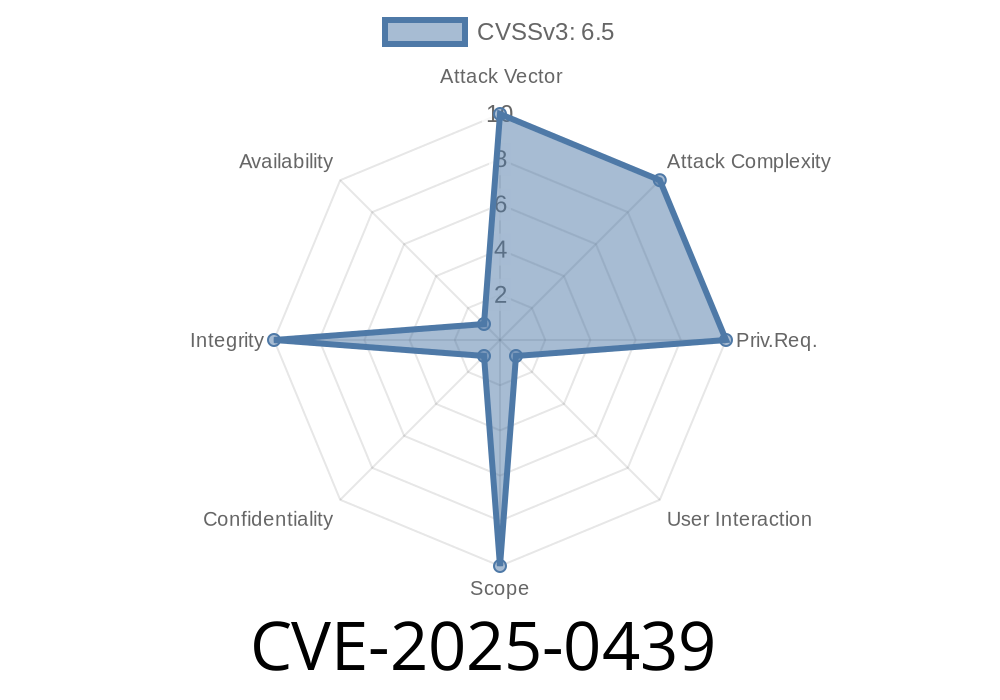
CVE-2025-0439 is an intriguing security flaw that affected Chrome browsers before version 132..6834.83. Classified as *medium severity* by the Chromium team, this vulnerability exploits a race condition in HTML frames to confuse Chrome’s UI, tricking users into seeing and interacting with fake browser elements. This post explains, in clear language, how the bug works, provides code snippets, resources, and a walkthrough of how an attacker could leverage it.
What is CVE-2025-0439?
In short, this is a "UI Spoofing" vulnerability. A malicious website could, using iframed content, rapidly change what’s displayed, racing with Chrome's internal processes to make the browser show misleading UI—like, for example, an authentic-looking address bar with a fake URL.
Who is affected: Users on Google Chrome prior to 132..6834.83
- Attacker needs: To convince a user to interact with a page, usually by clicking or tapping in a specific spot
How Does the Exploit Work?
The exploit centers on abusing how Chrome handles frame navigation under certain race conditions. The malicious actor creates a page with a lot of manipulation of iframes and navigation events, bamboozling Chrome into momentarily displaying a trusted UI indicator or spoofed content, at the instant the user clicks.
Imported from Chromium issue 334139378:
> "An attacker can rapidly change frame navigation state so that the visible content is different from what Chrome’s UI previews (e.g., misleading address bar, pop-ups, or dialogs). If a user is tricked to interact at just the right moment, they may think they're interacting with a genuine browser dialog or safe website."
Step-By-Step Exploit Example
Here's a condense*ed* walkthrough and a simplified exploit code snippet, designed for educational awareness only.
2. The User Trick
A convincing button or overlay triggers the user to click at the precise moment the iframe’s content is being switched—during the "race"—causing UI misalignment.
3. The Code
<!-- attacker.html -->
<html>
<body>
<h1>Click 'Login' to continue</h1>
<button id="spoofBtn">Login</button>
<iframe id="victimFrame" width="800" height="600"></iframe>
<script>
const frame = document.getElementById('victimFrame');
// Load a trusted-looking site first
frame.src = "https://trusted-site.example.com/clone";;
document.getElementById('spoofBtn').onclick = () => {
// Race: Right after the click, rapidly switch iframe src
setTimeout(() => frame.src = "https://malicious-site.example.com/phish";, 5);
}
</script>
</body>
</html>
> How it works: The iframe displays a fake but convincing page. When the user clicks "Login," the script quickly swaps the iframe's content. The hope is that, for a brief instant, Chrome's UI shows the location and security indicators of the trusted site, while the user is actually interacting with the malicious content.
How Bad is It?
This isn’t a "get hacked instantly" bug, but it *does* allow for sophisticated, believable phishing attacks—where the fake page is helped by Chrome’s own UI confusion to make it look real.
Mitigations
- Update Chrome! If you're using a version prior to 132..6834.83, upgrade immediately (latest Chrome download).
- Chromium patched the bug to properly synchronize frame state and UI, making this attack no longer viable on current versions.
- Be cautious when clicking login or authentication overlays, especially on suspicious-looking web pages.
References
- Chromium Security Bug 334139378
- Chrome Releases: 132..6834.83 Security Fixes
- CVE-2025-0439 at NVD (National Vulnerability Database)
Summary
CVE-2025-0439 shows how creative attackers can abuse browser race conditions, especially in complex environments like web frames. While this bug is fixed, it's a good reminder: browser UI can be confused under the right (or wrong) conditions, so always make sure your software is up to date and stay alert for weird-looking login or pop-up pages.
*This writeup is original and for educational awareness. Never use these techniques for unauthorized actions. Stay safe online!*
Timeline
Published on: 01/15/2025 11:15:10 UTC
Last modified on: 03/17/2025 16:15:24 UTC