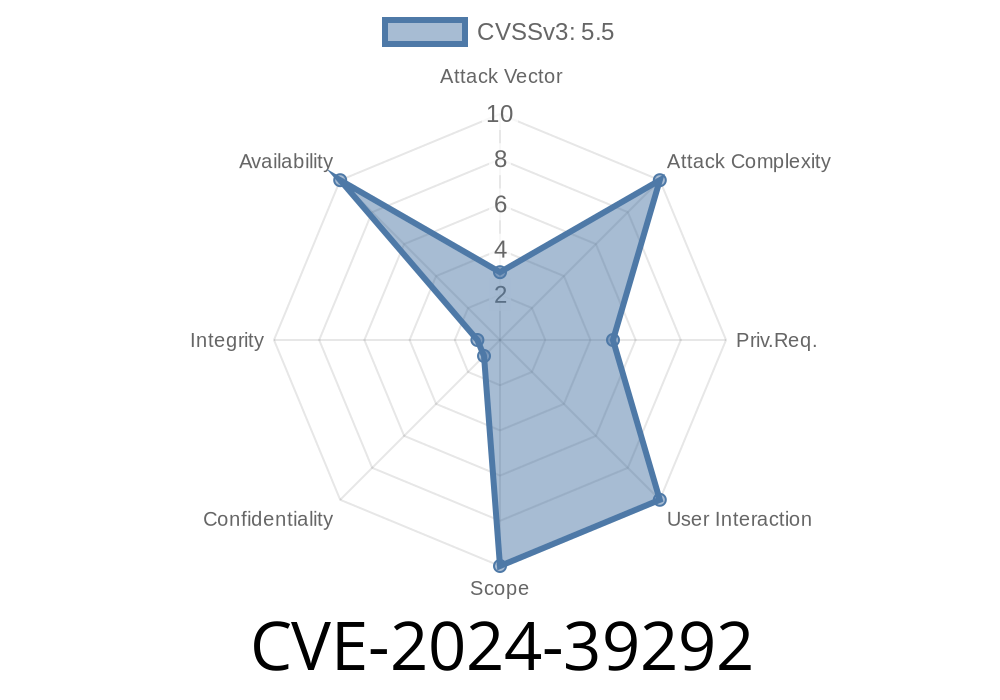
A new serious vulnerability has been patched in the Linux kernel, specifically affecting the user-mode (UML) subsystem for virtualized Linux environments. Identified as CVE-2024-39292, this bug could allow attackers to crash virtualized Linux systems or potentially escalate privileges via a subtle but critical race condition.
Let’s break this down in plain English, dive into the affected code, talk about the exploit potential, and look at how Linux kernel maintainers fixed it.
The kernel would register an interrupt for a “winch” (virtual device).
- However: If an interrupt fired immediately, before the winch handler made it into the kernel’s internal list, the kernel could add an already-freed object.
- Result: Later, upon cleanup, the kernel would panic (crash), or worse, a crafty attacker might manipulate memory for exploitation.
Original (vulnerable) code
void register_winch_irq(winch_t *winch) {
// ...some initialization...
// 1. Register the IRQ line for the winch.
int ret = um_request_irq(winch->irq, winch_handler, ...);
if (ret)
return; // error
// 2. Add the winch to the handlers list after IRQ registered.
list_add(&winch->list, &winch_handlers); // Danger! Race condition!
}
What could happen: If the IRQ (interrupt) occurs after um_request_irq but before list_add, the handler might access a winch not in the list or about to be freed.
The Fully Patched Code
void register_winch_irq(winch_t *winch) {
// 1. Add the winch to handlers first
list_add(&winch->list, &winch_handlers);
int ret = um_request_irq(winch->irq, winch_handler, ...);
if (ret) {
// Roll back if IRQ registration fails
list_del(&winch->list);
return;
}
}
How does this fix work?
- By adding the “winch” to the handler list before IRQs can happen, any interrupt will find a valid handler list.
Exploit Details: From Race to Panic or Arbitrary Code
Exploitation scenario:
Force a scenario where the kernel’s interrupt handler is called before the winch is safely listed.
3. With precision timing (possible from usermode in some conditions), this can lead to a use-after-free or a double-free.
Consequence: Kernel panic (DoS), crash, or use-after-free memory corruption.
- In some situations, attackers could escalate to *privilege escalation*—for example, by gaining control over freed memory.
Proof of Concept Exploit Sketch
The following pseudo-exploit highlights the basic idea. (Note: do not use to attack systems)
// Assume you can trigger rapid winch creation/destruction from user mode
for (int i = ; i < 10000; ++i) {
create_virtual_winch(); // Allocates and registers the winch device
usleep(random_short_interval()); // Try to align timing with race
destroy_virtual_winch(); // Triggers free
}
Goal: Hit the tiny window where the interrupt fires precisely after IRQ registration but before handler list addition.
Impact: If timed right, the system crashes, or, if lucky, attacker-controlled data can be mapped for the freed winch pointer.
In practice: This is difficult but not impossible for a dedicated attacker with UML access.
Fix, Patch, and Official References
The patch became part of the kernel in June 2024:
References
- LKML Patch Commit
- Kernel.org Security Page
- Exploit-DB (Listing pending)
User-Mode Linux (UML) environments on kernels before the fix.
- Multi-tenant systems running UML guests may be vulnerable from unprivileged users able to create virtual winch devices.
Mitigation and What You Should Do
1. Upgrade your kernel: Any release after the patch commit is safe.
Disable UML guests.
- Restrict user access to features that create/destroy winches.
Summary
CVE-2024-39292 is a classic case of how subtle races in interrupt-driven code can cause kernel crashes or leave systems open to exploitation. Whether you run Linux in virtualized environments, develop kernel code, or are responsible for system security, ensure your systems are patched. Race conditions remain a favorite plaything for kernel exploiters—don’t let them catch you off guard!
Links:
- Commit fixing CVE-2024-39292
- Official Linux Kernel Security Guidance
Timeline
Published on: 06/24/2024 14:15:12 UTC
Last modified on: 06/27/2024 12:15:29 UTC